A fully operational TheGentlemen ransomware toolkit on an exposed server, revealing victim credentials, ngrok tokens, and a complete pre-encryption playbook.
This led them to an unauthenticated HTTP server at 176.120.22[.]127:80, hosted by Russian bulletproof provider Proton66 OOO, exposing 126 files across 18 subdirectories and about 140 MB of data.
Proton66 has previously been tied to SuperBlack ransomware, WeaXor, and XWorm operations, underscoring its role in supporting ransomware-as-a-service ecosystems.
On March 12, 2026, Hunt.io analysts discovered an exposed open directory on Proton66 in CyberXTron’s playbook on TheGentlemen and searched their open-directory dataset.
The directory was first seen roughly three weeks before analysis and remained live until late February 2026, suggesting active, recent use rather than abandoned infrastructure.
What was exposed on the server
The open directory was not a random malware dump but a structured, maintained toolkit aligned with each phase of a ransomware intrusion.
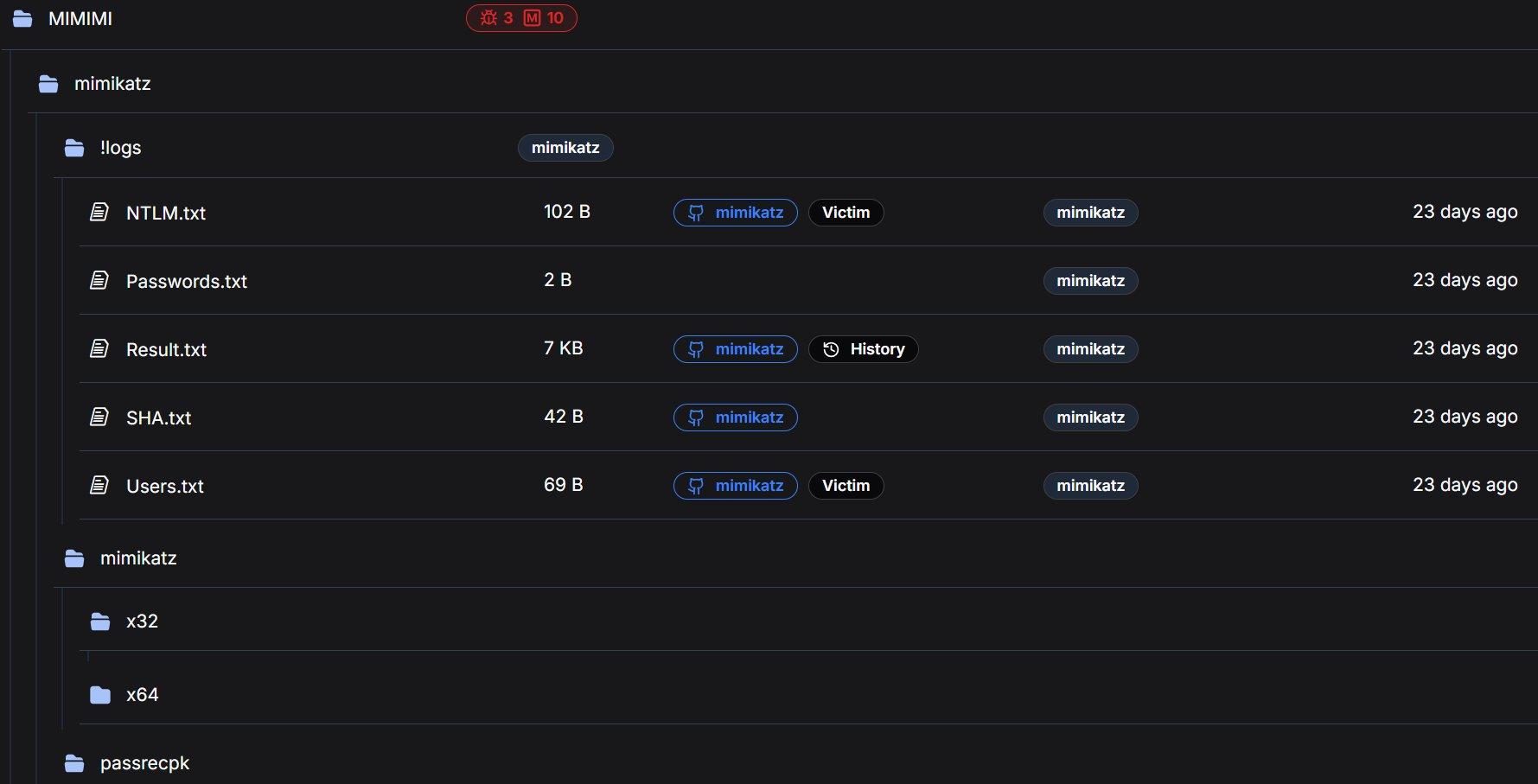
Key folders included a 64-bit_new directory with core tools for 64‑bit Windows, a PowerRun subfolder for privilege escalation, and a “MIMIMI” directory containing Mimikatz infrastructure and logs.
Root-level binaries included multiple PC Hunter and PowerTool builds, RustDesk remote access, ngrok, and utility tools like 7‑Zip, together weighing around 120 MB.
Hunt.io’s automated analysis classified all examined scripts as malicious, mapping them to 21 MITRE ATT&CK techniques spanning reconnaissance, privilege escalation, defense evasion, credential theft, lateral movement, persistence, and pre-encryption preparation.
The most sensitive evidence came from the MIMIMI/mimikatz/!logs directory, which stored live credential output from previous compromises.
Log files contained NTLM password hashes, usernames, and other credential artifacts, proving that the toolkit had already been used against real victims.
Alongside these logs, Hunt.io identified two ngrok authentication tokens hardcoded in configuration files and scripts, exposing the operators’ tunnel access to additional infrastructure.
These ngrok tokens could allow defenders and law enforcement to trace or even disrupt the group’s remote access channels if acted on quickly. The combination of credential logs and tokens effectively links the toolkit to active operations instead of theoretical capability.
The z1.bat “one-click” pre‑encryption weapon
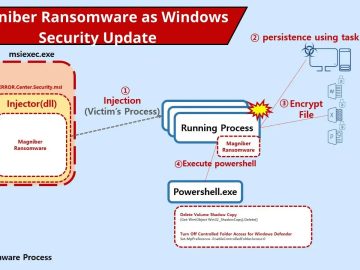
At the heart of the toolkit is z1.bat, a 35 KB batch script designed as a single-execution pre‑ransomware deployment engine.
Our automated analysis classified every analyzed script as Malicious, with categories spanning Exploit (scripts that alter security settings and escalate privileges) and Config (scripts containing sensitive authentication tokens).
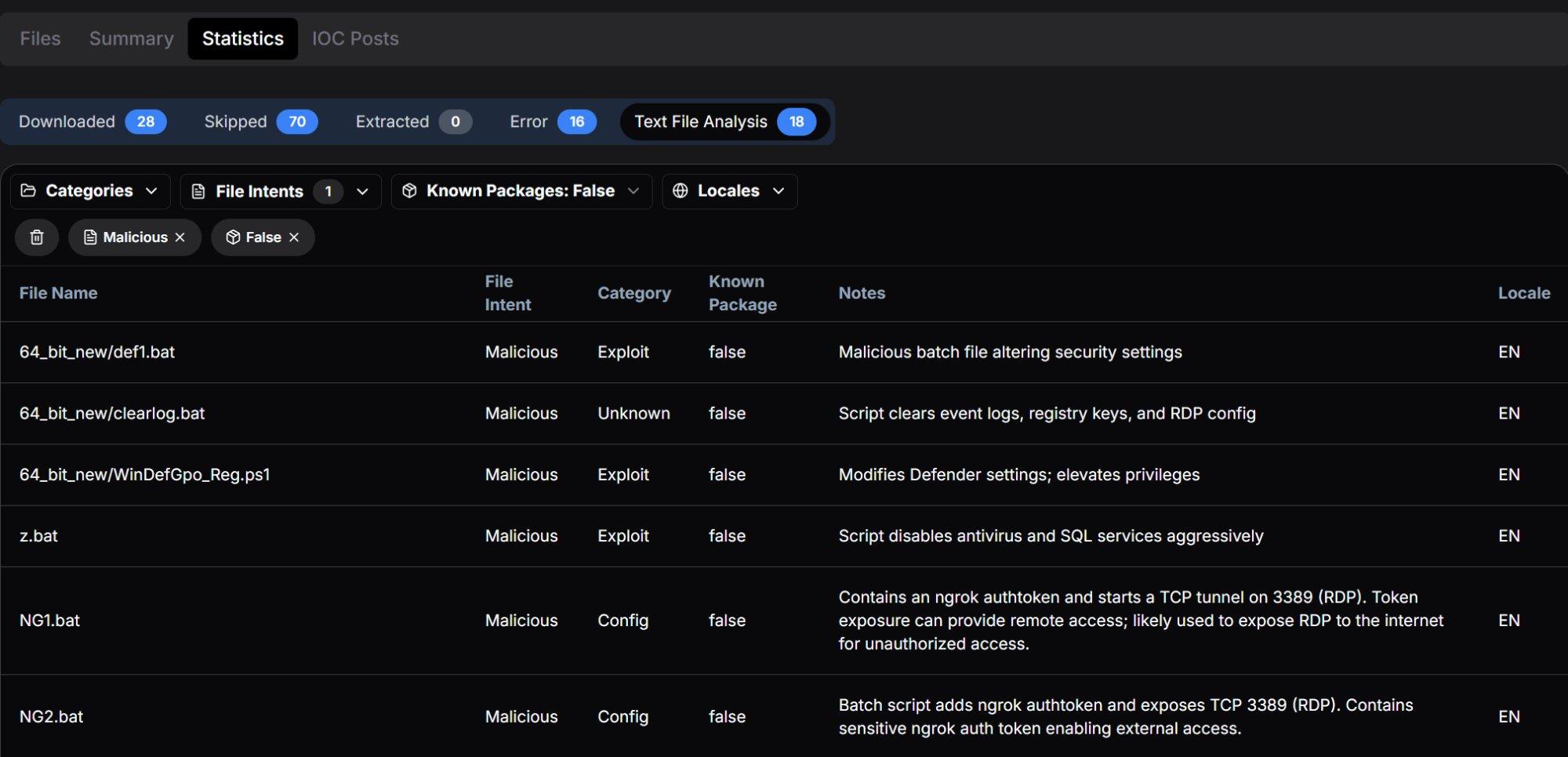
The script chains multiple phases: it deletes and turns off services for dozens of security products, database engines, backup tools, Hyper‑V, Exchange, and other enterprise applications to remove file locks and protection.
It aggressively disables Windows Defender through registry changes, policy tweaks, and task manipulation, and then clears Defender logs and scan history to erase evidence. z1.bat also creates wide-open SMB shares (granting Everyone full access on multiple drive letters) to maximize ransomware propagation across the environment.
Finally, it wipes Windows event logs, RDP history, and the Recycle Bin, implementing a thorough anti‑forensics step before any encryption payload is launched.
The exposed Proton66 server offers a rare, end-to-end view of how a TheGentlemen affiliate prepares victims for ransomware deployment.
Tools like PowerRun, PC Hunter, Defender Control, and heavily modified Defender-kill scripts highlight the group’s focus on reliably bypassing endpoint defenses at scale.
The presence of real victim credentials, ngrok tokens, and a mature pre-encryption script indicates that this toolkit is not experimental but part of ongoing campaigns.
Organizations are advised to monitor for Proton66 infrastructure, ngrok-based tunnels, and the specific service and registry manipulation patterns documented in Hunt.io’s analysis and CyberXTron’s playbook.
Rapid rotation of credentials, hardening of RDP, strict control over remote tunneling tools, and aggressive detection of bulk service-stopping behavior can help detect and disrupt similar toolkits before encryption begins.
Indicators of Compromise
| Type | Value |
|---|---|
| IP Address | 176.120.22[.]127 |
| Port | 80 (HTTP) |
| Hosting Provider | Proton66 OOO (AS198953) |
| Country | Russia |
| Ngrok Token 1 | 2gkRUQNkJyaGkvuDziSq1RGIrwl_4bGyJtv6ez2Hk8Hrd5zvq |
| Ngrok Token 2 | 2ozoAve91tpILCwKCbRDNz7us8e_2qLk1aLKZoV4Y6TfrcfjK |
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.