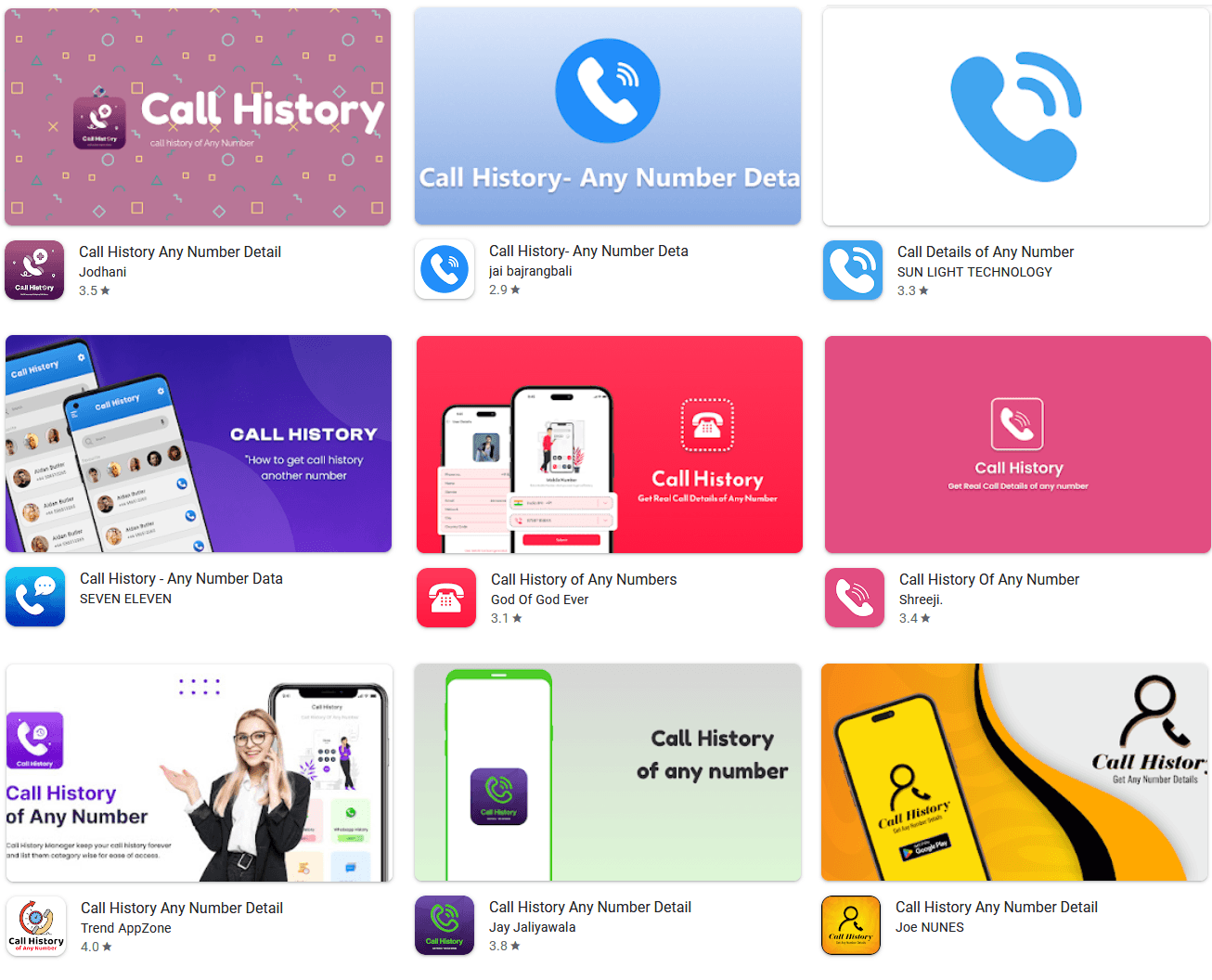
28 fake “call history” utilities on Google Play, collectively installed more than 7.3 million times, have been exposed as subscription scams that generate fabricated logs instead of real phone records, with several also bypassing Google’s official billing system to make refunds harder for victims.
The CallPhantom apps advertise an impossible service: detailed call histories, SMS records, and even WhatsApp call logs “for any phone number” supplied by the user.
One of the first samples flagged, “Call History of Any Number,” was even published under the misleading developer name “Indian gov.in,” despite having no connection to any government entity.
Once installed, the apps prompt users to enter a target phone number and then lock the supposed results behind a paywall, often framed as a weekly, monthly, or annual subscription.
Security researchers at ESET, who tracked the scheme under the name CallPhantom, reported all 28 apps to Google; the company has since removed them from the Play Store.
In reality, the apps have no technical capability to access telecom records or WhatsApp logs, and they never request the sensitive permissions needed to read the device’s call history or SMS data.
Fake Call History Apps on Google Play
ESET’s analysis shows that the “results” screens are driven entirely by hardcoded templates and random generators rather than any back‑end lookup.
In one cluster of apps, the code bundles fixed lists of names, country codes, timestamps, and call durations, which are combined with randomly generated numbers and then displayed as partial “sample” records before the user is asked to pay to unlock the full fake history.
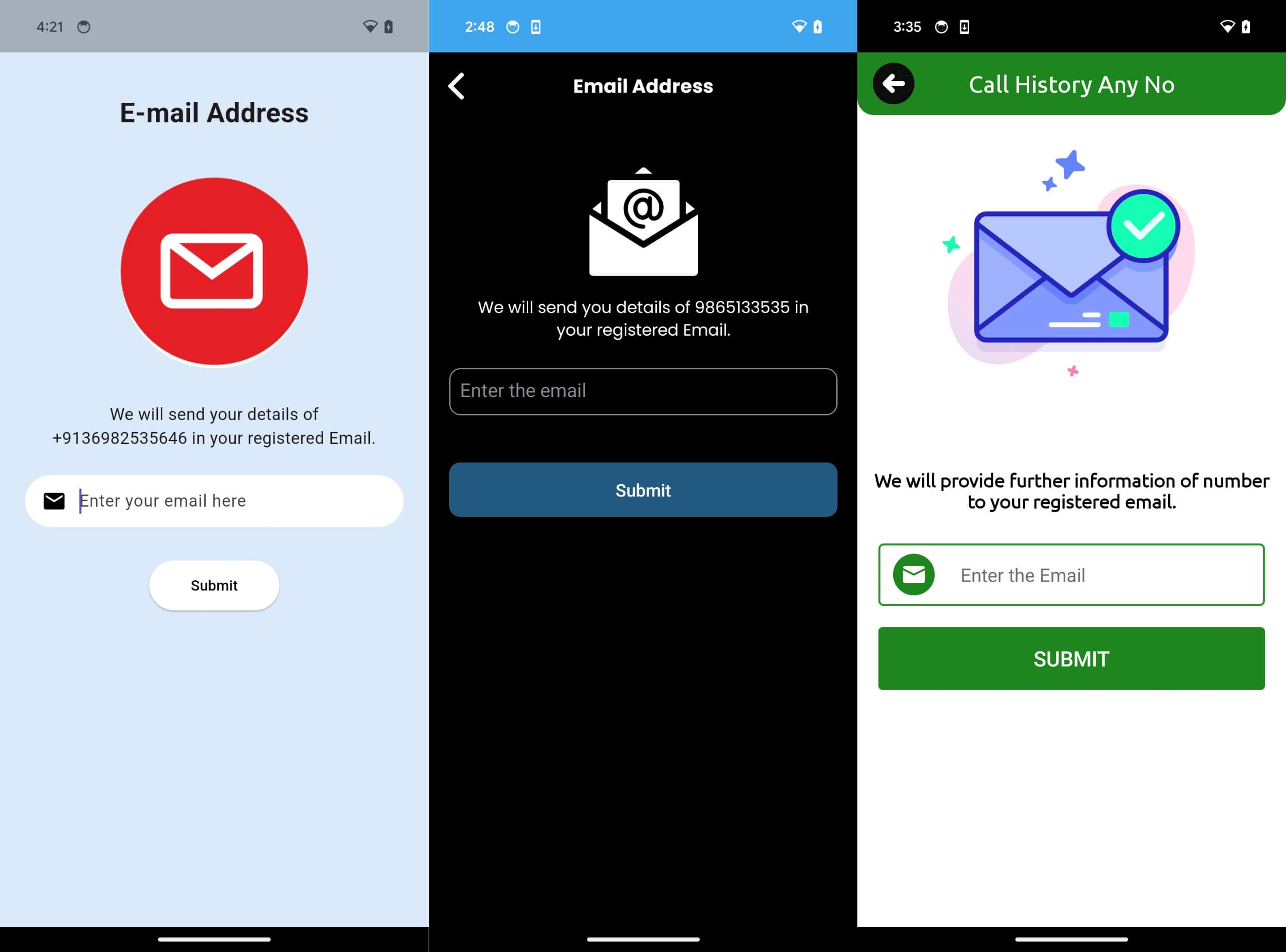
A second cluster collects an email address and promises to send the full report there once a subscription is purchased, but the generation of the fabricated logs only occurs after payment.
In both cases, there is no network request to any telecom operator or messaging service and no logic that could interface with legitimate call‑detail records.
To push hesitant users over the line, one variant even abuses fake system‑style notifications: if the user closes the app without paying, it displays alerts styled as new email messages claiming that the call history report has arrived, and tapping the notification takes the victim straight back to a subscription screen.
The campaign primarily targets users in India and the wider Asia‑Pacific region, with many apps preselecting India’s +91 country code and integrating UPI‑based payment flows that are popular in the country.
Store listings mixed obviously fake promises with polished marketing and a combination of fraudulent positive reviews and angry one‑star ratings from victims who paid and received nothing but random data.
ESET observed three payment paths across the 28 apps. Some used Google Play’s in‑app billing as required by policy, which at least brings standard subscription management and potential refund protections through Google.
Others pushed users to pay via third‑party UPI apps, using hardcoded or remotely configurable URLs hosted in a Firebase Realtime Database so that the operators could rotate receiving accounts at will.
A third set of embedded card‑payment forms directly in the app, with both the UPI redirection and direct card collection running afoul of Google Play’s payment rules and leaving victims dependent on external providers for any redress.
Google has removed all 28 identified CallPhantom apps from Google Play after receiving ESET’s report, and existing Play‑billing subscriptions associated with them have been cancelled.
Users who paid through Google Play may still be able to request refunds, subject to Google’s standard time windows and refund criteria, via the subscription management and refund request options documented in its support pages.
Those who entered card details in‑app or paid through third‑party UPI apps face a harder path: Google cannot cancel or refund these off‑platform transactions, so victims must instead contact their bank, card issuer, UPI provider, or – where possible – the listed developer.
ESET recommends that users avoid any app claiming to reveal call logs, SMS records, or messaging histories for arbitrary numbers, as such access is not available through legitimate consumer apps and should be treated as a red‑flag sign of a scam.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.






