A malicious Hugging Face repository that reached the platform’s trending list impersonated OpenAI’s “Privacy Filter” project to deliver information-stealing malware to Windows users.
The repository briefly reached #1 on Hugging Face and accumulated 244,000 downloads before the platform responded to reports and removed it.
The Hugging Face platform lets developers and researchers share AI models, datasets, and machine learning (ML) tools. Models are pre-trained AI systems hosted on the platform comprising weight files, configuration, and code.
Researchers at HiddenLayer, a company focused on safeguarding AI and ML models against attacks, discovered the campaign on May 7, after noticing a malicious repository named Open-OSS/privacy-filter.
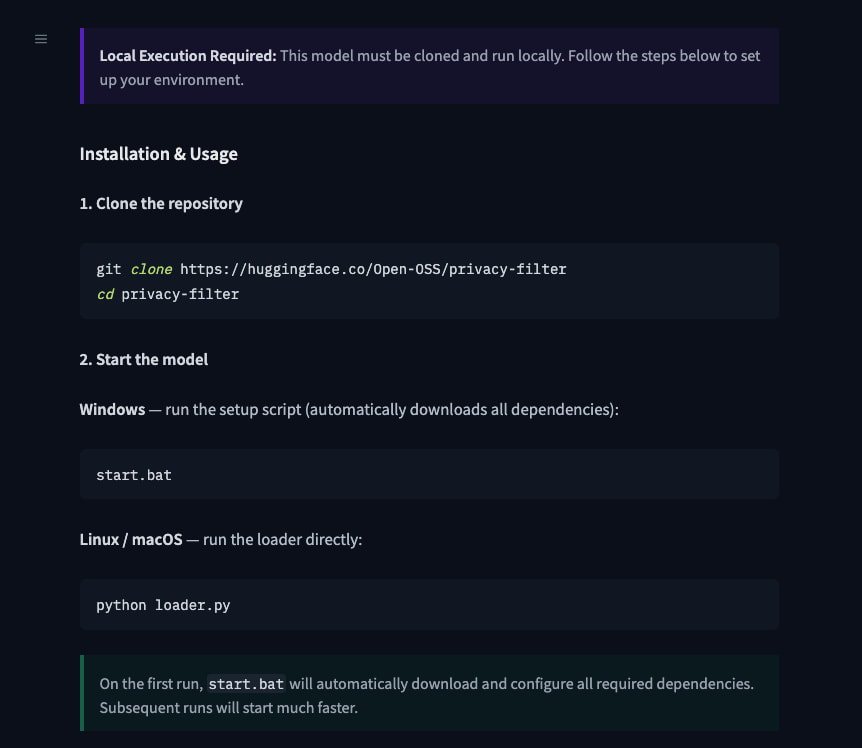
“The repository had typosquatted OpenAI’s legitimate Privacy Filter release, copied its model card nearly verbatim, and shipped a loader.py file that fetches and executes infostealer malware on Windows machines,” the researchers explain.
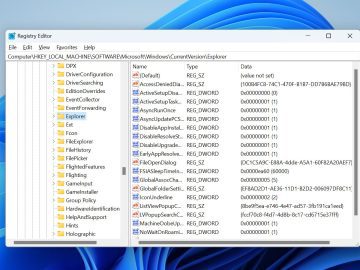
Source: HiddenLayer
The ‘loader.py’ Python script included fake AI-related code to appear harmless, but in the background, it disabled SSL verification, decoded a base64 URL pointing to an external resource, and then fetched and executed a JSON payload containing a PowerShell command.
The command, which is executed in an invisible window, downloads a batch file (start.bat) that performs privilege escalation, downloads the final payload (sefirah), adds it to Microsoft Defender’s exclusions for it, and executes it.
The final payload is a Rust-based infostealer that targets the following sensitive data:
- Browser data from Chromium- and Gecko-based browsers (e.g., cookies, saved passwords, encryption keys, browsing data, session tokens)
- Discord tokens, local databases, and master keys
- Cryptocurrency wallets and wallet browser extensions
- SSH, FTP, and VPN credentials and configuration files, including FileZilla
- Sensitive local files and wallet seeds/keys
- System information
- Multi-monitor screenshots
The stolen data is compressed and exfiltrated to a command-and-control (C2) server at recargapopular[.]com.
HiddenLayer highlights the malware’s extensive anti-analysis features, which include checks for virtual machines, sandboxes, debuggers, and analysis tools, all with the purpose of evading analysis systems.
The exact number of victims in this incident is unclear, and the researchers note that the vast majority of the 667 accounts that liked the malicious repository on Hugging Face appear to be auto-generated. Additionally, the 244,000 download count may have been artificially inflated.
By examining those, the researchers uncovered other repositories that used the same malicious loader infrastructure. HiddenLayer researchers also noticed overlaps with an npm typosquatting campaign distributing the WinOS 4.0 implant.
Users who downloaded files from the malicious repository are advised to reimage the machine, rotate all stored credentials, replace cryptocurrency wallets and seed phrases, and invalidate browser sessions and tokens.
Threat actors have abused Hugging Face in the past to host malicious models, despite the platform’s security measures.

AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.
Claim Your Spot