Software developers working on the OpenClaw project are the latest targets of a dangerous phishing campaign designed to empty their digital wallets. The attack, which was recently identified by the research firm OX Security, exploits GitHub’s own notification system to lead unsuspecting users toward a fraudulent website.
The $5,000 Bait
The scam begins on GitHub, where attackers set up fake accounts to open new discussion threads. To reach as many people as possible, they tag dozens of real developers in these posts. This tagging system ensures the victim receives an email or push notification directly, making the message appear like a legitimate part of their daily professional workflow.
Within these threads, the scammers claim that specific developers have been chosen to receive free $CLAW tokens worth $5,000 as a reward for their work. One specific message used by the attackers states: “Appreciate for your contributions on GitHub. We analyzed profiles and chose developers to get OpenClaw allocation.”
As per OX Security’s team research, which was shared with Hackread.com, the link in these posts, which often uses a Google LinkShare address, leads to a site found at token-claw.xyz. This domain is an almost identical clone of the official OpenClaw page.
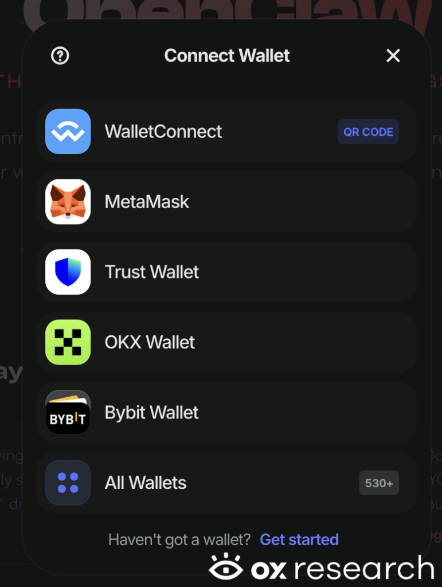
The only major difference here is a ‘Connect your wallet’ button. Researchers noted that the site supports various popular services, including MetaMask, Trust Wallet, OKX, and Bybit. Once a user connects their wallet to claim the prize, the scammers gain the power to drain every asset inside.
Hiding the Trail
We have often seen cybercriminals using complex methods to hide their tracks, and this case is no different, as researchers found a JavaScript file named ‘eleven.js’ containing the malicious instructions. They also identified that the code includes a ‘nuke’ function, which is designed to delete all evidence of the theft from the user’s browser storage to stop experts from tracing the crime later.
According to researchers, the attackers are likely finding their victims by looking at who has starred or interacted with OpenClaw-related projects on GitHub. This makes the lie feel much more believable to the person being tagged.
How to Stay Safe
While there are currently no confirmed victims, the threat actor created multiple accounts last week specifically to spread this campaign. Interestingly, these accounts were deleted just hours after the campaign launched to avoid detection. It is also worth noting that researchers identified a specific wallet address (0x6981E9EA7023a8407E4B08ad97f186A5CBDaFCf5) where the stolen funds are sent.
OX Security experts suggest that any developer who may have interacted with the site should immediately cancel any permissions given to their wallets and block the domain token-claw.xyz. As a general rule, any GitHub issue promoting a surprise giveaway should be treated as a major red flag.