Multiple ongoing malware campaigns are distributing a powerful information-stealing trojan, tracked as NWHStealer, through fake VPN installers, gaming mods, and system tools.
Unlike typical phishing campaigns, these attacks exploit users’ trust in popular software. Threat actors are disguising malicious payloads as legitimate installers for tools such as Proton VPN, OhmGraphite, Sidebar Diagnostics, Pachtop, and HardwareVisualizer.
The files are hosted across multiple channels including fake lookalike domains, GitHub, GitLab, MediaFire, and SourceForge and are often linked from gaming or security-related YouTube videos.
Once executed, NWHStealer infiltrates systems by injecting itself into trusted Windows processes like RegAsm.exe, Microsoft’s Assembly Registration Tool.
Researchers have uncovered a wide-ranging operation that leverages convincing fake websites, developer platforms, and YouTube channels to trick users into downloading and executing the malware.
Depending on the variant, it may use self-injection, DLL hijacking, or MSI-based loaders to deploy the final payload stealthily.
Case 1: Free Hosting Service as Malware
One surprising discovery was a malicious campaign leveraging onworks[.]net, a legitimate free web hosting provider that allows users to run virtual machines in-browser.
Attackers abused this platform to host infected ZIP archives masquerading as legitimate utilities. Downloads named OhmGraphite-0.36.1.zip, Sidebar Diagnostics-3.6.5.zip, and HardwareVisualizer_1.3.1.zip contained executables embedded with malicious loaders.
These loaders contain anti-analysis code, custom AES-CBC decryption routines, and Windows API calls to resolve system functions via LoadLibraryA and GetProcAddress dynamically.
Once decrypted, they load the next stage directly into memory, bypassing traditional endpoint defenses.
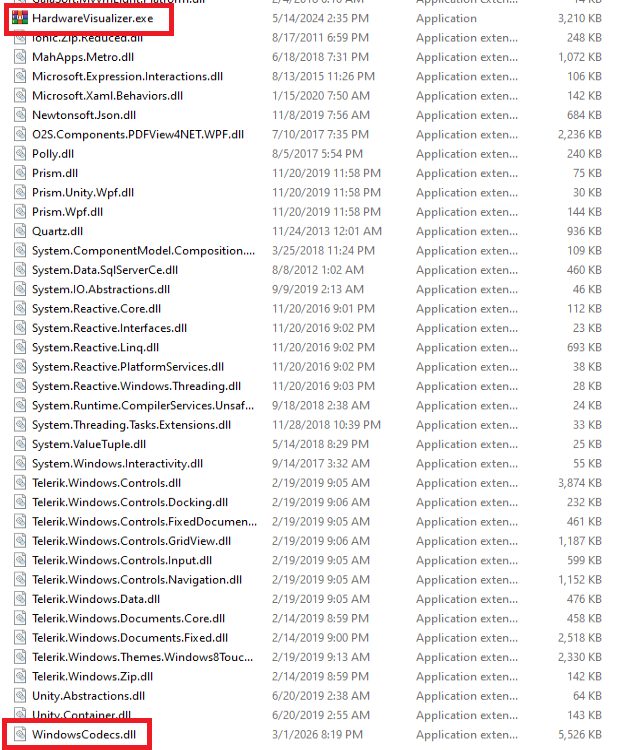
In related samples, the attackers replaced legitimate files with WinRAR executables bundled with malicious DLLs (e.g., WindowsCodecs.dll) to hijack trusted processes.
Case 2: Fake Proton VPN Sites Delivering Malware
A second wave involved fake Proton VPN websites, designed with realistic UIs and bundled ZIP files mimicking official VPN installers.
These archives contained malicious DLLs such as iviewers.dll, TextShaping.dll, and CrashRpt1403.dll that initiate process hollowing in legitimate binaries like RegAsm.
The malware then decrypts embedded resources, loads secondary payloads, and eventually executes NWHStealer in memory.

Researchers also linked this campaign to compromised YouTube channels that feature AI-generated tutorial videos demonstrating the fake installation process and directing viewers to download links.
None of these sites or videos is affiliated with Proton VPN, and the company has been notified of the impersonation.
Once active, NWHStealer systematically enumerates browser data, extracts saved credentials, and targets over 25 directories tied to cryptocurrency wallets.
It operates across major browsers such as Chrome, Edge, Brave, Opera, and Chromium-based variants, injecting a DLL into browser processes to decrypt and exfiltrate stored information.
Data is encrypted with AES-CBC before being sent to the command-and-control (C2) infrastructure. If the main server is inaccessible, the malware retrieves a new C2 address using a Telegram-based dead drop.

DLL into browser processes such as msedge.exe, firefox.exe, or chrome.exe. This DLL extracts and decrypts browser data before sending it to the command-and-control (C2) server.
It also executes PowerShell commands to disable Windows Defender, create hidden folders, and set up scheduled tasks to maintain persistence. To escalate privileges, it uses a known CMSTP UAC bypass technique.
How to Stay Safe
Attackers behind NWHStealer are leveraging software users already trust, making these threats unusually effective. To stay protected:
- Always download software only from official vendor websites.
- Be cautious with tools hosted on GitHub, SourceForge, or file-sharing sites.
- Verify file digital signatures and publisher details.
- Avoid following YouTube links that promise free or “modded” versions of software.
- Use security add-ons like Malwarebytes Browser Guard to block malicious sites.
The growing sophistication of NWHStealer’s distribution shows that even seemingly legitimate software sources can’t always be trusted without careful scrutiny.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.



![Threat Actors Exploit Nifty[.]com Infrastructure in Sophisticated Phishing Attack](https://image.cybernoz.com/wp-content/uploads/2025/05/Threat-Actors-Exploit-Niftycom-Infrastructure-in-Sophisticated-Phishing-Attack.webp.jpeg)


