A newly discovered malware campaign is exploiting user trust in Telegram by distributing a trojanized installer through a typosquatted website, telegrgam[.]com.
The site closely mimics the official Telegram download portal and delivers a malicious executable named tsetup-x64.6.exe, making it appear legitimate to unsuspecting users.
Once downloaded and executed, the installer initiates a multi-stage attack chain while also dropping a legitimate Telegram installer to avoid raising suspicion.
During execution, the installer launches several commands via cmd.exe, including process enumeration. Notably, it searches for specific processes such as 0tray.exe, indicating potential checks for security tools or prior infections.
One of the most critical actions is the modification of Windows Defender settings. The malware executes a PowerShell command to add all system drives (C:, D:, E:, F:) to Defender’s exclusion list.
According to the report, the attack begins with a deceptive domain designed to trick users searching for Telegram downloads. The site visually replicates the official interface, increasing the likelihood of successful infection.
This effectively disables antivirus scanning across the system, allowing the malware to operate undetected.
The installer also creates registry entries that likely act as infection markers, helping the malware identify compromised systems and avoid redundant reinfection.
Payload Staging and Masquerading
The malware drops multiple payload components into the directory:
C:Users
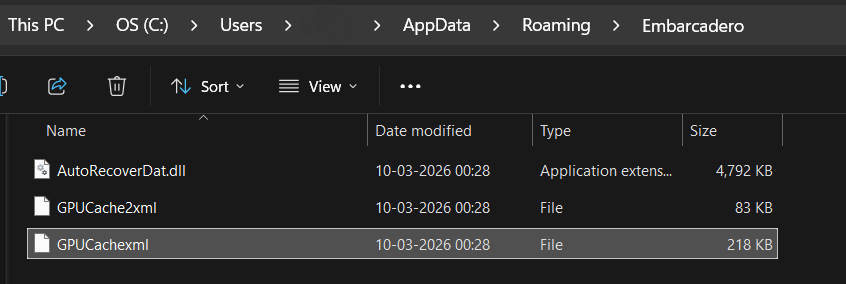
The use of the “Embarcadero” folder name helps the files blend in with legitimate development tools. Additionally, a genuine Telegram installer is deployed at:
C:Program Files (x86)Applicatelegrom.exe
This decoy ensures the user sees Telegram installed, reducing suspicion while malicious processes run in the background.
Instead of containing the payload directly, the DLL reads encoded data from an XML file named GPUCache.xml.
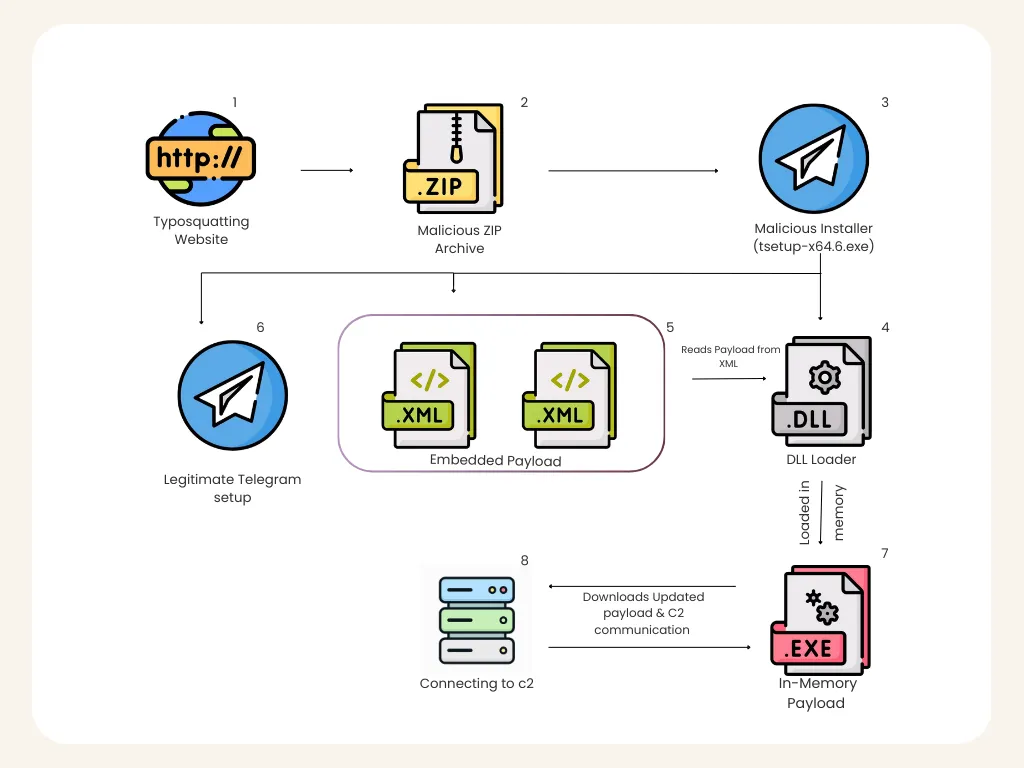
It then reconstructs a Portable Executable (PE) payload at runtime. This payload is never written to disk. Instead, it is loaded directly into memory using reflective loading techniques.
A key component of the attack is the execution of a malicious DLL via rundll32.exe. The DLL, named AutoRecoverDat.dll, exposes the DllRegisterServer export as its entry point. However, it does not behave like a standard COM component.
This approach involves memory allocation, PE mapping, resolving imports, and transferring execution all within a legitimate Windows process.
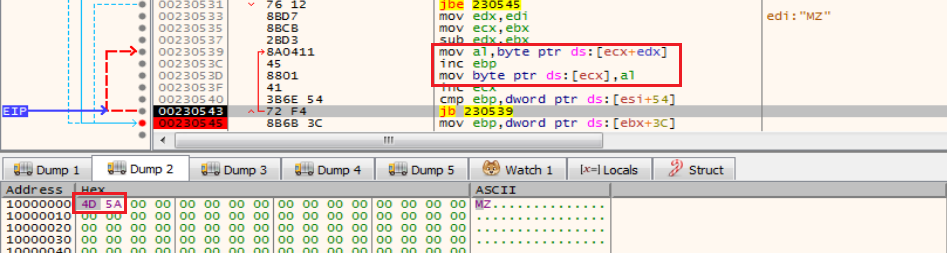
By running inside rundll32.exe, the malware blends into normal system activity and evades traditional file-based detection mechanisms.
Command-and-Control Communication
Once active, the malware establishes a TCP connection to its command-and-control (C2) infrastructure at 27[.]50[.]59[.]77:18852, associated with the domain jiijua[.]com.
This connection allows the attacker to send commands, update payloads, and maintain persistent access.
Network analysis shows that the malware continuously communicates with the C2 server, enabling remote command execution, data exfiltration, and system monitoring behavior commonly associated with advanced loaders or remote access trojans.
The malware also includes a flexible update mechanism. Traffic analysis reveals that it can download updated payload components directly from the C2 server and execute them in memory. This allows attackers to evolve their capabilities without redistributing the original installer.
Overall, this campaign highlights the growing sophistication of loader-based malware, particularly the use of in-memory execution and legitimate system tools to evade detection.
Users are strongly advised to download software only from official sources and verify domain authenticity before installing applications.
IOCs
| MD5 | Detection Name |
| A9A5CC6B6766FEC51B281B94F5F17CCD (tsetup-x64.6.exe) | Trojan(005cea261) |
| 62F8EFFC7690455ABCB300E3574F0A93(Loaded Payload) | Trojan(005d198a1) |
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.