A new Vidar infostealer campaign is abusing fake software download links on YouTube to compromise corporate employees and sell their stolen credentials on Russian cybercrime marketplaces.
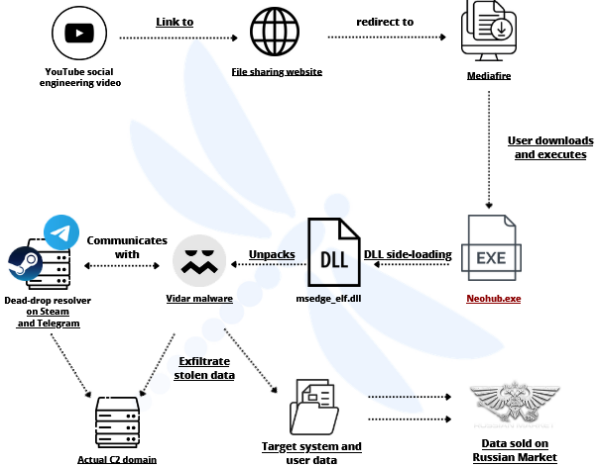
In the investigated case, the victim was searching for software on YouTube and likely followed a link in the video description that led to a third‑party file‑sharing service.
From YouTube, the user appears to have been redirected to filefa.st and then to MediaFire, where a compressed archive posing as a NeoHub installer was hosted and still available at the time of analysis.
The archive contained several files created on 16 October 2025, including NeoHub.exe and a malicious library named msedgeelf.dll.
Because NeoHub.exe looks like a normal Windows application, users are highly likely to run it, believing they are installing a legitimate tool.
The infostealer ecosystem for our annual threat reporting, we noticed that Vidar was the top stealer on the Russian Market marketplace.
Threat researchers observed attackers weaponizing a fake tool called “NeoHub” to lure victims into executing a malicious installer that silently loads the latest Vidar 2.0 stealer.
Technical details of the payload
The msedgeelf.dll file is a 64‑bit Go‑compiled DLL of about 10 MB, packed and obfuscated to hinder static and dynamic analysis.
Inside logs collected by Vidar, the file “information.txt” reveals the domain used to advertise Vidar, which is now vidars[.su.
When executed, the binary imports two key functions from msedgeelf.dll, which is in fact a Vidar sample disguised as a Microsoft Edge component.
Analysts observed unusual section names and the use of classic packer-related imports such as LoadLibrary and GetProcAddress, indicating a custom Go-based packer with control-flow flattening.
The DLL was originally signed with a fake “githab.com” certificate and later re-signed with another fraudulent certificate spoofing “grow.com,” both of which appear on VirusTotal across multiple infostealer samples.
Once unpacked, Vidar exhibits typical stealer capabilities, targeting credentials, cookies, autofill data, and cryptocurrency wallets.
To obtain data on this compromise, which helps detail almost all the aspects of the kill-chain that led to the exfiltration of sensitive data.
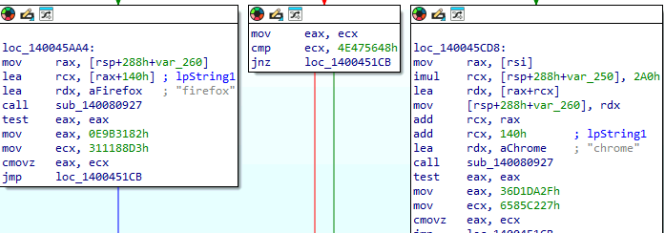
It supports multiple browsers, including Chrome, Edge, Firefox, Opera, Vivaldi, Waterfox, and Pale Moon, and accesses local databases such as Firefox’s key4.db to decrypt stored secrets.
The malware also collects detailed system information and generates an information.txt file summarizing host metadata for operators.
Vidar relies on dead drop resolvers hosted on popular platforms such as Steam and Telegram to retrieve its command‑and‑control (C2) domains dynamically.
In the analysed sample, a Steam profile and a Telegram channel were hardcoded and used to point to a subdomain (gz.technicalprorj.xyz), which then resolved to the real C2 domain gpu.orca-trade.com.
This layered design allows Vidar operators to rotate infrastructure rapidly and hide behind legitimate services that are commonly allowed in corporate networks.
Researchers also mapped an expanding Vidar infrastructure around vidars.su, including related domains like true-v.top, v-new.cloud, my-vidar.ru and vidmn.top hosted across several IP ranges.
An email address using the domain otmail.top, which mimics Hotmail, was linked to multiple Vidar-related domains, further illustrating the use of look‑alike infrastructure.
From stolen logs to corporate impact
Stolen data from this campaign ends up as “logs” sold or shared on Russian Market and Telegram “cloud” channels such as KATANACLOUD and BradMax Cloud, which actively advertise Vidar content.

These channels distribute infostealer logs to a wide range of threat actors, enabling secondary attacks such as VPN hijacking, corporate email compromise, cloud account takeover and financial fraud.
Because the initial lure abuses common user behaviour searching YouTube for cracked or unofficial tools corporate employees are directly exposed even on otherwise well‑secured networks.
Once Vidar exfiltrates browser-stored credentials and cookies, attackers can bypass multi-factor authentication in some scenarios by replaying session cookies or targeting poorly secured internal portals.
Security teams should block the Vidar infrastructure detailed in recent reporting, including domains such as vidars.su, true-v.top, v-new.cloud, my-vidar.ru, getpi.su, get-p.buzz and associated IP addresses.
Network and email security controls should focus on detecting traffic to Steam and Telegram profiles used as dead drop resolvers, as well as suspicious downloads from file-sharing services like MediaFire linked from YouTube or shortener domains.
Enterprises should also harden browser security by limiting password storage, enforcing multi-factor authentication, and monitoring for abnormal login patterns associated with stolen cookies.
Finally, regular awareness training should explicitly cover the risk of installing “free” tools from YouTube links and unofficial file‑sharing sites, as this Vidar campaign shows how easily a single user action can expose corporate credentials at scale.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.