The loader-as-a-service (LaaS) known as FakeBat has become one of the most widespread loader malware families distributed using the drive-by download technique this year, findings from Sekoia reveal.
“FakeBat primarily aims to download and execute the next-stage payload, such as IcedID, Lumma, RedLine, SmokeLoader, SectopRAT, and Ursnif,” the company said in a Tuesday analysis.
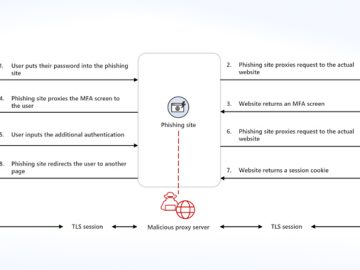
Drive-by attacks entail the use of methods like search engine optimization (SEO) poisoning, malvertising, and nefarious code injections into compromised sites to entice users into downloading bogus software installers or browser updates.
The use of malware loaders over the past few years dovetails with the growing use of landing pages impersonating legitimate software websites by passing them off as legitimate installers. This ties into the larger aspect that phishing and social engineering remain one of the threat actors’ main ways to acquire initial access.

FakeBat, also known as EugenLoader and PaykLoader, has been offered to other cybercriminals under a LaaS subscription model on underground forums by a Russian-speaking threat actor named Eugenfest (aka Payk_34) since at least December 2022.
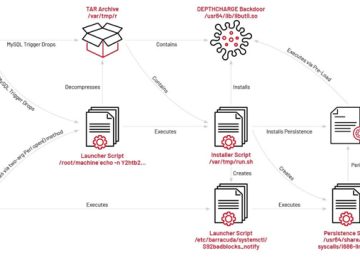
The loader is designed to bypass security mechanisms and provides customers with options to generate builds using templates to trojanize legitimate software as well as monitor installations over time through an administration panel.
While the earlier versions made use of an MSI format for the malware builds, recent iterations observed since September 2023 have switched to an MSIX format and added a digital signature to the installer with a valid certificate to sidestep Microsoft SmartScreen protections.
The malware is available for $1,000 per week and $2,500 per month for the MSI format, $1,500 per week and $4,000 per month for the MSIX format, and $1,800 per week and $5,000 per month for the combined MSI and signature package.

Sekoia said it detected different activity clusters disseminating FakeBat by three primary approaches: Impersonating popular software through malicious Google ads, fake web browser updates via compromised sites, and social engineering schemes on social networks. This encompasses campaigns likely related to the FIN7 group, Nitrogen, and BATLOADER.
“In addition to hosting payloads, FakeBat [command-and-control] servers highly likely filter traffic based on characteristics such as the User-Agent value, the IP address, and the location,” Sekoia said. “This enables the distribution of the malware to specific targets.”
The disclosure comes as the AhnLab Security Intelligence Center (ASEC) detailed a malware campaign distributing another loader named DBatLoader (aka ModiLoader and NatsoLoader) through invoice-themed phishing emails.
It also follows the discovery of infection chains propagating Hijack Loader (aka DOILoader and IDAT Loader) via pirated movie download sites to ultimately deliver the Lumma information stealer.
“This IDATLOADER campaign is using a complex infection chain containing multiple layers of direct code-based obfuscation alongside innovative tricks to further hide the maliciousness of the code,” Kroll researcher Dave Truman said.

“The infection hinged around utilizing Microsoft’s mshta.exe to execute code buried deep within a specially crafted file masquerading as a PGP Secret Key. The campaign made use of novel adaptations of common techniques and heavy obfuscation to hide the malicious code from detection.”
Phishing campaigns have further been observed delivering Remcos RAT, with a new Eastern European threat actor dubbed Unfurling Hemlock leveraging loaders and emails to drop binary files that act as a “cluster bomb” to spread different malware strains at once.
“The malware being distributed using this technique is mostly comprised of stealers, such as RedLine, RisePro, and Mystic Stealer, and loaders such as Amadey and SmokeLoader,” Outpost24 researcher Hector Garcia said.
“Most of the first stages were detected being sent via email to different companies or being dropped from external sites that were contacted by external loaders.”