CISA and the FBI have issued a joint advisory highlighting the increasing threat behind ongoing Royal ransomware attacks targeting many U.S. critical infrastructure sectors, including healthcare, communications, and education.
This follows an advisory issued by the Department of Health and Human Services (HHS), whose security team revealed in December 2022 that the ransomware operation had been linked to multiple attacks against U.S. healthcare organizations.
In response, the FBI and CISA shared indicators of compromise and a list of tactics, techniques, and procedures (TTPs) linked, which would help defenders detect and block attempts to deploy Royal ransomware payloads on their networks.
“CISA encourages network defenders to review the CSA and to apply the included mitigations,” the U.S. cybersecurity agency said on Thursday.
The federal agencies are asking all organizations at risk of being targeted to take concrete steps to protect themselves against the rising ransomware threat.
To safeguard their organizations’ networks, enterprise admins can start by prioritizing the remediation of any known vulnerabilities attackers have already exploited.
Training employees to spot and report phishing attempts effectively is also crucial. Cybersecurity defenses can further be hardened by enabling and enforcing multi-factor authentication (MFA), making it much harder for attackers to access sensitive systems and data.
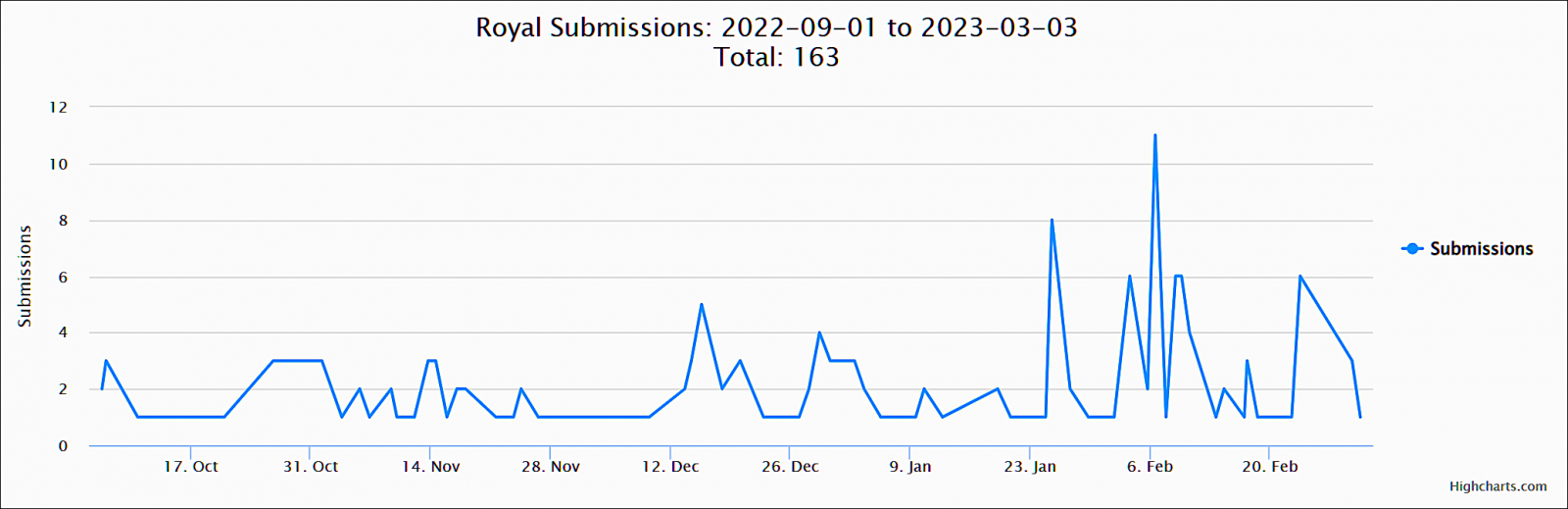
Samples submitted to the ID-Ransomware platform for analysis show that the enterprise-targeting gang has been increasingly active starting late January, showing this ransomware operation’s huge impact on its victims.
Request for Royal incident reports
Even though the FBI says that paying ransoms will likely encourage other cybercriminals to join the attacks, victims are urged to report Royal ransomware incidents to their local FBI field office or CISA regardless of whether they’ve paid a ransom or not.
Any additional information will help collect critical data needed to keep track of the ransomware group’s activity, help stop further attacks, or hold the attackers accountable for their actions.
Royal Ransomware is a private operation comprised of highly experienced threat actors known for previously working with the notorious Conti cybercrime gang. Their malicious activities have only seen a jump in activity since September, despite first being detected in January 2022.
Even though they initially deployed encryptors from other operations like BlackCat, they have since transitioned to using their own.
The first was Zeon, which generated ransom notes similar to those used by Conti, but they switched to a new encryptor in mid-September after rebranding to “Royal.”
The malware was recently upgraded to encrypt Linux devices, specifically targeting VMware ESXi virtual machines.
Royal operators encrypt their targets’ enterprise systems and demand hefty ransom payments ranging from $250,000 to tens of millions per attack.
This ransomware operation also stands out from the crowd due to its social engineering tactics to deceive corporate victims into installing remote access software as part of callback phishing attacks, where they pretend to be software providers and food delivery services.
In addition, the group employs a unique strategy of utilizing hacked Twitter accounts to tweet out details of compromised targets to journalists, hoping to attract news coverage and add further pressure on their victims.
These tweets contain a link to leaked data, which the group allegedly stole from the victims’ networks before encrypting them.