Feiniu fnOS network-attached storage (NAS) devices have been pulled into a large Netdragon botnet after attackers exploited still-unpatched vulnerabilities, turning home and small‑business storage into infrastructure for DDoS attacks.
The malware opens an HTTP backdoor on port 57132, letting attackers run arbitrary system commands remotely via crafted GET requests to the /api path.
Using traffic fingerprints from this backdoor and asset‑mapping data, analysts identified signs of compromise on more than 1,000 IP addresses, all tied to Feiniu devices, with no evidence of other vendors being affected.
Researchers observed malicious code implanted on Internet‑exposed Feiniu NAS devices running fnOS, confirming the samples belong to the Netdragon malware family first seen in October 2024.
By late January, C2 telemetry suggested the botnet had grown to roughly 1,500 infected Feiniu NAS nodes, with over 1,100 bots simultaneously online in one control‑panel snapshot.
Netdragon Botnet Attack
Netdragon aggressively attacks the defenses of infected devices by dismantling logs, updates, and recovery paths.
Regarding the scale of the infection, based on XLAB Global Hawk asset mapping and the C2 control data we have, netdragonthe botnet.
The loader component wipes extensive log directories (including /var/log/*.log, /var/log/messages*, /var/log/audit/audit.log*, and system journals) to erase traces of intrusion and lateral activity.
It tampers with /etc/hosts to redirect Feiniu’s official update domains, such as apiv2-liveupdate.fnnas.com, to 0.0.0.0, effectively cutting the NAS off from firmware updates and security patches.
It also kills recovery‑related services (like sysrestore_service and backup_service) and deletes update and restore binaries, making in‑place repair or rollback difficult.
For persistence, the malware deploys both systemd services and kernel modules, creating a dual foothold in user and kernel space that survives reboots.
It appends a startup command to system_startup.sh that downloads and runs a second‑stage payload from attacker‑controlled IP space, then sets up copies under paths such as /sbin/gots and /usr/bin/ and registers systemd units to auto‑start.
Later variants add new kernel modules (for example async_memcpys.ko) and services like /etc/systemd/system/dockers.service to refresh persistence and evade cleanup scripts released by Feiniu and users.
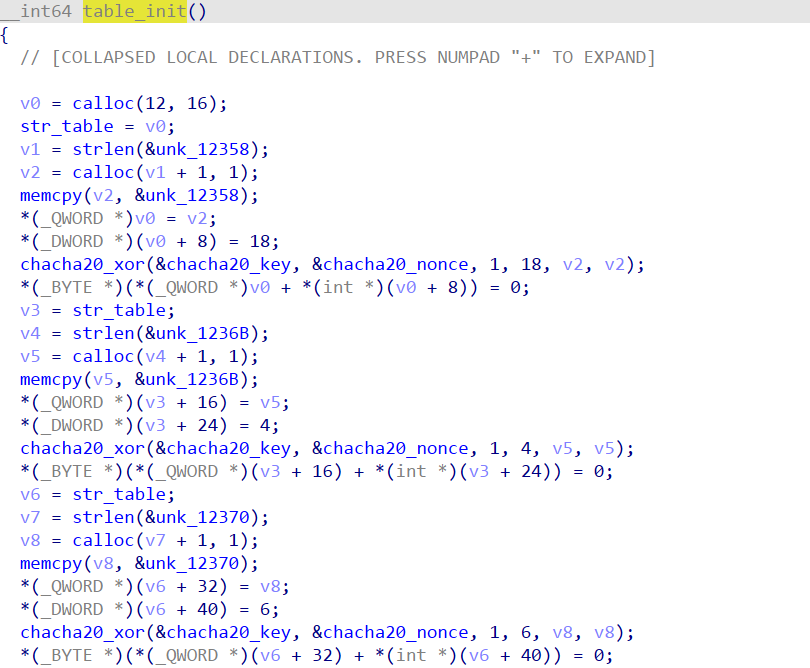
A hard‑coded key and nonce decrypt a string table that includes markers such as PWNED FROM NETDRAG, C2 domains like aura.kabot[.]icu, and system paths it manipulates.
The bot randomly selects C2 endpoints (for example in the 45.95.*.* range or those domains) and one of several ports (3489, 5098, 6608, 7489), then speaks a custom binary message format with typed frames for login, ping/pong, command execution, and DDoS tasks.
Session keys are protected with layered XOR and ChaCha20, using separate nonces for bot‑to‑server and server‑to‑bot traffic, and a handshake step verifies both sides before entering the command loop.
When receiving a DDoS order, the bot also renames /usr/bin/cat and kills monitoring services such as network_service and resmon_service, so admins lose basic tools for observing network and process behavior during an attack.
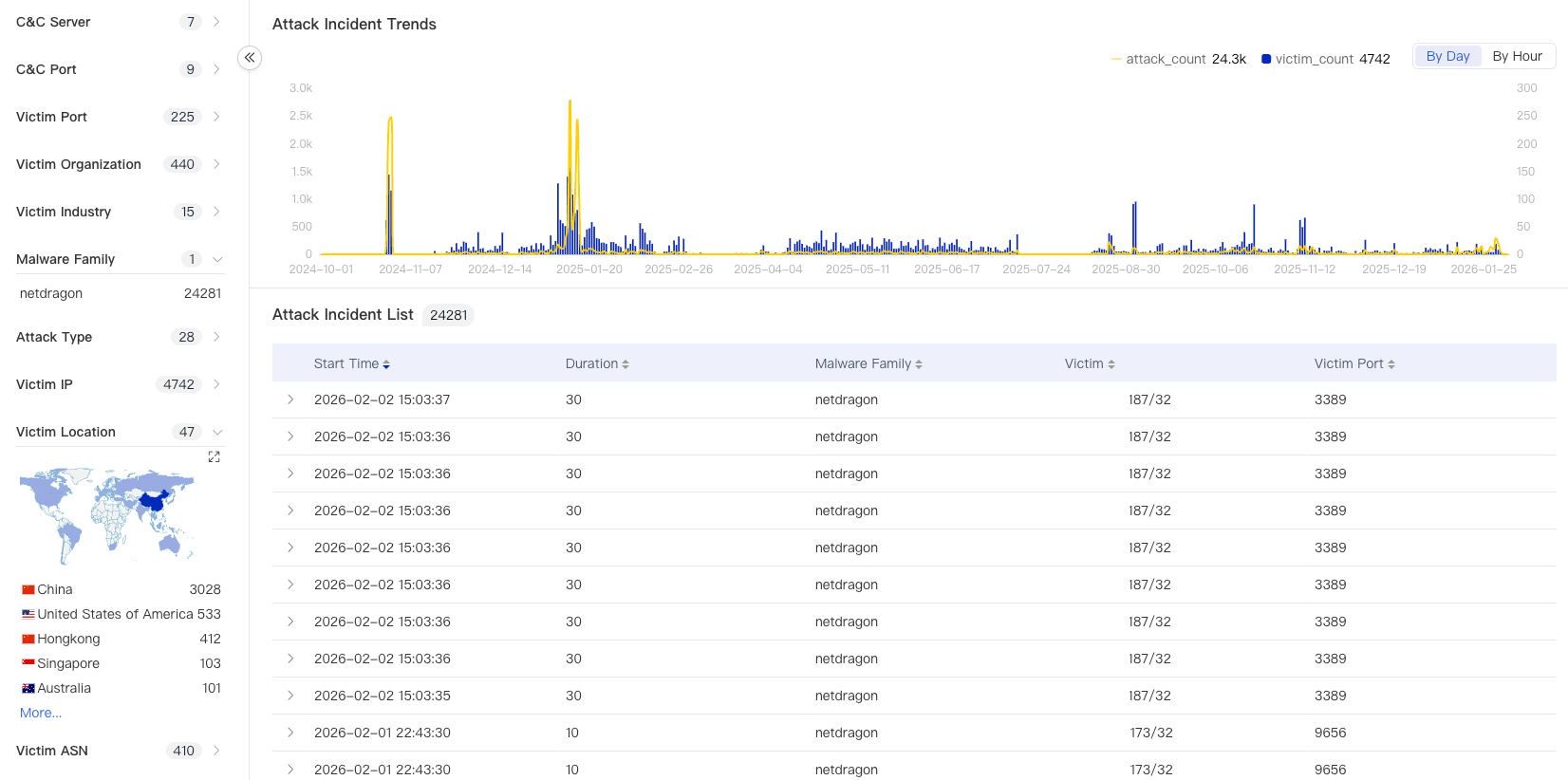
Telemetry shows Netdragon receives attack instructions over channels including Telegram bots and HTTP APIs, then launches broadly targeted DDoS campaigns against organizations in China, the US, Singapore, and Australia across sectors like IT services, manufacturing, and public administration.
Ongoing evolution and impact
As defenders published detection rules and Feiniu shared cleanup scripts, Netdragon operators pushed new builds on January 31 that automatically delete iptables and nftables entries marked with “C2IP”, restoring outbound access to C2 servers.
The DDoS module uses ChaCha20‑encrypted strings and a custom protocol to hide configuration, C2 infrastructure, and attack commands.
The malware also shifted its HTTP backdoor to a new port (57199), refreshed C2 infrastructure, and introduced dynamic 8‑byte key packing to further frustrate static signatures and reverse engineering.
On February 1, operators ordered all bots to delete the rsa_private_key.pem file on Feiniu NAS systems, a destructive step that could break encrypted services or recovery mechanisms and increase the chance of data loss.
Feiniu users have reported that compromised devices sometimes cannot complete firmware upgrades or apply official security tools, leaving them stuck in an infected state and continuously contributing to the botnet.
Until Feiniu and the wider community can close the underlying fnOS vulnerabilities and provide robust offline remediation paths, Netdragon’s evolving toolset will remain a serious threat to both device owners and downstream DDoS victims.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.