Finding security vulnerabilities with GitHub’s new code search

Source link
Related Articles
All Mix →What to do when you feel directionless
What to do when you feel directionless Source link
UL NO. 430: The Courage to be Disliked
Table of Contents TOC NOTES MY WORK SECURITY TECHNOLOGY HUMANS IDEAS & ANALYSIS RECOMMENDATION OF THE WEEK APHORISM OF THE WEEK Continue reading online to…
Create a self-hosted chat service with your own Matrix server
A speed-run introduction to Matrix via Dendrite. Matrix is an open standard for decentralized real-time communication. The specification is production-ready and bridges to tons of…
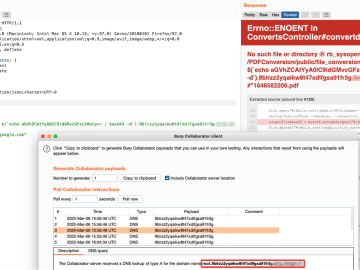
Basic recon to RCE III
For the 3rd and I think last episode of the series, we’re going to continue with the same target as the episode 2, that I…
If You’re Agnostic, You’re Probably an Atheist
Table of Contents Atheism The Difference Between (A)theism and (A)gnosticism Conclusion Notes Related [ 2009-04-12 : I’ve decided to back off this specific argument of…
CORS Misconfigurations: Advanced Exploitation Guide
Table of Contents Same-origin policy (SOP) Cross-origin resource sharing (CORS) Bypassing weak regex pattern validations Null origin Whitelisted third-party origins Accessing internal-only resources with CORS…