An easy phishing attack using a Flipper Zero device can lead to compromising Tesla accounts, unlocking cars, and starting them. The attack works on the latest Tesla app, version 4.30.6, and Tesla software version 11.1 2024.2.7.
Security researchers Talal Haj Bakry and Tommy Mysk reported their finding to Tesla saying that linking a car to a new phone lacks proper authentication security. The car maker determined the report to be out of scope.
Phishing attack
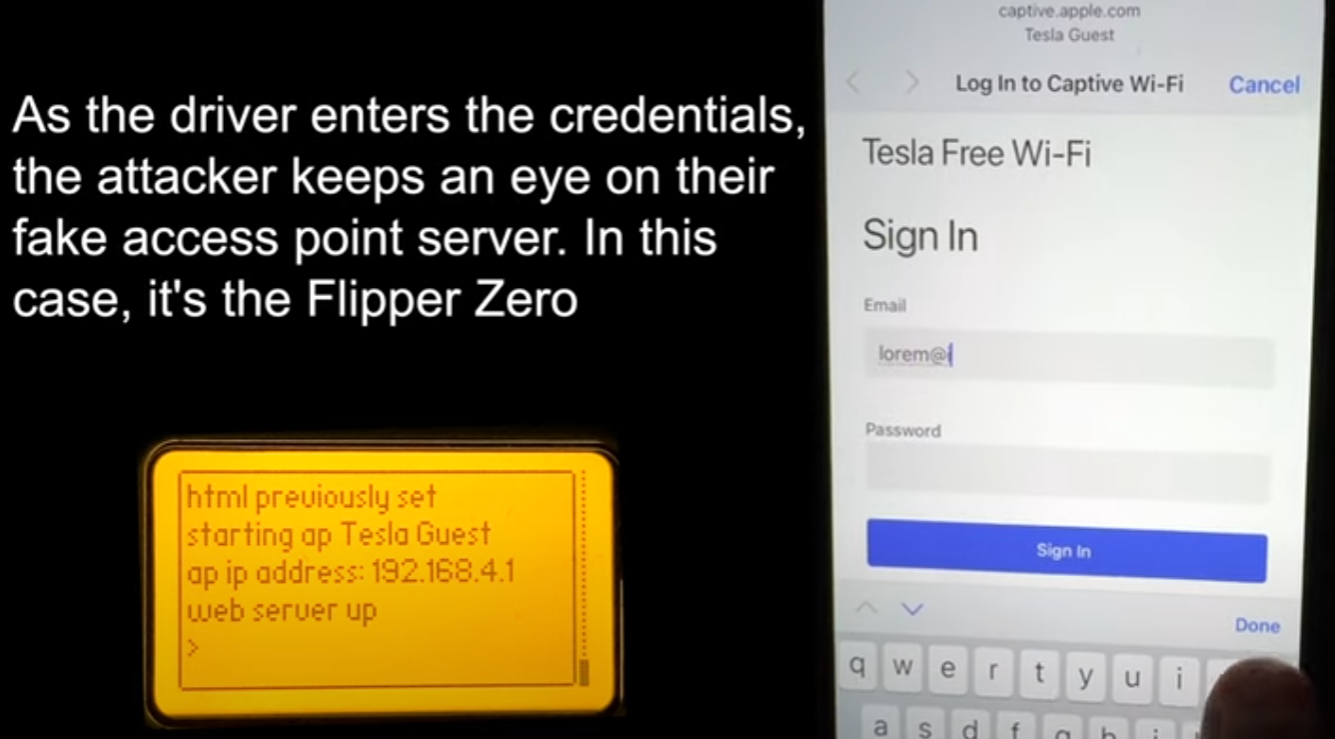
An attacker at a Tesla supercharger station could deploy a WiFi network called”Tesla Guest,” an SSID that is commonly found at Tesla service centers and car owners are familiar with it.
Mysk used a Flipper Zero to broadcast the WiFi network but notes that the same can be accomplished using a Raspberry Pi or other devices that come with WiFi hotspot capabilities.
Once the victim connects to the spoofed network, they are served a fake Tesla login page asking to log in using their Tesla account credentials. Whatever the victim enters on the phishing page, the attacker can see on the Flipper Zero in real time.
After entering the Tesla account credentials, the phishing page requests the one-time password for the account, to help the attacker bypass the two-factor authentication protection.
The attacker has to move before the OTP expires and log into the Tesla app using the stolen credentials. Once in the account, the threat actor can track the vehicle’s location in real time.
Adding a new key
Access to the victim’s Tesla account allows the attacker to add a new ‘Phone Key.’ For this, they must be in close proximity of the car, just a few meters away.
Phone Keys use Tesla’s mobile app in conjunction with the car owner’s smartphone to allow locking and unlocking the vehicle automatically, over a secure Bluetooth connection.
Tesla cars also use Card Keys, which are slim RFID cards that need to be placed on the center console’s RFID reader to start the vehicle. Although more secure, Tesla treats them as a backup option if the Phone Key is unavailable or out of battery.
Mysk says that adding a new Phone Key through the app does not require the car to be unlocked or the smartphone to be inside the vehicle, which makes for significant security gap.
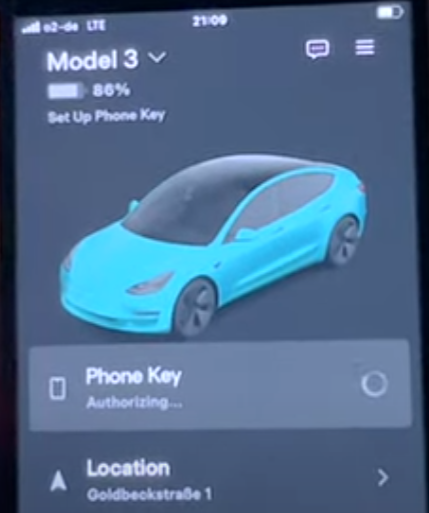
To make matters worse, once a new Phone Key is added, the Tesla owner does not receive a notification about the fact through the app, and no alert is shown on the car’s touchscreen.
With the new Phone Key, the attacker can unlock the car and activate all its systems, allowing them to drive away as if they were the owner.
Mysk notes that the attack is successful on a Tesla Model 3. In the report to the car company, the researcher notes that the hijacked Tesla account must belong to the main driver and that the vehicle must already be linked to a Phone Key.
Additionally, for the attack to work the owner’s mobile phone with the Phone Key must be off or out of the range of the car.
The researchers argue that requiring a physical Tesla Card Key when adding a new Phone Key would improve security by adding an authentication layer for the new phone.
“I was able to add a second phone key on a new iPhone without the Tesla app prompting me to use a key card to authenticate the session on the new iPhone. I only signed in on the new iPhone with my username and password, and as soon as I granted the app access to the location services, it activated the phone key,” Tommy Mysk and Talal Haj Bakry wrote in the report to Tesla.
The company replied by saying that its investigation determined that it was the intended behavior and that the Tesla Model 3 owner’s manual does not state that a key card is needed to add a phone key.
BleepingComputer has contacted Tesla with questions on the above and whether they plan to issue an OTA update that introduces security measures to prevent these attacks, but we have not heard back yet.






