The Russian APT28 hacking group (aka ‘Strontium’ or ‘Fancy Bear’) has been targeting government entities, businesses, universities, research institutes, and think tanks in France since the second half of 2021.
The threat group, which is considered part of Russia’s military intelligence service GRU, was recently linked to the exploitation of CVE-2023-38831, a remote code execution vulnerability in WinRAR, and CVE-2023-23397, a zero-day privilege elevation flaw in Microsoft Outlook.
The Russian hackers have been compromising peripheral devices on critical networks of French organizations and moving away from utilizing backdoors to evade detection.
This is according to a newly published report from ANSSI (Agence Nationale de la sécurité des systèmes d’information), the French National Agency for the Security of Information Systems, that conducted investigations on the activities of the cyber-espionage group.
Network reconnaissance and initial access
ANSSI has mapped the TTPs (techniques, tactics, and procedures) of APT28, reporting that the threat group uses brute-forcing and leaked databases containing credentials to breach accounts and Ubiquiti routers on targeted networks.
In one case from April 2023, the attackers ran a phishing campaign that tricked the recipients into running PowerShell that exposed their system configuration, running processes, and other OS details.
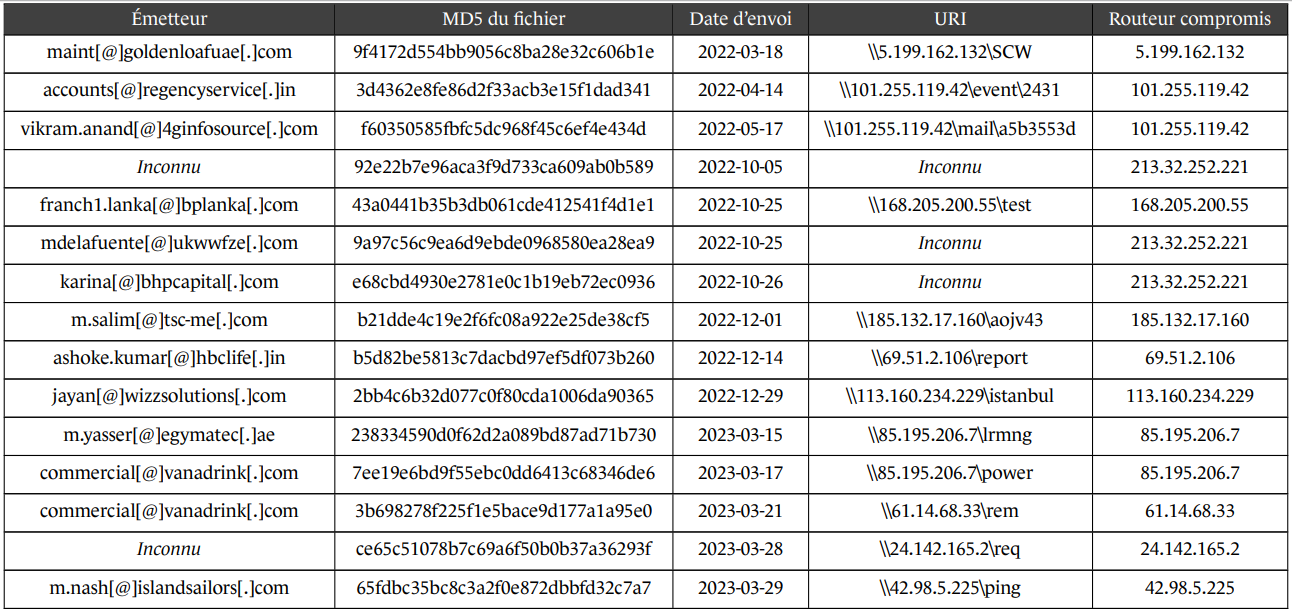
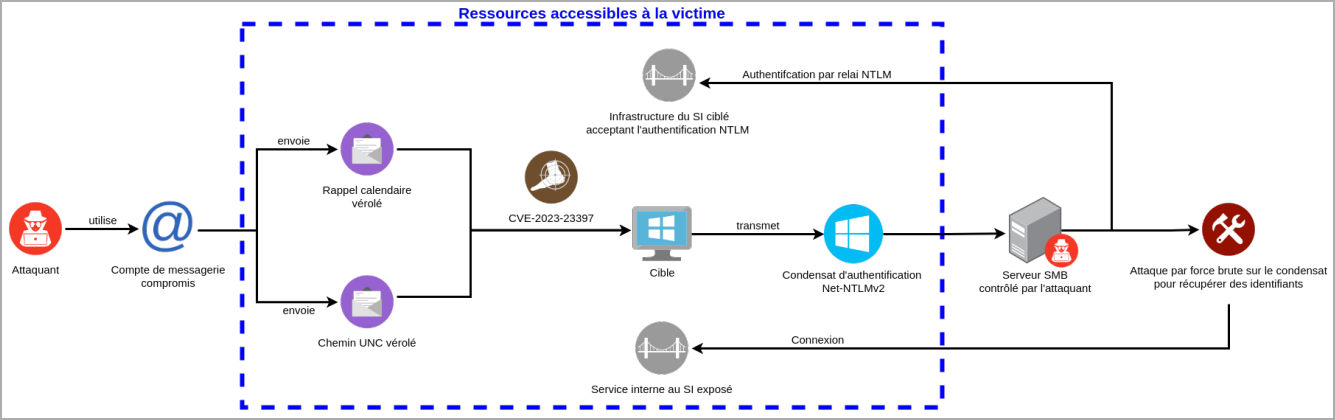
Between March 2022 and June 2023, APT28 sent emails to Outlook users that exploited the then zero-day vulnerability now tracked as CVE-2023-23397, placing the initial exploitation a month earlier than what was recently reported.
During this period, the attackers also exploited CVE-2022-30190 (aka “Follina”) in the Microsoft Windows Support Diagnostic Tool and CVE-2020-12641, CVE-2020-35730, CVE-2021-44026 in the Roundcube application.
The tools used in the first stages of the attacks include the Mimikatz password extractor and the reGeorg traffic relaying tool, as well as the Mockbin and Mocky open-source services.
ANSSI also reports that APT28 uses a range of VPN clients, including SurfShark, ExpressVPN, ProtonVPN, PureVPN, NordVPN, CactusVPN, WorldVPN, and VPNSecure.
Data access and exfiltration
As a cyber-espionage group, data access and exfiltration are at the core of Strontium’s operational goals.
ANSSI has observed the threat actors retrieving authentication information using native utilities and stealing emails containing sensitive information and correspondence.
Specifically, the attackers exploit CVE-2023-23397 to trigger an SMB connection from the targeted accounts to a service under their control, allowing the retrieval of the NetNTLMv2 authentication hash, which can be used on other services, too.
APT28’s command and control server (C2) infrastructure relies on legitimate cloud services, such as Microsoft OneDrive and Google Drive, to make the exchange less likely to raise any alarms by traffic monitoring tools.
Finally, ANSSI has seen evidence that the attackers collect data using the CredoMap implant, which targets information stored in the victim’s web browser, such as authentication cookies.
Mockbin and the Pipedream service are also involved in the data exfiltration process.
Defense recommendations
ANSSI emphasizes a comprehensive approach to security, which entails assessing risks. In the case of the APT28 threat, focusing on email security is crucial.
The agency’s key recommendations around email security include:
- Ensure the security and confidentiality of email exchanges.
- Use secure exchange platforms to prevent email diversions or hijacks.
- Minimize the attack surface of webmail interfaces and reduce risks from servers like Microsoft Exchange.
- Implement capabilities to detect malicious emails.
For more details on ANSSI’s findings and defense tips, check out the full report here.







