FROM 0 to $$$$ – MY BIGGEST BUG BOUNTY LEARNINGS!

Source link
Related Articles
All Mix →Fundamentals of GraphQL-specific attacks – API Security
Table of Contents GraphQL vs REST APIs Excessive Value Length Query depth Batching attacks Maximum aliases Schema introspection Debug Mode GraphiQL How to protect your…
Improve DevOps Security With Code Security Audit
Table of Contents Use Code Security Audit for DevOps Identify Risks in Code with Expert Reviewers Secure Integrations and Controls A Key Addition to the…
[Integration] Integrate Detectify with Jira, Github, Instagram and much more using Zapier
Automation should be for everyone, which is why we at Detectify love Zapier. We wanted to make it possible for our customers to use Detectify…
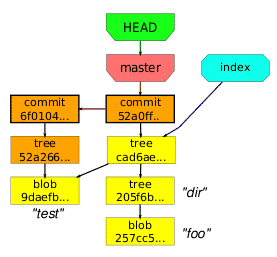
Git: Ignore WordPress Cache Files using .gitignore
I’ve had a nagging problem for some time where I couldn’t figure out quite how to ignore my wp-content/cache directory when doing syncs with git.…
Nahamsec interviews Rhok
Table of Contents Profile 🐝 Timeline 🐝 Live hacking events 🐝 Collaboration 🐝 Learning 🐝 Programming 🐝 Advice 🐝 Methodology 🐝 Links 🐝 Note that…
Secrets of Google’s Information Security Team
Table of Contents Everyone on the Security Team is a Programmer Google’s Security Team Writes All of Their Security Libraries All Code is Reviewed by…