A dispute over maintainer access in the widely used Go library fsnotify has triggered temporary supply chain concerns after contributors were removed from the project’s GitHub organization and recent releases came under scrutiny.
While no evidence suggests that any version of fsnotify has been compromised, the incident highlights how governance ambiguity in critical open source projects can quickly raise red flags across the software ecosystem.
fsnotify is a cross-platform filesystem notification library supporting Windows, Linux, macOS, BSD, and illumos.
With more than 10,000 GitHub stars and over 300,000 dependent projects, it sits deep in the development stack, powering developer tools, CLI utilities, and infrastructure workflows.
Because of this widespread adoption, even minor uncertainty around maintainer control or release authority can ripple downstream rapidly.
The issue began when Go developer Yasuhiro Matsumoto (known as mattn) claimed he had been removed from the fsnotify GitHub organization.
In a now-deleted social media post, he suggested that internal conflicts led to contributors losing access, raising fears of a potential project takeover.
The claims quickly fueled discussion in a GitHub issue, where users sought clarification on who currently controls the repository.
Security concerns were amplified by a combination of signals: recent releases after a long quiet period, revoked maintainer access, and unclear review processes.
For many observers, these indicators resembled early warning signs seen in past supply chain attacks, even though no malicious activity was confirmed.
Earlier in April 2026 research by Socket, automated security tools had already flagged fsnotify as “unmaintained” after more than a year without a release.
Shortly after, Matsumoto published versions 1.10.0 and 1.10.1, addressing bugs in filesystem event handling, particularly issues affecting Linux inotify behavior. While the updates resolved legitimate problems, their timing added to the uncertainty.
fsnotify Maintainer Access
Project maintainer Martin Tournoij (@arp242) denied any takeover scenario, stating that removed contributors had legacy commit access but were not actively maintaining the project.
Grafana Staff Developer Advocate Oshi Yamaguchi, who started the thread, noted that fsnotify is widely used by major open source projects and that downstream users needed more context to evaluate the change.
He argued that recent contributions were merged too quickly without sufficient cross-platform review and introduced quality concerns.
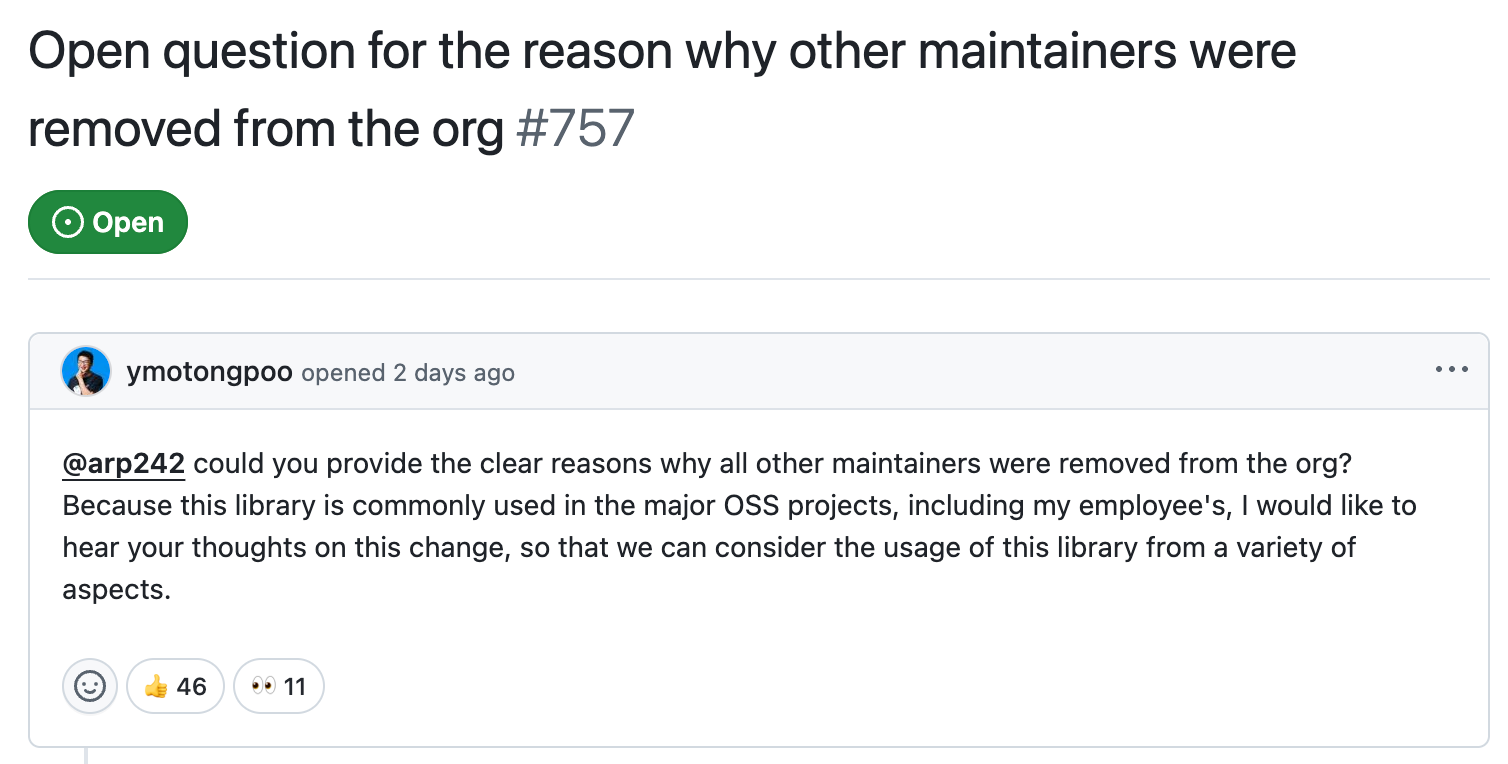
Tournoij emphasized that access removal was a governance and code quality decision, not a hostile action. He also pointed to disagreements over a funding configuration update, which he said was committed directly to the main branch without discussion.
Matsumoto later acknowledged inaccuracies in his earlier statements and apologized, clarifying that his intent was to help revive a project that had not seen a release in over a year.
He cited multiple bug fixes and stabilization efforts as evidence of legitimate maintenance work but expressed concern about the lack of multiple active maintainers for peer review.
The situation quickly reached downstream projects. Kubernetes contributors opened discussions questioning the health of fsnotify and whether alternatives or forks should be considered. One such fork, gofsnotify/fsnotify, emerged as a potential fallback and is now being monitored.
Security experts note that incidents like this mirror early stages of real supply chain compromises, where unusual maintainer behavior, sudden releases, and unclear authority create uncertainty.
A comparable example is the xz-utils backdoor incident, where trust in maintainers was exploited over time.
As Docker and container ecosystem maintainers pointed out, dependencies like fsnotify often operate quietly in the background, making them easy to overlook until something changes.
Automated tools such as Dependabot can further amplify risk by encouraging quick updates without deeper verification.
The fsnotify incident ultimately underscores a broader issue: lack of transparency in open source governance. When users cannot clearly identify who controls a project’s release pipeline, even routine internal disputes can trigger widespread security concerns.
Although no compromise has been detected, the episode demonstrates how quickly trust can erode when maintainer roles, access controls, and review processes are not clearly defined.
For widely adopted libraries, establishing transparent governance and release practices is increasingly critical to maintaining supply chain confidence.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.