Fundamentals of Bug Bounty Recon

Source link
Related Articles
All Mix →Create a self-hosted chat service with your own Matrix server
A speed-run introduction to Matrix via Dendrite. Matrix is an open standard for decentralized real-time communication. The specification is production-ready and bridges to tons of…
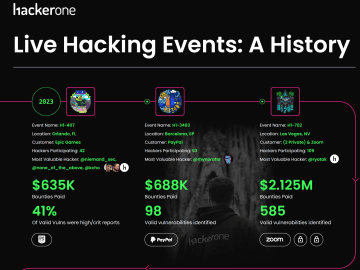
The Evolution of HackerOne’s Live Hacking Events
If you’ve heard of HackerOne, then you’ve heard about our Live Hacking Events. For years, we’ve been bringing together the brightest minds in security to…
Nine Months into the DIB-VDP Pilot, Nearly 1,000 Valid Vulnerabilities Have Been Identified
Maintaining the security of the digital assets within the Defense Industrial Base (DIB) contractor networks helps defend the United States of America. For the last…
How to Build a Strong Argument
Table of Contents Basic Structure Title Introduction Your Thesis Supporting Paragraphs Addressing the Counterarugument Conclusion References In the spirit of improving my debating skills (both…
You Can BUY This Hacked YouTube Channel
You Can BUY This Hacked YouTube Channel Source link
Better Quicksearches with QuickSilver | Daniel Miessler
Like many out there I’m rather obsessed with doing things the best way possible. Up until yesterday I was using browser-based quick searches to perform…