Hackers are abusing GitHub and Jira’s built‑in notification systems to send phishing emails that appear completely legitimate.
Because these emails are sent from the platforms’ own mail servers, they pass standard checks like SPF, DKIM, and DMARC, making them very hard for traditional email gateways to block.
The messages are routed via the official mail infrastructure of these services, so security products see them as trusted traffic from known-good domains.
Most campaigns focus on phishing and credential harvesting, often used as a first step before further attacks once accounts are compromised.
During one campaign on 17 February 2026, around 2.89% of all emails observed coming from GitHub were likely tied to this abuse, highlighting the scale of the problem.
Cisco Talos has observed a recent spike in spam and phishing activity delivered through notification pipelines in popular SaaS collaboration tools, especially GitHub and Atlassian Jira.
Over a five‑day window, about 1.20% of messages from “[email protected]” carried an “invoice” lure in the subject line, signaling a focused billing‑themed phishing run.
Platform‑as‑a‑Proxy (PaaP) technique
This emerging “Platform‑as‑a‑Proxy” model uses legitimate SaaS platforms as delivery proxies for malicious content.
Because the emails are generated and signed by GitHub or Jira, they meet all authentication requirements and inherit the reputation of the provider.
This effectively separates the attacker’s intent from the underlying infrastructure and gives the phishing mail a built‑in “seal of approval” many gateways do not challenge.
Attackers embed their social‑engineering lures inside normal workflow notifications, such as commit alerts or service desk invitations.
Users see notifications they are used to receiving and are more likely to click, especially when the content mentions invoices, support issues, or urgent account problems.
On GitHub, threat actors exploit the automated commit notification system. They create repositories and push commits that contain malicious text in the two standard commit fields: a short summary and a longer description.
The summary line, which appears first and most prominently in email alerts, is crafted as the initial hook, often referencing billing or account issues.
The extended description field is then used to host the main scam content, such as fake billing statements, fraudulent support numbers, or phishing links.
When the commit is pushed, GitHub infrastructure sends an automatic email to collaborators from a legitimate SMTP host like “out‑28.smtp.github.com”, signed with a valid “d=github.com” DKIM signature.
Because the message structure and headers are genuine, it easily slips past security filters and lands directly in users’ inboxes.
Jira invitation hijacking
In Jira, attackers focus on invitation and service desk workflows rather than raw notification pipelines.
They set up Jira Service Management projects and abuse configurable fields such as “Project Name”, “Welcome Message”, or “Project Description” to insert their lures.
When Jira sends automated “Customer Invite” or “Service Desk” emails, Atlassian’s backend injects this content into its own trusted, cryptographically signed templates.
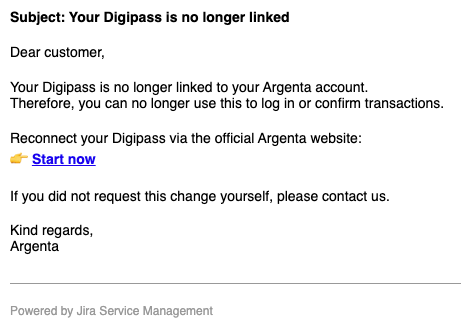
Victims then receive professional‑looking messages that appear to come from a legitimate Jira project, complete with Atlassian branding in the footer.
Because Jira notifications are common in corporate environments and often critical for IT workflows, these emails are rarely blocked, allowing phishing content to masquerade as internal helpdesk or project alerts.
This activity exposes a growing “trust paradox,” where organizations treat emails from major SaaS platforms as inherently safe.
Defenders should: identity‑check which specific SaaS instances and sender identities are allowed, ingest GitHub and Atlassian API logs into SIEM/SOAR to detect suspicious repository or project activity, and profile “normal” business usage so that urgent billing or financial lures from code or ticketing tools are flagged as semantically abnormal.
GitHub is abused for its strong developer reputation, while Jira is leveraged for its role in business‑critical processes, letting attackers launder malicious content through trusted brands.
Cisco Talos recommends moving away from binary domain‑level trust towards a Zero‑Trust mindset for SaaS notifications.
Adding friction for high‑risk notifications and automating takedowns of malicious repositories or Jira projects can further raise attacker costs and reduce the effectiveness of this PaaP model.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.