Google has overhauled its Vulnerability Reward Programs (VRP) for Chrome and Android in response to a surge in the use of AI tools for vulnerability discovery.
In the case of the Android and Google Devices VRP, Google is now focusing on vulnerabilities with the highest user impact, and is prioritizing flaw categories that are more difficult for AI tools to find.
The tech giant also announced incentivizing actionable reports, explaining, “We are shifting our program focus on Linux kernel vulnerabilities to Google-maintained components unless there is concrete proof of exploitability on Android or our devices. For most vulnerabilities we will also be strongly incentivizing reports to contain proposed patches for addressing the underlying issue.”
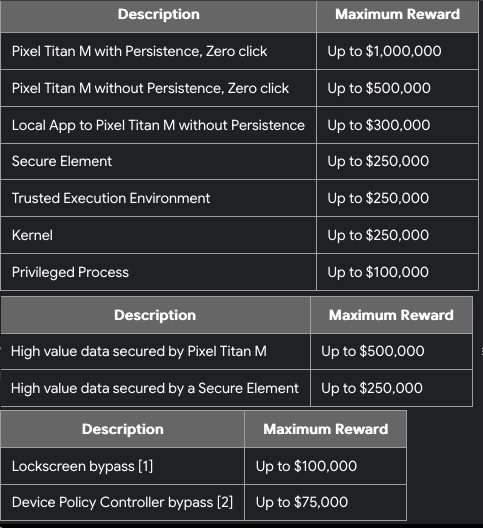
In terms of the reward amounts, the maximum payouts have increased considerably, from $1 million to $1.5 million for zero-click Pixel Titan M exploits with persistence, and from $500,000 to $750,000 for exploits without persistence. Secure element data exfiltration is now worth up to $375,000, from $250,000.
For Chrome vulnerabilities, on the other hand, standard payout amounts have dropped significantly as the company is shifting focus to actionable reports.
“While AI has made it effortless to produce lengthy, detailed write-ups, our internal tooling has also evolved to help us automatically explain and suggest fixes for bugs,” Google explained. “Moving forward, we are shifting our program’s focus to prioritize concrete proof that a bug exists. We now consider the most effective reports to be concise, containing only a reproducer and the necessary artifacts to help us validate and route the issue.”
Specifically, the base reward for memory safety issues is now $500, with multipliers for factors such as reachability and the level of exploitability. Security researchers pointed out that some Chrome bug rewards are now 10 times smaller than before.
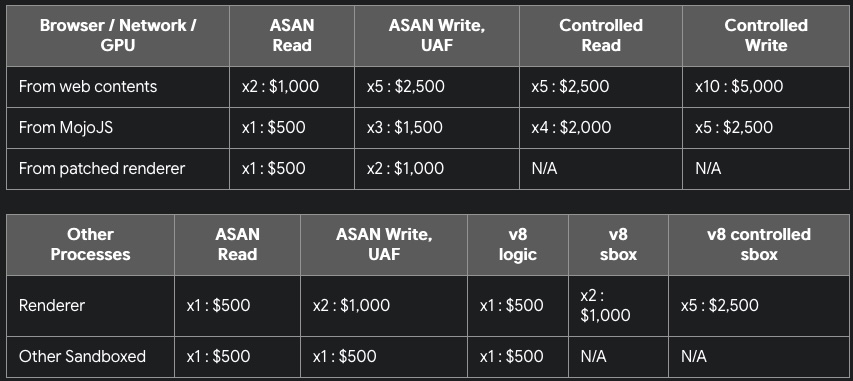
The company also announced phasing out bonuses introduced last year for arbitrary read/write and remote code execution vulnerabilities following a surge in AI-driven submissions.
Google also plans to release special Chrome configurations designed for security researchers to demonstrate arbitrary read/write and memory-leak issues.
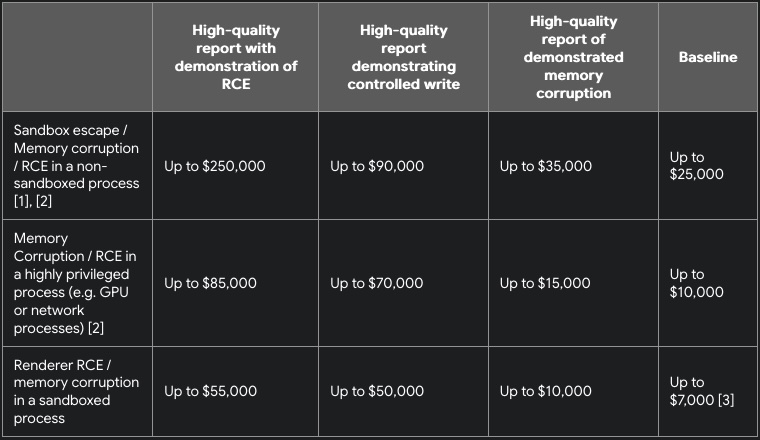
It’s worth noting that a full-chain Chrome exploit is still worth up to $250,000, with the same amount offered as a bonus for a MiraclePtr bypass.
While individual bug payouts may drop, Google expects to increase its total aggregate rewards for 2026 after paying a record-high $17.1 million in 2025.
The changes announced by Google are not surprising. Advanced AI tools such as Anthropic’s Claude Mythos and OpenAI’s GPT‑5.4‑Cyber are bringing significant changes to the vulnerability discovery landscape.
While Mythos and GPT‑5.4‑Cyber currently have limited availability to prevent abuse, even widely available tools have led to a surge in AI-based vulnerability reports, leaving some organizations overwhelmed by these submissions.
The Internet Bug Bounty (IBB) program recently paused accepting new vulnerability reports due to an influx of AI-assisted security research, and many other organizations have complained about the impact of AI tools, which create a significant imbalance between the volume of submissions and the ability to address vulnerabilities.
Related: OpenAI Launches Bug Bounty Program for Abuse and Safety Risks
Related: Google Offers Up to $20,000 in New AI Bug Bounty Program






