Google Dorks and DoD

Source link
Related Articles
All Mix →Facism: “I Don’t Think That Word Means What You Think It Means.”
Many, especially in the blogsphere, are fond of saying, “This country is becoming fascist.” Or, “We’re on a path to fascism.” That sounds cool, and…
Getting Worried About Linux | Daniel Miessler
So I’m getting a little freaked out lately. I keep hearing that both the Gentoo and Debian projects are in trouble. I haven’t researched how…
The Republican Agenda is Bad for America
Table of Contents 1. First Principles 2. Applicaiton of First Principles 3. Mapping the Needs of the Middle Class 4. Obstacles to the American Middle…
Introducing the Wallarm Q1 2024 API ThreatStats™ Report –
As we have in previous editions of the ThreatStats report, we highlight the industry’s top API-related attacks and trends. New to this version, however, is…
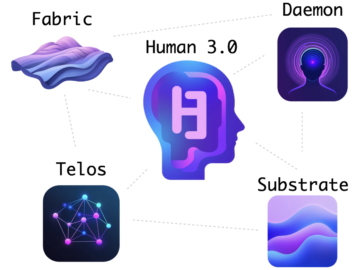
How My Projects Fit Together
Table of Contents Table of Contents The Problem(s) Security forever The Major Projects Substrate Fabric Telos Daemon Human 3.0 Component Summary Summary When people look…
Introducing the Hacker101 CTF | HackerOne
Hacker101 is getting something brand new: our own Capture The Flag! For those who are unfamiliar, Capture The Flags (better known as CTFs) are games…