Google has released security updates to fix the first Chrome zero-day vulnerability exploited in the wild since the start of the year.
“Google is aware of reports that an exploit for CVE-2024-0519 exists in the wild,” the company said in a security advisory published Tuesday.
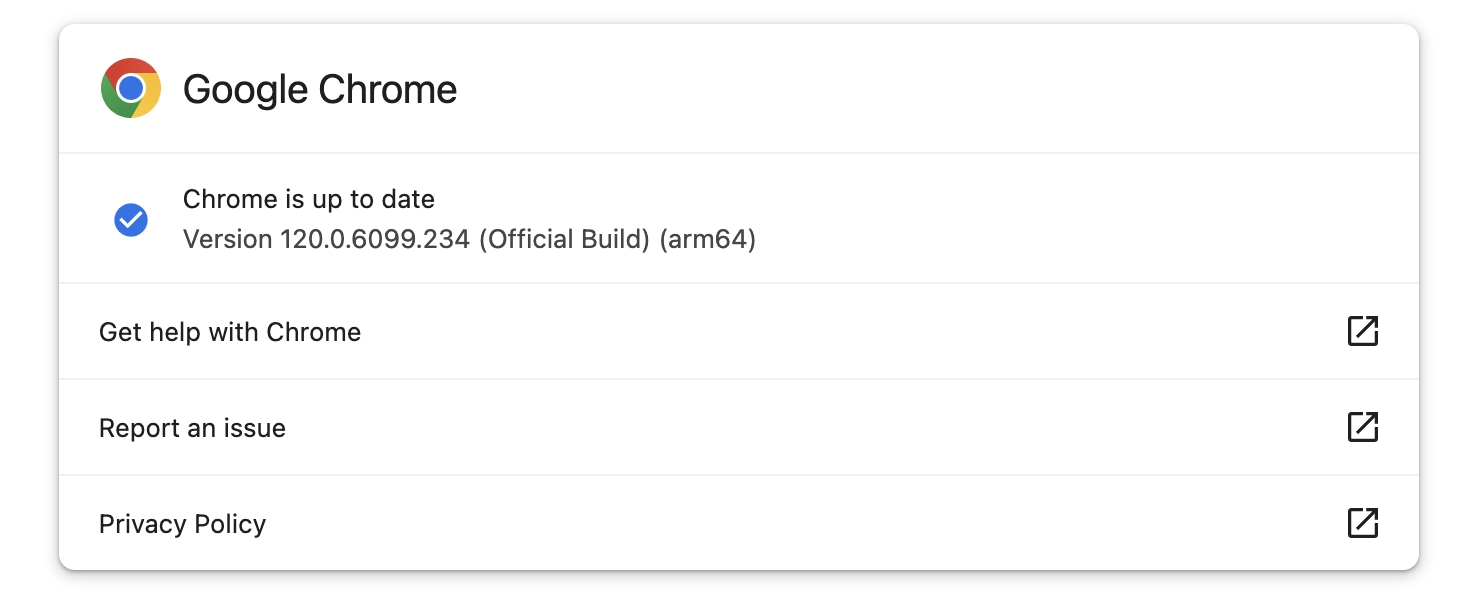
The company fixed the zero-day for users in the Stable Desktop channel, with patched versions rolling out worldwide to Windows (120.0.6099.224/225), Mac (120.0.6099.234), and Linux (120.0.6099.224) users less than a week after being reported to Google.
Although Google says the security update could take days or weeks to reach all impacted users, it was available immediately when BleepingComputer checked for updates today.
Those who prefer not to update their web browser manually can rely on Chrome to automatically check for new updates and install them after the next launch.
The high-severity zero-day vulnerability (CVE-2024-0519) is due to a high-severity out-of-bounds memory access weakness in the Chrome V8 JavaScript engine, which attackers can exploit to gain access to data beyond the memory buffer, providing them access to sensitive information or triggering a crash.
“The expected sentinel might not be located in the out-of-bounds memory, causing excessive data to be read, leading to a segmentation fault or a buffer overflow,” MITRE explains. “The product may modify an index or perform pointer arithmetic that references a memory location that is outside of the boundaries of the buffer. A subsequent read operation then produces undefined or unexpected results.”
Besides unauthorized access to out-of-bounds memory, CVE-2024-0519 could also be exploited to bypass protection mechanisms such as ASLR to make it easier to achieve code execution via another weakness.
While Google knows of CVE-2024-0519 zero-day exploits used in attacks, the company has yet to share further details regarding these incidents.
“Access to bug details and links may be kept restricted until a majority of users are updated with a fix,” Google said. “We will also retain restrictions if the bug exists in a third party library that other projects similarly depend on, but haven’t yet fixed.”
Today, Google also patched V8 out-of-bounds write (CVE-2024-0517) and type confusion (CVE-2024-0518) flaws, allowing for arbitrary code execution on compromised devices.
Last year, Google fixed eight Chrome zero-day bugs exploited in attacks tracked as CVE-2023-7024, CVE-2023-6345, CVE-2023-5217, CVE-2023-4863, CVE-2023-3079, CVE-2023-4762, CVE-2023-2136, and CVE-2023-2033.
Some of them, like CVE-2023-4762, were tagged as zero-days used to deploy spyware on vulnerable devices belonging to high-risk users, including journalists, opposition politicians, and dissidents, several weeks after the company released patches.