Google released emergency updates to fix another Chrome zero-day vulnerability exploited in attacks, marking the fourth such security flaw patched since the start of the year.
“Google is aware that an exploit for CVE-2026-5281 exists in the wild,” Google said in a security advisory issued on Tuesday.
As detailed in the Chromium commit history, this vulnerability stems from a use-after-free weakness in Dawn, the underlying cross-platform implementation of the WebGPU standard used by the Chromium project.
Attackers can exploit this Dawn security flaw to trigger web browser crashes, data corruption, rendering issues, or other abnormal behavior.
While Google has found evidence that threat actors were exploiting this zero-day flaw in the wild, it did not share details about these incidents.
“Access to bug details and links may be kept restricted until a majority of users are updated with a fix. We will also retain restrictions if the bug exists in a third party library that other projects similarly depend on, but haven’t yet fixed,” the company noted.
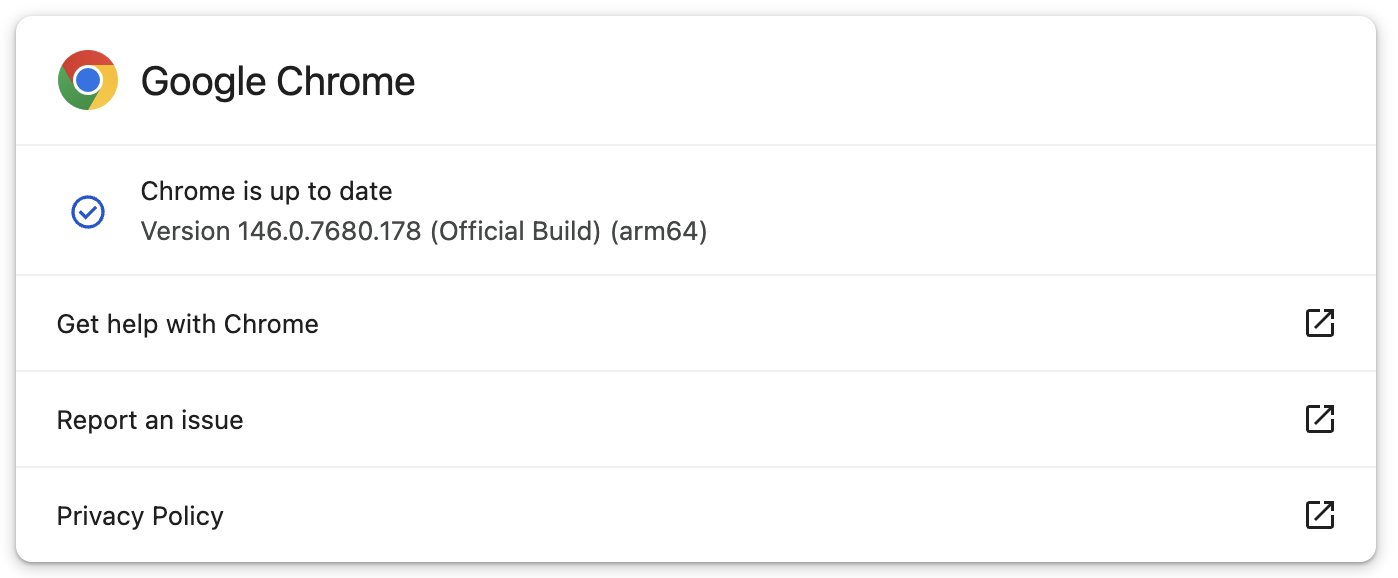
Google has now fixed the zero-day for users in the Stable Desktop channel, with new versions rolling out to Windows, macOS (146.0.7680.177/178), and Linux users (146.0.7680.177). While Google says that this out-of-band update could take days or weeks to reach all users, it was immediately available when BleepingComputer checked for updates today.
If you don’t want to update the browser manually, you can also have it check for updates at the next launch and install them automatically.
This is the fourth actively exploited Chrome zero-day patched since the start of the year. The first (CVE-2026-2441) was an iterator invalidation bug in CSSFontFeatureValuesMap (Chrome’s implementation of CSS font feature values), which Google addressed in mid-February.
Google patched two other Chrome zero-day bugs exploited in attacks earlier this month: the first is an out-of-bounds write weakness in the Skia 2D graphics library (CVE-2026-3909), and the second is an inappropriate implementation vulnerability in the V8 JavaScript and WebAssembly engine (CVE-2026-3910).
In 2025, Google fixed a total of eight zero-days exploited in the wild, many of which were discovered and reported by Google’s Threat Analysis Group (TAG), which is known for tracking and identifying zero-day exploits used in spyware attacks.

Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.







