The Gootloader malware family employs sophisticated social engineering tactics to infiltrate computers.
By leveraging compromised legitimate WordPress websites, Gootloader’s operators manipulate Google search results to redirect users to a deceptive online message board.
They link the malware to a simulated conversation featuring fictitious users, effectively answering the exact queries victims input into search engines.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try for Free
Infection Mechanism and Server Orchestration
The infection process hinges on the interplay between compromised WordPress servers and a central server (referred to as the “mothership”).
This complex architecture dynamically generates pages that appear to provide valid responses to user queries.
Operators modify the site behind the scenes, embedding code that loads content from the mothership.
Security researchers have found that the obfuscation techniques used are so extensive that even site owners may struggle to detect alterations or trigger the Gootloader scripts themselves.
Sophos X-Ops has recently reconstructed Gootloader’s server-side operations using insights gathered from various threat analysts and open-source intelligence.
The analysis reveals how Gootloader’s malicious search engine optimization (SEO) strategies operate.


Each malicious JScript file corresponds directly to the search terms that lead victims to the compromised sites, showcasing the operators’ ability to carefully tailor their tactics.
Technical Analysis of Malicious Code
The Gootloader malware employs intricately obfuscated code to evade detection, utilizing randomized variable names and segmented functions.
This coding strategy complicates dynamic analysis, prolonging the time required for security experts to understand the underlying operations.
Researchers successfully identified specific functions within Gootloader’s code that handle tasks such as string manipulation and the execution of base64-encoded payloads.
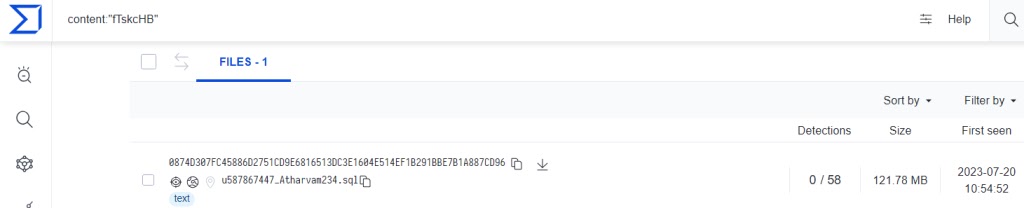
The malware uses a unique identifier embedded in script tags, allowing it to interact with the mothership to fetch the first-stage JScript downloader.
This downloader is then seamlessly integrated into the compromised websites through fake forum pages, which mislead victims into downloading malicious files under the guise of helpful content.
The insights gained from this examination not only elucidate the infection process but also provide actionable intelligence for developing detection and prevention measures against Gootloader’s ongoing threats.
As the malware continues to evolve, so too must the strategies employed by cybersecurity professionals to combat it effectively.
For the Indicators of compromise, you can refer here.
Integrating Application Security into Your CI/CD Workflows Using Jenkins & Jira -> Free Webinar







