GrayCharlie is abusing compromised WordPress sites to silently load malicious JavaScript that pushes NetSupport RAT, often followed by Stealc and SectopRAT, via fake browser updates and ClickFix lures.
Insikt Group tracks GrayCharlie as a financially motivated threat actor overlapping with SmartApeSG, active since mid‑2023, and specializing in turning legitimate WordPress sites into malware-delivery points.
The actor injects links to externally hosted JavaScript into compromised pages, which then redirect visitors to fake browser-update pages or ClickFix-style social engineering flows that ultimately deliver the NetSupport RAT.
Once NetSupport is installed and connected to attacker‑controlled C2 servers, GrayCharlie operators gain remote access for surveillance, file operations, and follow‑on payload delivery, including infostealer Stealc and remote access malware SectopRAT.
Insikt Group reports that GrayCharlie operates a sizable, layered infrastructure footprint, heavily concentrated on providers MivoCloud and HZ Hosting Ltd.
This includes dedicated NetSupport RAT C2 servers, staging servers hosting the malicious JavaScript templates, and higher‑tier systems used to administer campaigns, often accessed through proxy services.
The group’s activity remains consistent across campaigns, with recurring use of the same infection chains, license keys, and TLS certificate patterns on its C2 infrastructure.
Fake Updates, ClickFix, and Law Firm
Initially, GrayCharlie relied primarily on fake browser update overlays, which appear tailored to Chrome, Edge, or Firefox and prompt users to download a supposed update package that is actually a JavaScript driven NetSupport installer.
The IP addresses associated with the staging infrastructure are linked to websites impersonating “Wiser University” a fictional entity used to demonstrate Wiser, a free Bootstrap HTML5 education.
The loader script launches via WScript, stages PowerShell, downloads and extracts the NetSupport client into locations such as %AppData%, adds Registry Run keys for persistence, and then beaconing to GrayCharlie‑controlled C2 servers.
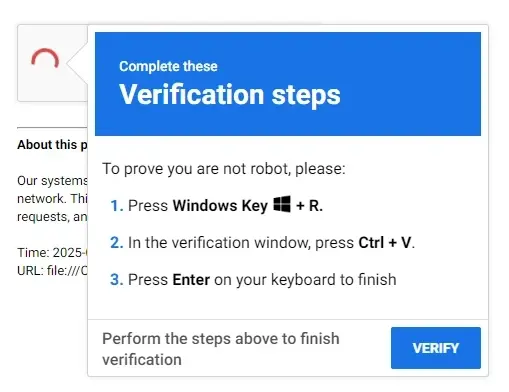
In 2025, the actor expanded to a ClickFix flow, where compromised WordPress pages display a fake CAPTCHA that copies a PowerShell‑based command to the clipboard and instructs users to execute it using the Windows Run dialog, again resulting in NetSupport RAT installation and persistence.
Most victim sites appear opportunistically compromised across many sectors, but Insikt Group also highlights a notable cluster of US law firm WordPress sites that began loading malicious JavaScript from GrayCharlie‑controlled infrastructure around November 2025.
Evidence suggests these law firm sites may have been compromised via a supply‑chain vector involving a shared IT or marketing provider, with SMB Team cited as a likely avenue due to its branding and shared credentials surfacing around the time the malicious infrastructure became active.

While GrayCharlie’s ultimate objectives remain unclear, current telemetry points to data theft, financial gain, and potentially selling or sharing access with other threat actors, underlining the risk to legal and other high‑value targets.
Mitigations
Insikt Group advises defenders to aggressively block IP addresses and domains tied to NetSupport RAT, Stealc, SectopRAT, and other tools used in GrayCharlie operations, and to treat traffic to known‑compromised WordPress sites as high‑risk until remediated.
The page presents a fake CAPTCHA that quietly copies a malicious command to the user’s clipboard and instructs them to paste it into the Windows Run dialog (Win+R).
Security teams should deploy updated YARA, Snort, and Sigma rules to detect NetSupport components, ClickFix‑style commands, and GrayCharlie’s JavaScript and PowerShell loader patterns, including in historical logs.
Additional recommended controls include tightening email and web filtering, monitoring for suspicious data exfiltration to known malicious infrastructure, and continuously ingesting new GrayCharlie threat intelligence sources to keep detection and blocking policies current.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.