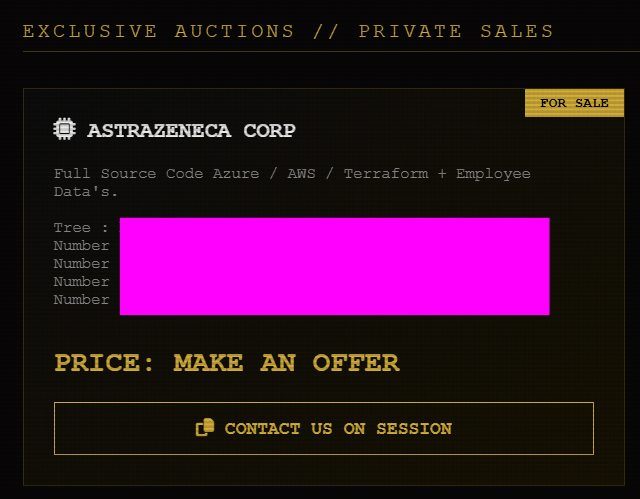
A threat actor group identifying itself as “LAPSUS$” is claiming responsibility for an alleged data breach involving AstraZeneca, one of the world’s largest multinational pharmaceutical and biotechnology company. The group claims to have obtained approximately 3GB of internal data, including source code, cloud infrastructure configurations, and employee-related information.
What the Threat Actor Claims
According to a post circulating on a hacker forum and the group’s official website, it alleges access to:
- Employee-related datasets
- Full source code (Java, Angular, Python)
- Secrets and access credentials (private keys, vault data)
- Cloud infrastructure configurations (AWS, Azure, Terraform)
and more…
The post includes references to downloadable archives in .tar.gz format and states a total data size of around 3GB. The hackers are attempting to sell the data to the highest bidder and have shared sample files to support their claims.
A screenshot with the post displays AstraZeneca branding and a message advertising the data, alongside a session ID for negotiation and a slogan referencing previous breach activity.
Analysis of the Leaked Samples
Hackread.com managed to review the sample data, which is divided into 3 main categories: GitHub-related data, third-party data, and financial data. Here are the details of what each category contains and whether the data appears authentic or fabricated.
1. GitHub Enterprise User Data
One sample file includes structured records resembling exports from a GitHub Enterprise environment. Fields include:
- Employee names
- Cost center references
- License types (Enterprise)
- Enterprise roles and permissions
- Two-factor authentication status
- GitHub usernames and profile URLs
- Organization roles (Owner, Member)
Assessment:
The data structure is consistent with what would be expected from real enterprise exports tied to GitHub or identity and access management systems. Its detailed role mappings throughout multiple internal organizations suggest visibility from inside a corporate environment rather than information gathered through public scraping.
The presence of numerous accounts with “Owner” privileges across several repositories also increases the stakes, because if authentic, that kind of access data would be highly sensitive. If genuine, this data could expose internal access hierarchies and enable targeted attacks.
2. Third-Party / Contractor Access Data
Another dataset appears to track access requests and onboarding for external collaborators, including:
- Internal user IDs
- Full names and email addresses
- Comments from internal teams
- Company affiliations (IQVIA, Parexel, Labcorp, etc.)
- Access status to internal systems (e.g., Confluence)
Assessment:
This data appears to be an internal access management or onboarding log, containing personally identifiable information along with details about organizational relationships. The inclusion of operational comments points to genuine internal workflow data rather than fabricated content.
Given the nature of the information, the risk level can be considered moderate to high, as exposure of contractor relationships and access systems could be used to support targeted social engineering campaigns.
3. Generic Financial Data
A third dataset contains high-level financial statistics labeled “All industries” with fields such as:
- Assets
- Salaries
- Total income
- Expenditure
Assessment:
This data appears to consist of public or generic statistical information rather than anything specific to AstraZeneca. It was likely included to increase the volume of the sample or distract from more relevant data. As such, it carries a low risk level, with no clear sensitivity or direct connection to AstraZeneca’s operations.
Sensitivity of the Alleged Data
| Data Type | Sensitivity | Impact |
|---|---|---|
| GitHub enterprise roles | High | Privilege escalation, internal mapping |
| Employee / contractor data | Moderate to High | Phishing, social engineering |
| Cloud infrastructure configs (claimed) | Critical | Full environment compromise |
| Generic financial data | Low | No direct risk |
If the claimed “secrets and access” data is real, that would represent the most severe risk, though no direct evidence of such material is present in the samples reviewed. However, attribution in cybercrime forums is unreliable, and the use of the name does not confirm the group’s involvement.
At the time of writing, these claims remain unverified. We have reached out to AstraZeneca for confirmation or comment. We will update this story if and when the company responds.