Hacker Interviews: TJ_Null

Source link
Related Articles
All Mix →Major improvement to web crawling, more customization, and new tests
Table of Contents More flexibility when viewing all of your assets Improved web application crawler now available Additional product updates: Recently added crowdsourced vulnerabilities More…
how I bruteforced my way into your Active Directory – honoki
Table of Contents The Target The Setup The Bugs The Exploit The Outcome Timeline Last May, I discovered that a critical vulnerability I had reported…
WordPress Plug-in Threatens 90,000+ websites
A highly concerning security loophole was recently discovered in a WordPress plugin called “Email Subscribers by Icegram Express,” a popular tool utilized by a vast…
The Top 5 Most Common Security Issues I Discover When Reviewing Code
Table of Contents 1. Sensitive Information in Log Files 2. Poor Cryptography Choices 3. Insufficient Access Controls 4. Unsecured Caches 5. Trusting the Client Too…
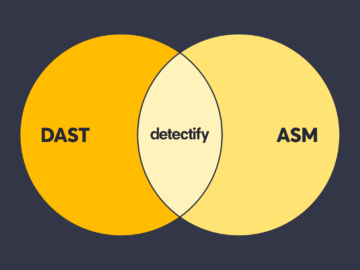
Embracing the best of both DAST and ASM
Table of Contents Differences between manual and automated security testing The history of DAST tools Surface Monitoring + Application Scanning = Best-in-class AST solution Surface…
Napkin Ideas Around What Changes to Expect Post-ChatGPT
Table of Contents 1. The startup engine is about to point its sights at human work Reviewing updates and looking for interesting nuggets or patterns…