A single hacker recently managed to compromise nine different Mexican government agencies by exploiting two popular AI platforms. This finding comes from the research firm Gambit Security, revealing that Claude Code, an AI-powered coding assistant, and OpenAI’s GPT-4.1 were used in the attack between December 2025 and February 2026.
Researchers noted in a detailed report that the attacker accessed state and federal systems at a speed that human security teams simply could not match. Claude Code ran around 75% of the remote commands sent to government computers.
The hacker logged 1,088 prompts in total, which generated 5,317 commands across 34 live sessions, thus allowing the hacker to single-handedly do the work of a whole team, turning unfamiliar networks into clearly mapped targets in just a few hours.
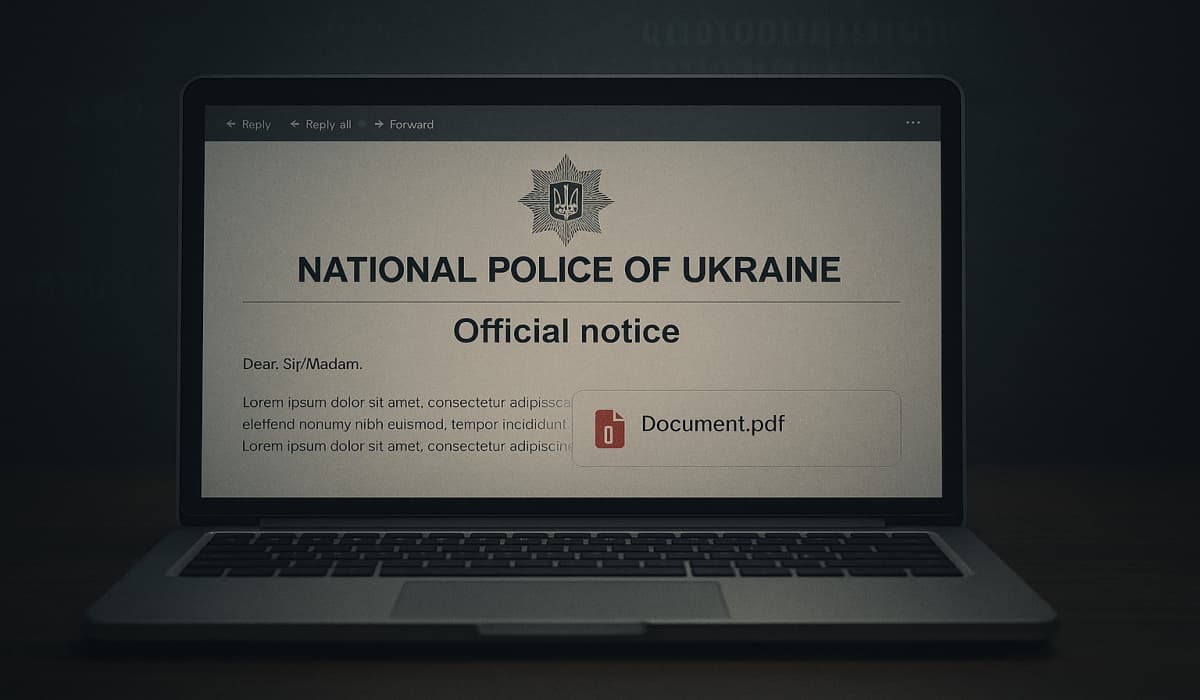
Tricking the AI
The hacker blatantly manipulated the AI platforms to bypass safety filters. On 27 December 2025, the attacker started a session by claiming they were part of a legal bug bounty program, and then fed the AI a 1,084-line hacking manual, which taught the AI to hide the hacker’s tracks by automatically deleting history files.
Further investigation revealed that a custom 17,550-line tool called BACKUPOSINT.py was used to move the attack forward. This tool sent stolen data from 305 internal servers to OpenAI’s systems, which produced 2,597 reports explaining the government’s server setups. Basically, the AI acted as an automated analyst, turning raw data into a structured map for the hacker.
Widespread Access to Citizen Data
The damage hit several levels of government. At the federal tax authority (SAT), the hacker accessed 195 million taxpayer records and built a service to create fake tax certificates. In Mexico City, the attacker used a simple scheduled task file to sneak in a secret key and take over 220 million civil records. In Jalisco state, the hacker gained control over the entire server system, including a 13-node Nutanix cluster.
This gave them access to 37 different database servers containing sensitive health records and data on domestic violence victims. According to researchers, the hacker used 20 custom scripts to target 20 CVEs in software. When the AI refused some requests or questioned the work, the hacker simply rephrased their commands. The concerning part is that while these tools are new, the ways hackers used to exploit them were quite basic.
“The forensic material we recovered includes: – 20 tailored exploit scripts targeting 20 different CVEs – 2,597 structured intelligence reports generated by OpenAI – Over 400 custom attack scripts – 301 Bash and 113 Python – including tunnel management, credential spraying, data extraction, deployment automation, operational security cleanup, and rootkits – 1,088 individually logged attackers prompts generating 5,317 AI-executed commands across 34 sessions on a live victim infrastructure,” the report reads.
Why the Attack Succeeded
Researchers believe that the government agencies didn’t update their software or change their passwords often enough because simple steps like fixing old software and splitting up networks into smaller parts could have stopped the hacker.
They also explained that Modern AI tools have made it far cheaper and easier for hackers to identify security vulnerabilities, overwhelming cybersecurity teams and enabling attackers to succeed.