A sophisticated way to bypass email security by weaponizing legitimate messages from trusted companies like Apple and PayPal.
These attacks, known as DKIM replay attacks, exploit email authentication systems to deliver scams that appear completely authentic.
The technique is deceptively simple. Attackers create accounts on platforms like Apple’s App Store or PayPal and manipulate user-controlled fields during setup.
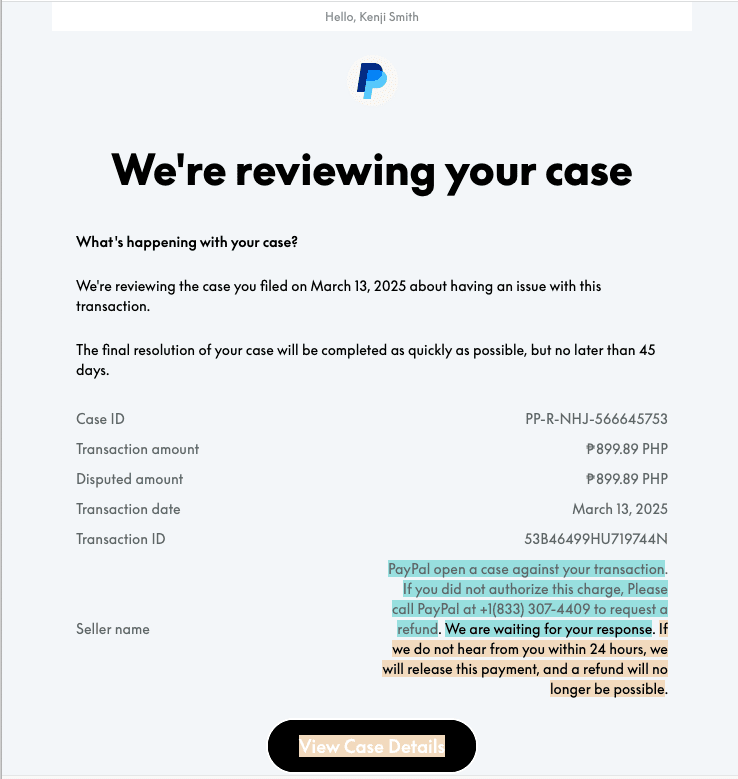
When signing up for an Apple subscription, they insert scam instructions such as “To cancel Call +1 (803) 745-3821” into the account name field. Similarly, on PayPal, they add malicious content to the “seller name” when creating invoices or disputes.
These platforms automatically generate confirmation emails containing the attacker’s inserted text and cryptographically sign them using DKIM (DomainKeys Identified Mail).
INKY has detected attacks in legitimate invoices and dispute notifications from well-known vendors, such as PayPal, Apple, DocuSign and HelloSign.
The attacker receives this legitimate email at their own address, then simply forwards it to victims. Because the original signature remains intact, the message passes all authentication checks including DKIM and DMARC (Domain-based Message Authentication, Reporting & Conformance).
Why Traditional Defenses Fail
Email security systems rely heavily on authentication signals to detect threats. When a message originates from apple.com or paypal.com with valid cryptographic signatures, security filters treat it as trustworthy.
The forwarding process breaks SPF (Sender Policy Framework) checks, but DMARC still passes because the aligned DKIM signature alone satisfies authentication requirements.
Since companies allow free-form text in certain fields, attackers embed scam content directly into legitimately signed messages.
This user-supplied content becomes part of the authenticated email body, making it virtually impossible for traditional filters to distinguish from genuine notifications.
Real-World Impact
INKY security researchers documented active campaigns abusing both Apple and PayPal emails.
Victims receive what appears to be a subscription confirmation from Apple or a dispute notice from PayPal, complete with proper logos, formatting and valid authentication.
The only red flag might be unusual wording like “Dear, To cancel Call…” followed by a phone number.
Unsuspecting users call the listed number, connecting directly with scammers who harvest payment details, personal information or convince victims to install remote-access malware.
The attacks succeed because recipients trust communications from recognizable brands, especially when their email systems confirm authenticity.
Organizations and individuals should inspect email headers carefully. Check if the “To:” address matches the intended recipient a mismatch indicates forwarding.
Be skeptical of any phone numbers in emails, as legitimate companies direct users to official websites rather than unsolicited calls.
DKIM replay attacks represent an evolving threat that turns trusted infrastructure against itself, requiring both technical controls and heightened awareness to combat effectively.
User education remains critical. Employees need to understand that authenticated emails from trusted domains can still contain malicious content inserted by attackers.
When receiving unexpected invoices or account notifications, users should navigate directly to official websites rather than responding to embedded links or phone numbers.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.