A new remote access trojan known as ResokerRAT has come to light, using Telegram’s bot API as its core communication channel to silently monitor and control infected Windows machines.
What makes this threat stand out is that it does not rely on a traditional command-and-control server.
Instead, it misuses a widely trusted messaging platform to receive attacker instructions and send stolen data back, making detection considerably more difficult for standard network security tools.
ResokerRAT is delivered as an executable file named Resoker.exe. Once a victim runs this file, the malware immediately starts working in the background, setting up persistence, requesting elevated privileges, and preparing to respond to remote commands.
.webp)
Its capabilities range from capturing screenshots and downloading additional files to disabling Windows security prompts and blocking user access to diagnostic tools like Task Manager.
K7 Security Labs analysts identified the malware and noted that one of its first actions upon execution is creating a mutex called “GlobalResokerSystemMutex” using the Windows CreateMutexW API.
.webp)
This mutex acts as a simple lock, ensuring only one instance of the malware runs on the system at a time. The malware also uses the IsDebuggerPresent function to check whether an analyst has attached a debugger to its process.
.webp)
If a debugger is found, the malware triggers a custom exception to interrupt any ongoing analysis.
To gain deeper access, the malware attempts to relaunch itself with administrator privileges using the ShellExecuteExA function with the “runas” option.
.webp)
If this elevation succeeds, the original instance shuts down and the elevated process takes over. Should it fail, the malware reports the error back through the Telegram bot.
It also scans running processes and forcibly terminates analysis tools like Taskmgr.exe, Procexp.exe, and ProcessHacker.exe using the TerminateProcess function.
Persistence and Remote Command Execution
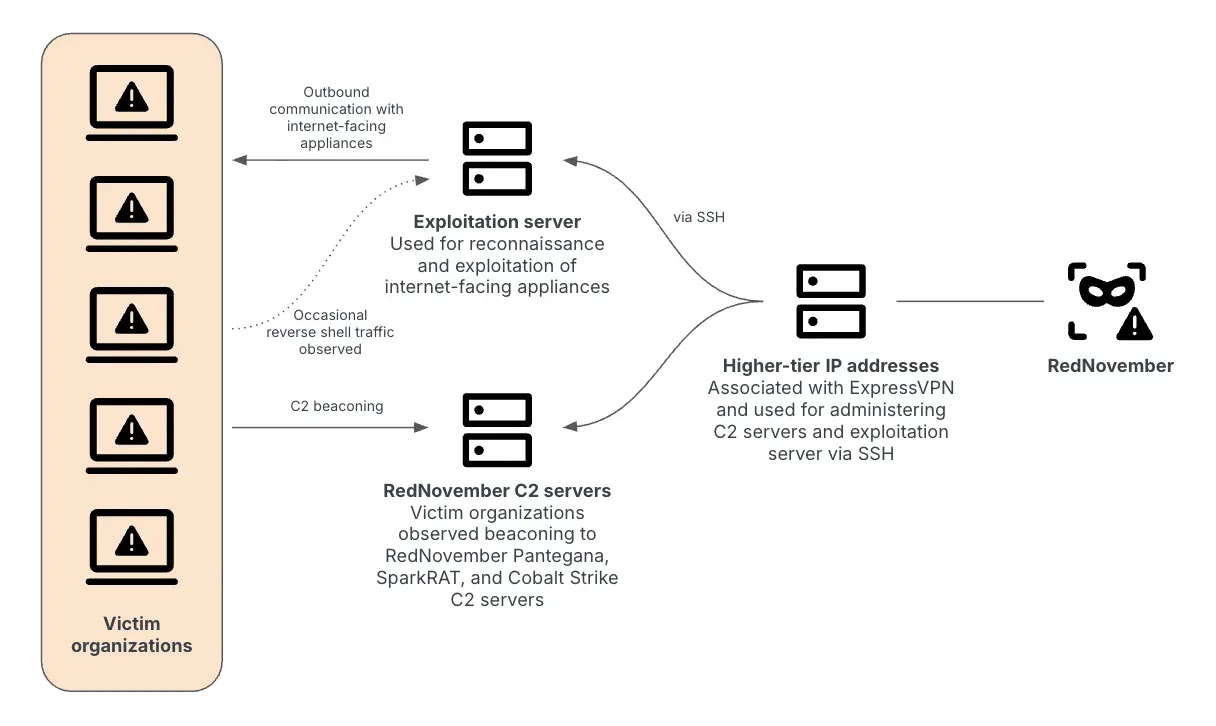
The most alarming aspect of ResokerRAT is how it permanently embeds itself into a system while using Telegram as its live control channel.
When the attacker sends the /startup command, the malware writes its executable path to the Windows registry under HKCUSoftwareMicrosoftWindowsCurrentVersionRun with the key name “Resoker”.
.webp)
This ensures the malware launches automatically every time the machine starts. A confirmation message reading “Added to startup” is then sent back to the attacker.
.webp)
Communication between the malware and the attacker flows entirely through the Telegram Bot API. The malware constructs a URL using a hardcoded bot token and chat ID to continuously poll Telegram for new instructions.
Before transmitting collected data, the malware encodes the content using URL encoding to help it pass through network filters without being flagged. This recurring traffic pattern was confirmed during network capture analysis.
.webp)
Among the available remote commands, the /screenshot command is particularly invasive. When issued, the malware creates a Screenshots folder in its local directory and runs a hidden PowerShell script to capture the full screen, saving it as a PNG file, all without showing any window to the user.
The attacker can also weaken system defenses using the /uac-min command, which sets ConsentPromptBehaviorAdmin to 0 and disables the secure desktop prompt, while keeping UAC appearing enabled to avoid raising suspicion.
Users and security teams are strongly advised to monitor the Windows Run registry key for unauthorized entries and watch for outbound HTTPS traffic directed to api.telegram.org from unknown processes.
Keeping systems and software up to date, avoiding executable files from untrusted sources, and staying alert to any sudden inability to open Task Manager are essential steps toward reducing the risk of infection.
Follow us on Google News, LinkedIn, and X to Get More Instant Updates, Set CSN as a Preferred Source in Google.