A severe scoping vulnerability was recently discovered in Microsoft Entra ID’s new Agent Identity Platform.
The security flaw allowed users assigned the Agent ID Administrator role to hijack arbitrary service principals across an organization’s tenant, leading to potential privilege escalation.
Although the administrative role was designed strictly to manage AI agent identities, a boundary breakdown allowed it to control non-agent service principals as well. Microsoft has fully patched the vulnerability across all cloud environments.
However, the incident highlights the ongoing risks of introducing new control planes built on existing directory primitives.
When an application is registered in Microsoft Entra ID, it creates a global application object and a local service principal.
The service principal acts as the localized identity that authenticates, receives role assignments, and accesses enterprise resources.
Microsoft Entra Agent ID is a preview feature that allows organizations to govern and secure AI agents by treating them as first-class identities. The platform introduces new directory objects, such as agent identities and blueprints.
Because these AI agent identities are technically implemented as specialized service principals, they share a common foundational infrastructure with standard enterprise applications.
To manage these new AI objects, Microsoft created the Agent ID Administrator role. The documentation stated that this role was restricted to agent-related objects. However, due to the shared underlying architecture between agents and applications, a critical scoping gap emerged.
Hackers Exploit Agent ID Administrator Role
Cybersecurity researchers from SilverFort found that accounts holding only the Agent ID Administrator role could exploit this scoping gap to take over any service principal.
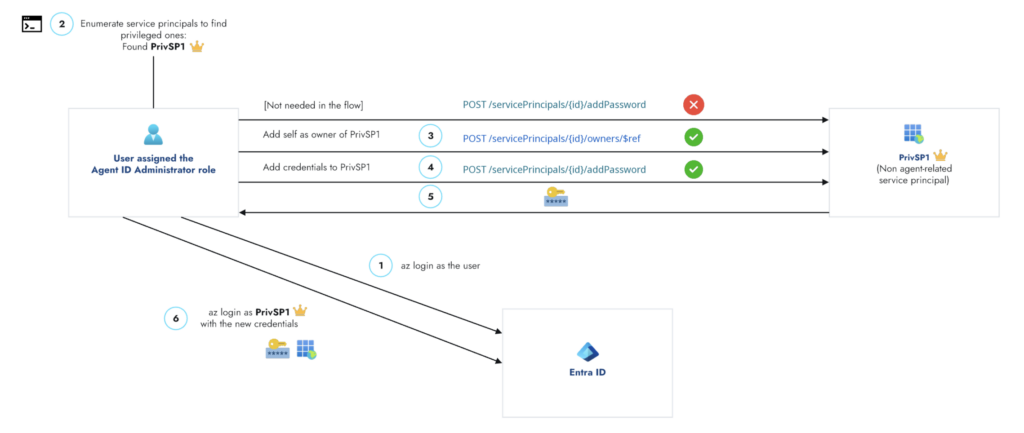
The attack flow executes through a simple but devastating takeover primitive:
- Assign Unauthorized Ownership: An attacker with the Agent ID Administrator role can force themselves as the owner of any service principal, bypassing intended agent-only restrictions.
- Generate New Credentials: Once ownership is established, the attacker can seamlessly attach a new secret or certificate to the targeted service principal.
- Authenticate and Hijack: The attacker uses the newly created credentials to authenticate as the hijacked service principal, gaining all of its associated access rights.
This process grants the attacker full control over the compromised application identity. Interestingly, the vulnerability was strictly limited to the service principal surface, as the system successfully blocked attempts to alter ownership on broader application objects maliciously.
The primary danger of this vulnerability lies in severe privilege escalation. Service principals frequently operate as the digital identities behind critical CI/CD pipelines, automated workflows, and high-level security tools.
If an attacker successfully hijacks a service principal that holds powerful Microsoft Graph permissions or administrative directory roles, they immediately inherit those elevated rights.
While the Agent ID Administrator role is relatively new, nearly all enterprise tenants utilize highly privileged service principals.
Furthermore, the Entra user interface failed to visually flag the Agent ID Administrator role as privileged, potentially misleading IT administrators into assigning it without adequate security scrutiny.
Following responsible disclosure in February 2026, Microsoft confirmed the flaw and successfully deployed a comprehensive fix by April 9, 2026.
The Agent ID Administrator role is now permanently blocked from modifying the owners of non-agent service principals.
To maintain robust security, organizations must actively monitor sensitive role usage and alert security teams to any unexpected changes in service principal ownership.
Privileged service principals must be treated as critical infrastructure and require continuous auditing of any newly created credentials.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.