A new wave of phishing campaigns where scammers are abusing Google’s legitimate infrastructure to bypass security filters.
Attackers are now creating free developer accounts on Google Firebase to send fraudulent emails that impersonate well-known brands.
By leveraging the reputation of the Firebase domain, these attackers are successfully landing in users’ inboxes, bypassing standard spam detection systems.
How the Attack Works
Google Firebase is a popular platform used by developers to build mobile and web applications.
It offers free accounts to help developers test their software. Unfortunately, scammers have realized that emails sent from these accounts originate from trusted Google servers.
In this campaign, attackers register free accounts and use them to broadcast phishing emails.
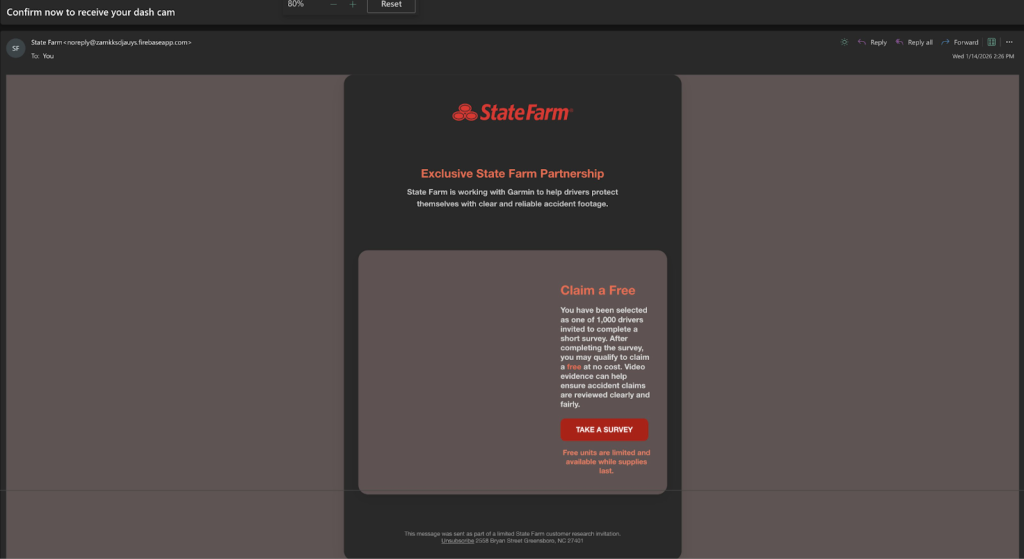
These messages typically come from addresses ending in firebaseapp.com. Because the emails are technically sent from a legitimate Google service, email security gateways often mark them as safe.
The campaigns rely on two primary psychological triggers: fear and greed.
- Scare Tactics: Many victims receive urgent alerts claiming that their bank accounts or online profiles have been compromised. These messages often warn of “fraudulent account use” and demand immediate action to prevent account lockout.
- Fake Giveaways: Other emails lure victims with the promise of free, high-value items. These fake promotions mimic popular retail brands, encouraging users to click links to claim a prize.
Once a user clicks a link in these emails, they are redirected to malicious websites designed to steal sensitive data, such as login credentials or credit card numbers, as reported PaloAlto Network.
Indicators of Compromise (IoCs)
Security teams should be on the lookout for specific patterns in email traffic.
The attackers often use randomly generated subdomains on the Firebase platform. Examples of sending addresses observed in this campaign include:
Furthermore, the links contained within these emails redirect to external phishing pages.
Researchers have identified several malicious URLs, including those hosted on clouud.thebatata[.]org and shortened links using rebrand[.]ly.
To stay safe, users should be skeptical of any unsolicited emails, even if they appear to come from a reputable technical domain like Firebase.
Always verify the sender’s address carefully. If an email claims to be from a bank or retailer but the address ends in firebaseapp.com, it is almost certainly a scam.
Network administrators are advised to monitor traffic for the identified domains and to consider blocking emails from unknown Firebase subdomains if their organization does not actively use them for development.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google