A new abuse campaign targeting AI-driven workflow automation platforms particularly n8n that turns legitimate automation tools into powerful malware delivery systems.
Between October 2025 and March 2026, security analysts observed a sharp surge in phishing emails that weaponized n8n-generated webhooks to deliver malicious payloads and collect device fingerprints under the guise of trusted infrastructure.
AI workflow platforms like n8n and Zapier are built to streamline tasks across applications such as Slack, Google Sheets, and Gmail, often integrating with LLMs like OpenAI’s GPT-4 or Anthropic’s Claude.
While these tools have become vital for automating business operations, they’ve also opened new attack surfaces.
Just as threat actors previously exploited platforms like Softr.io for phishing, n8n’s accessible webhook functionality now serves as an ideal conduit for stealthy malware campaigns.
Cisco Talos research has uncovered agentic AI workflow automation platform abuse in emails. n8n allows developers to host customizable workflows and APIs, often accessible through unique subdomains on the service (e.g., tti.app.n8n[.]cloud).
These URL-based webhooks are typically designed to receive and relay real-time data between applications.
When the URL receives a request, the subsequent workflow steps are triggered, returning results as an HTTP data stream to the requesting application.
Unfortunately, attackers now exploit this same functionality to disguise malware downloads and gathering mechanisms inside legitimate-looking traffic.
Webhooks as Stealth Malware
Talos detected a continuous rise in phishing emails embedding n8n-hosted webhook links up nearly 686% between January 2025 and March 2026.
Webhooks can dynamically serve different data streams based on triggering events such as request header information a phishing operator can tailor payloads based on the user-agent header.
Because webhooks obscure the source of delivered content, payloads appear to originate from the trusted n8n.io domain. The attackers further tailor these payloads dynamically using the victim’s browser or system data, allowing highly adaptive social engineering tactics.
One example involved phishing emails masquerading as shared Microsoft OneDrive folders. When recipients clicked the embedded webhook URL, a deceptive webpage appeared with a CAPTCHA verification screen.
After solving it, users unknowingly downloaded a malicious executable named “DownloadedOneDriveDocument.exe.”
This file deployed a modified version of the Datto Remote Monitoring and Management (RMM) tool, registering itself as a scheduled Windows task and connecting to Datto’s relay domain for persistent remote access.
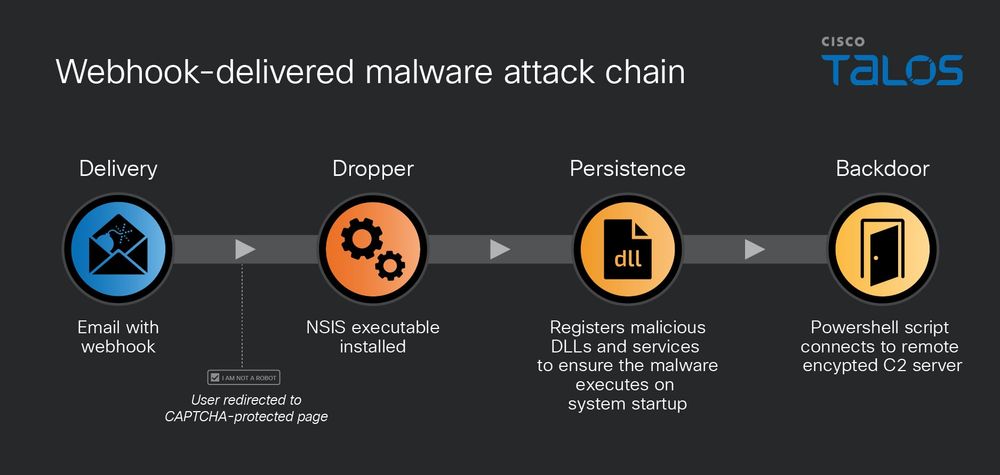
A second campaign followed a nearly identical pattern but dropped a weaponized MSI installer protected by the Armadillo packer.
The malware impersonated a OneDrive “Document Reader” and, when executed, installed a rogue version of the ITarian RMM agent.
During installation, it exfiltrated sensitive system data using Python modules, while showing users a fake progress bar designed to mimic a failed installation message.
Invisible Tracking Pixels
Beyond malware delivery, Talos also identified n8n abuse for device fingerprinting. In this method, attackers embed transparent or 1×1-pixel images within phishing emails.
When opened, the image forces an HTTP request to an n8n webhook URL containing unique identifiers such as the target’s email address or system metadata.
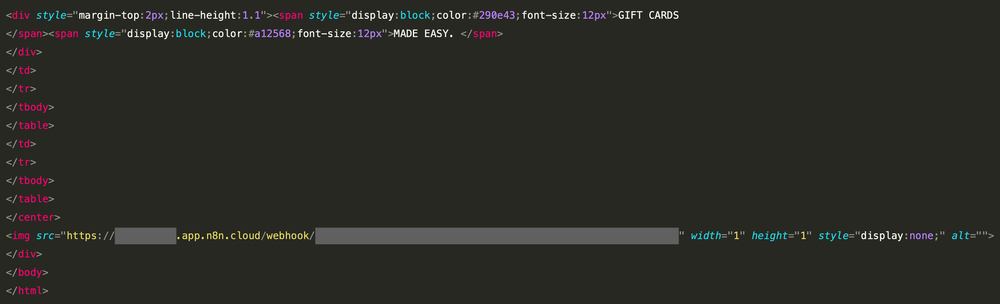
This simple yet effective approach allows adversaries to track when and where victims open their emails, profiling them for future exploitation.
These findings highlight how easily attackers repurpose legitimate AI automation platforms for malicious ends.
AI-driven automation should accelerate productivity not empower cyber threat actors. Security teams must now treat these platforms as both valuable assets and potential attack vectors.
As organizations increasingly integrate such tools into daily workflows, their trust-based infrastructure can be manipulated to evade detection and compromise systems at scale.
Cisco Talos urges defenders to monitor for unusual n8n or webhook-related traffic, enforce stricter email filtering, and educate users about malicious automation links.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.





