Hackers are abusing a critical React2Shell vulnerability in Next.js applications to run an automated credential‑theft operation that has already compromised at least 766 servers in under 24 hours.
The threat activity is tracked as “UAT‑10608”. It relies on a custom framework dubbed NEXUS Listener to systematically harvest and organize stolen secrets at scale.
Cisco Talos describes UAT‑10608 as a large‑scale, automated credential harvesting campaign targeting public‑facing Next.js applications vulnerable to CVE‑2025‑55182, commonly known as React2Shell.
By chaining this pre‑authentication remote code execution (RCE) vulnerability with scripted post‑exploitation tooling, the actors exfiltrate credentials, SSH keys, cloud tokens, and environment secrets with no further manual interaction after initial compromise.
Telemetry from an exposed NEXUS Listener instance shows at least 766 hosts compromised across multiple regions and cloud providers, with the tooling tuned for breadth rather than specific industries.
The targeting pattern is consistent with mass internet scanning using services like Shodan or Censys, as well as custom scanners, to discover and probe publicly reachable Next.js deployments.
React2Shell exploitation
React2Shell (CVE‑2025‑55182) is a CVSS 10.0 pre‑auth RCE in React Server Components (RSC) that also affects frameworks built on top of RSC, including Next.js.
The vulnerability arises from insecure deserialization of attacker‑controlled data sent to Server Function endpoints, allowing arbitrary code execution in the server‑side Node.js process before authentication or proper validation takes place.
In this campaign, UAT‑10608 first identifies a vulnerable internet‑facing application, then sends a crafted serialized payload directly to a Server Function endpoint to trigger the deserialization bug.
Successful exploitation results in the execution of a lightweight dropper, which in turn retrieves and launches a multi‑phase shell script without any need for valid credentials.
Post‑compromise, the attackers rely on nohup‑executed shell scripts placed in /tmp with randomized filenames, such as /bin/sh -c nohup sh /tmp/.eba9ee1e4.sh >/dev/null 2>&1, to persist and run the harvesting logic in the background.
The script moves through multiple phases, each focused on a particular data source: environment variables, JavaScript runtime configuration, SSH keys, token patterns, shell history, cloud metadata, Kubernetes service accounts, Docker environments, and running process arguments.
Execution state is tracked via a meta.json file, and after each phase completes, the tool phones home to the C2 over HTTP (typically port 8080), passing the victim hostname, current phase label, and a unique ID as URL parameters.
This design makes it easy for operators to monitor progress and correlate individual datasets back to specific hosts in the NEXUS Listener GUI.
NEXUS Listener and stolen data
Once uploaded, all collected files are stored in a backend database and surfaced through a password‑protected web interface called NEXUS Listener.
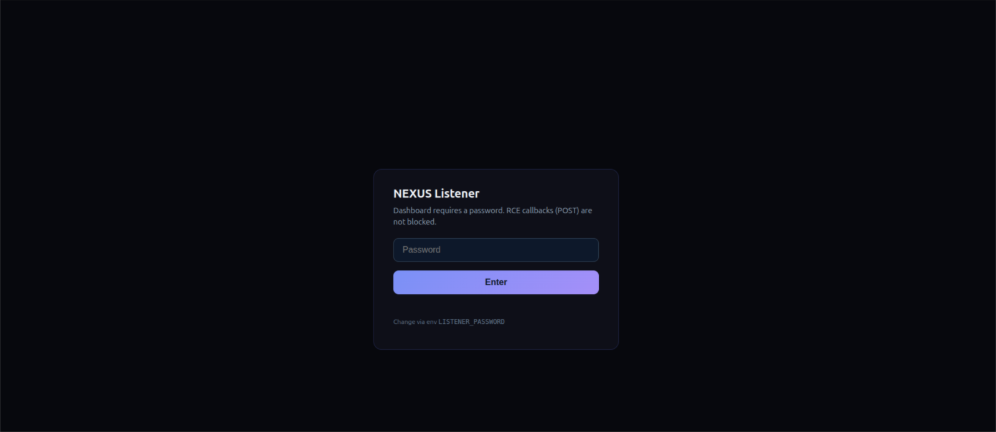
Data from that instance shows 10,120 files exfiltrated from 766 hosts, with roughly 91.5% of systems exposing database credentials and 78.2% leaking complete SSH private keys.
In at least one observed deployment, the interface was left exposed, allowing researchers to inspect both the application internals and live statistics on compromised hosts, harvested credential types, and application uptime.

Around 25.6% of hosts contained AWS credentials, 32% exposed shell command history, 11.4% had live Stripe API keys, and 8.6% leaked GitHub access tokens.
The interface, labeled as version “v3,” provides searchable access per host, broken down by the same phases used in the harvesting script.
The breadth of exposed data gives attackers everything from direct database access and cloud control‑plane operations to payment abuse, source‑code theft, and potential software supply‑chain attacks.
SSH key exposure, in particular, creates durable lateral‑movement paths that may outlive any immediate credential rotation if keys are reused across environments.
Aggregated at campaign scale, the dataset doubles as an intelligence map of victims’ infrastructure, simplifying follow‑on intrusions, social engineering, or resale of access to other threat actors.
Defenders should immediately patch React2Shell across all React Server Components and Next.js deployments and verify that no vulnerable versions remain exposed to the internet.
Cisco Talos and other vendors further urge teams to audit getServerSideProps and getStaticProps usage, enforce strict NEXT_PUBLIC_ environment‑variable discipline, rotate any potentially exposed secrets, harden cloud metadata access.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.