The open-source download management tool, JDownloader, website was recently targeted in a security incident involving the manipulation of the official download links to distribute malicious files. This was a kind of supply chain compromise because the hackers targeted the trusted source, the JDownloader website, to distribute malicious files through official-looking links.
The developers got alerted after users reported suspicious installer behaviour on Reddit, prompting them to take the server offline for emergency maintenance. This issue has been fixed now.
The Attack Vector
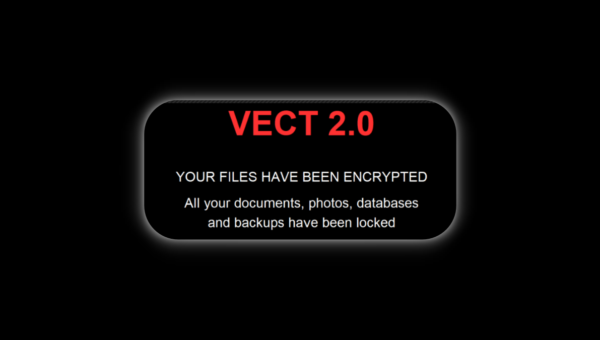
This compromise wasn’t a breach of JDownloader’s underlying server stack or host filesystem. According to the company’s official update, hackers exploited an unpatched security flaw in the website’s CMS (Content Management System), allowing them to modify access control lists (ACLs) without authentication. This helped them obtain the required permissions to edit web content and change download URLs.
The issue was identified on 7 May; however, as per the update, attackers first conducted a connectivity test on a low-traffic subsite on 5 May at 23:55 UTC. Then, on 6 May at 00:01 UTC, they updated the live links on the primary site. This manipulation, however, was limited to the Windows Alternative Installer and the Linux shell script.
The Linux shell script was altered to include harmful shell code, while the Windows files lacked proper digital signatures. AppWork GmbH always signs official JDownloader installers. The malicious versions either had no signature at all or showed unauthorised names like Zipline LLC or The Water Team. Another difference observed was that these files typically triggered Microsoft Defender or SmartScreen warnings during execution.
Current Status
The website was fully restored on 9 May after applying security patches and hardening the server configuration. JDownloader has confirmed that this incident didn’t affect existing installations or in-app updates because those channels utilize RSA-signed cryptographic verification that remained secure.
For users who executed these files on 6 and 7 May using Download Alternative Installer and/or the Linux shell installer link from this site, a standard antivirus scan may not be enough. As per the developers, mere scanning “cannot guarantee removal of every persistence mechanism” installed by the attackers. That’s why they recommend a complete reinstall of the OS to ensure the environment is secure.