Following the high-profile supply chain compromise of the widely used Axios package, a highly coordinated social engineering campaign has been uncovered targeting top-tier Node.js and npm maintainers.
Security researchers confirm that the Axios breach was part of a scalable operation aimed at infiltrating the global software supply chain.
The threat actors are actively hunting developers who hold write access to foundational open-source packages, turning trusted maintainers into distribution channels for malware.
The targeted individuals manage tools critical to modern software infrastructure, accumulating billions of downloads monthly.
Attackers recently attempted to compromise Socket CEO Feross Aboukhadijeh, Lodash creator John-David Dalton, and Fastify lead maintainer Matteo Collina.
Other prominent figures targeted include Scott Motte of the dotenv package, Node.js core collaborator Jean Burellier, and ecosystem contributors like Wes Todd and Pelle Wessman.
Aboukhadijeh warned the community that this type of persistent, targeted harassment against individual maintainers has become the new normal.
Rather than relying on simple phishing links, the threat actors execute a patient, weeks-long playbook designed to build genuine rapport.
The attackers typically initiate contact via LinkedIn or Slack, posing as legitimate recruiters, marketing agencies, or podcast hosts under fake company personas like “Openfort.”
They conduct themselves with professional corporate behavior, carefully scheduling and rescheduling video meetings to disarm their targets and establish a false sense of trust.
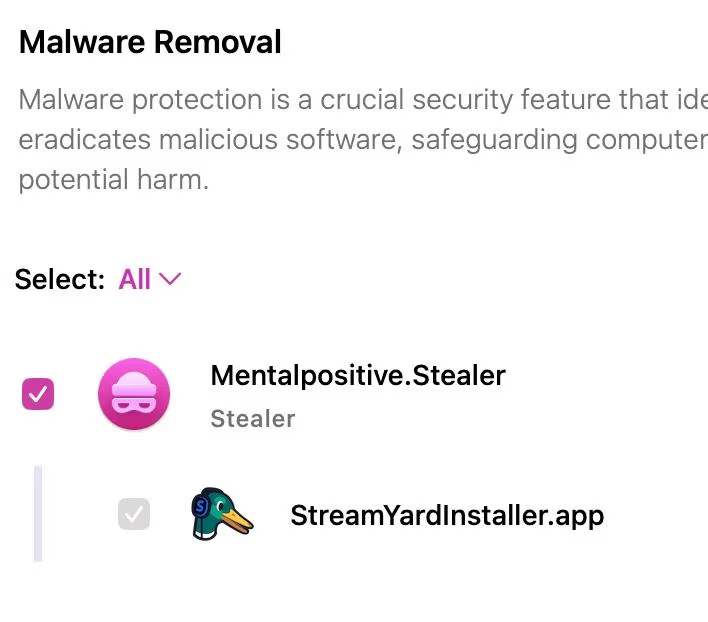
Once the maintainer agrees to a meeting, they are directed to a spoofed video conferencing platform designed to mimic Microsoft Teams or Streamyard.
Shortly after joining the call, the victim is presented with a technically plausible audio or video error message.
To resolve the fabricated issue, the site prompts the developer to either download a native application or execute a terminal command. If the victim complies, the payload silently installs a persistent Remote Access Trojan onto their machine.
This malware deployment is devastatingly effective because it completely bypasses standard security measures like two-factor authentication.
Security researcher Tay from Socket explained that the trojan immediately captures the victim’s post-authentication state.
By exfiltrating active browser session cookies, AWS credentials, and publishing tokens, the attackers gain immediate write access to the npm registry.
Developer Wes Todd cautioned that while OIDC-based publishing improves security hygiene, it provides a false sense of security against a fully compromised local machine.
Cybersecurity experts and organizations have linked these sophisticated operations to UNC1069, a suspected North Korean threat group.
Historically, UNC1069 spent years targeting cryptocurrency founders and venture capitalists to drain digital wallets using advanced malware.
However, their strategic pivot to open-source maintainers represents a severe escalation. By hijacking a developer’s npm publishing rights, the attackers can distribute malicious updates that are automatically ingested by millions of continuous integration pipelines worldwide.
The cybersecurity community is urging developers to remain highly vigilant and share their experiences without fear of embarrassment.
As threat actors continuously evolve their tactics to include platforms like Slack huddles and deploy AI-generated video personas, collective awareness remains the strongest defense.
A compromised developer machine is a direct attack on the millions of enterprise services that silently depend on their code.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.