Check your system for Axios npm Package versions 1.14.1 and 0.30.4 and remove them immediately to prevent data theft.
Modern web development relies heavily on shared libraries, and few are as critical as Axios, a tool that manages how applications talk to servers. On 31 March 2026, this trust was broken when a supply chain attack ‘poisoned’ the library. With Axios used in roughly 80% of cloud environments and seeing 100 million (101,032,032) weekly downloads, this is one of the most impactful npm compromises on record.
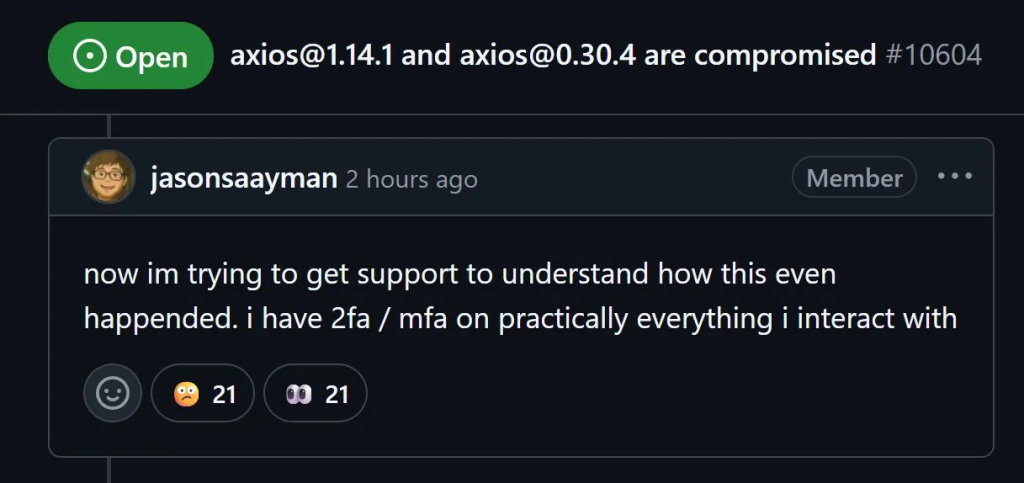
A Rapid-Fire Account Takeover
The breach began when a threat actor hijacked the GitHub and npm accounts of lead maintainer Jason Saayman. According to research by Socket and OpenSourceMalware, this allowed the attacker to bypass standard security checks like OIDC signing, which usually verify code as trusted.
By 00:21 UTC, the hacker published [email protected], followed by [email protected]. Both were pushed directly via a command-line interface rather than the official automated pipeline. The first infection was recorded just 89 seconds later. While collaborators like DigitalBrainJS rushed to alert the community, the attacker used stolen admin privileges to delete GitHub issues reporting the hack, playing a high-stakes cat-and-mouse game with security teams for over three hours.
According to blog posts from Socket and OpenSourceMalware researchers, the actual payload was hidden inside a fake dependency called plain-crypto-js. Staged 24 hours prior, this Trojan horse was designed to look like a standard encryption library. Once a developer installed the poisoned Axios, a script inside plain-crypto-js immediately went to work.
A separate research from Huntress reveals the malware’s advanced stealth. As a multi-platform Remote Access Trojan (RAT), it adapted to its environment: on Windows, it renamed itself wt.exe to mimic Windows Terminal; on Macs, it hid as com.apple.act.mond to look like a native system process. Once active, the malware performed a self-destruct sequence, deleting its own files to remove any evidence of the infection.
Spying and Data Theft
The consequences for infected machines are severe. The malware established a connection to a command-and-control server at sfrclak.com:8000, sending a heartbeat signal every 60 seconds. This beacon included a ‘fingerprint’ of the victim’s machine, including active processes and directory dumps of sensitive folders like .ssh, Documents, and OneDrive.
The attackers weren’t just looking for files; they were looking for a foothold. The RAT allowed them to remotely execute commands, inject new binaries, or capture cloud API tokens. This effectively gave hackers a remote-control window into any developer’s machine that ran a standard npm install during the three-hour compromise window.
What to Do If You’re Affected
If you performed a build or update between 00:21 and 03:40 UTC on 31 March, your system is likely at risk. Check your lockfiles for Axios versions 1.14.1 or 0.30.4 and the plain-crypto-js package.
Because the malware survives reboots and hides from basic antivirus, experts from all three firms recommend a ‘scorched earth’ approach. Do not attempt to patch the system; instead, wipe the machine completely, reinstall the OS, and immediately rotate every secret, key, and password stored on that device.