Security researchers are seeing threat actors switching to a new and open-source command and control (C2) framework known as Havoc as an alternative to paid options such as Cobalt Strike and Brute Ratel.
Among its most interesting capabilities, Havoc is cross-platform and it bypasses Microsoft Defender on up-to-date Windows 11 devices using sleep obfuscation, return address stack spoofing, and indirect syscalls.
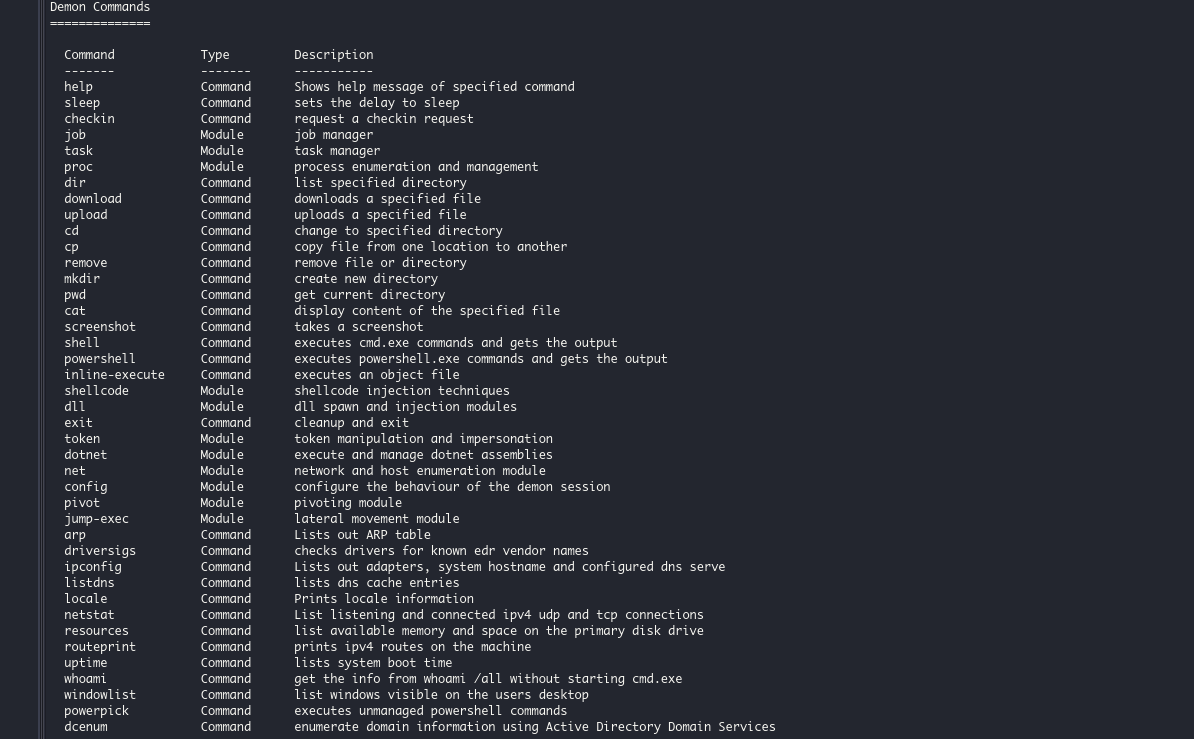
Like other exploitation kits, Havoc includes a wide variety of modules allowing pen testers (and hackers) to perform various tasks on exploited devices, including executing commands, managing processes, downloading additional payloads, manipulating Windows tokens, and executing shellcode.
All of this is done through a web-based management console, allowing the “attacker” to see all of their compromised devices, events, and output from tasks.
Havoc abused in attacks
An unknown threat group recently deployed this post-exploitation kit in early January as part of an attack campaign targeting an undisclosed government organization.
As the Zscaler ThreatLabz research team that spotted it in the wild observed, the shellcode loader dropped on compromised systems will disable the Event Tracing for Windows (ETW) and the final Havoc Demon payload is loaded without the DOS and NT headers, both to evade detection.
The framework was also deployed via a malicious npm package (Aabquerys) typosquatting legitimate module, as revealed in a report from ReversingLabs’ research team earlier this month.
“Demon.bin is a malicious agent with typical RAT (remote access trojan) functionalities that was generated using an open source, post-exploitation, command and control framework named Havoc,” ReversingLabs threat researcher Lucija Valentić said.
“It supports building malicious agents in several formats including Windows PE executable, PE DLL and shellcode.”
More Cobalt Strike alternatives deployed in the wild
While Cobalt Strike has become the most common tool used by various threat actors to drop “beacons” on their victims’ breached networks for later movement and delivery of additional malicious payloads, some of them have also recently begun looking for alternatives as defenders have gotten better at detecting and stopping their attacks.
As BleepingComputer previously reported, other options that help them evade antivirus and Endpoint Detection and Response (EDR) solutions include Brute Ratel and Sliver.
These two C2 frameworks have already been field tested by a wide range of threat groups, from financially motivated cybercrime gangs to state-backed hacking groups.
Brute Ratel, a post-exploitation toolkit developed by Mandiant and CrowdStrike ex-red teamer Chetan Nayak, has been used in attacks suspected to be linked to Russian-sponsored hacking group APT29 (aka CozyBear). At the same time, some Brute Ratel licenses have likely also landed in the hands of ex-Conti ransomware gang members.
In August 2022, Microsoft also noted that multiple threat actors, from state-sponsored groups to cybercrime gangs (APT29, FIN12, Bumblebee/Coldtrain), are now using the Go-based Sliver C2 framework developed by researchers at cybersecurity firm BishopFox in their attacks as an alternative to Cobalt Strike.






