Security researchers at EXPMON have uncovered a highly sophisticated, unpatched zero-day vulnerability actively targeting Adobe Reader users.
The exploit, first detected in the wild late last month, allows threat actors to silently steal local files, gather sensitive system information, and potentially deploy remote code execution (RCE) attacks against compromised machines.
According to the threat intelligence report published by EXPMON founder Haifei Li, the malicious PDF bypasses standard antivirus engines.
The file, originally named “yummy_adobe_exploit_uwu.pdf,” initially scored a low 5/64 detection rate on VirusTotal. The exploit has been verified to work on the latest version of Adobe Reader (26.00121367).
Alarmingly, the attack requires zero user interaction beyond simply opening the trapped PDF document.
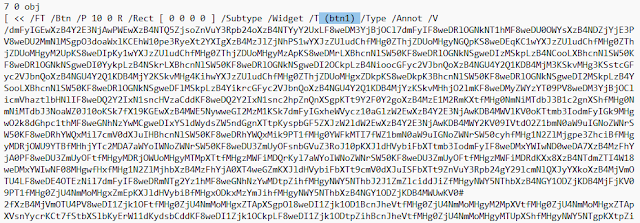
The attack relies on heavily obfuscated JavaScript hidden deep within the PDF’s objects that abuses two privileged Acrobat application programming interfaces (APIs):
- The exploit uses the
util.readFileIntoStream()API to read arbitrary files stored on the victim’s local system, such asntdll.dll, to calculate the exact operating system version. - The malware calls the
RSS.addFeed()API to exfiltrate this stolen data to a remote attacker-controlled server located at IP address169.40.2.68:45191.
Advanced Fingerprinting and Next-Stage Payloads
This zero-day functions primarily as an advanced fingerprinting tool. It acts as an initial scout, collecting environmental data such as language settings, Adobe Reader versions, and local file paths.
This profile is sent back to the attackers to determine if the compromised machine belongs to a high-value target.
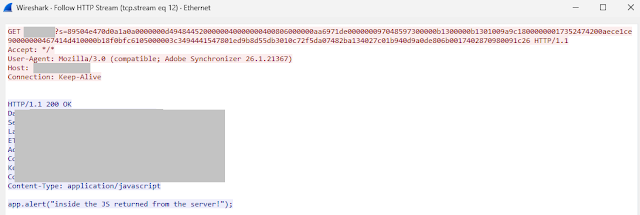
If the victim meets the attacker’s strict criteria, the command server uses the same RSS.addFeed() connection to deliver encrypted, secondary JavaScript payloads.
Researchers proved in a controlled environment that this channel can successfully execute remote code, paving the way for complete sandbox escape (SBX) exploits and total system takeover.
During real-world testing, the server connected but withheld the final payload, likely because the researchers’ test environment did not match the attackers’ specific target profile.
EXPMON has disclosed these findings to Adobe Security, but an official patch is not yet available. Until a fix is deployed, the security community must remain on high alert.
Network defenders are advised to block the known malicious IP address (169.40.2.68:45191).
Because threat actors can easily rotate their infrastructure, security teams should implement broader hunting rules.
Defenders should proactively monitor their environments for anomalous HTTP or HTTPS traffic containing “Adobe Synchronizer” in the User-Agent field.
Users are strongly urged to exercise extreme caution and avoid opening unsolicited PDF documents from unknown sources until Adobe issues a comprehensive security update.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.