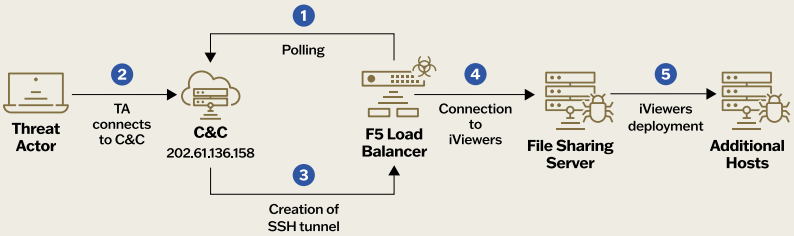
A group of suspected Chinese cyberespionage actors named ‘Velvet Ant’ are deploying custom malware on F5 BIG-IP appliances to gain a persistent connection to the internal network and steal data.
According to a Sygnia report who discovered the intrusion after they were called in to investigate the cyberattack, Velvet Ant established multiple footholds using various entry points across the network, including a legacy F5 BIG-IP appliance that served as an internal command and control (C2) server.
Using the compromised F5 BIG-IP devices, the threat actors could stealthily steal sensitive customer and financial information from the company for three years without being detected.
Using F5 BIG-IP malware in attacks
The attack observed by Sygnia started by compromising two outdated F5 BIG-IP appliances the victim organization used for firewall, WAF, load balancing, and local traffic management.
Both appliances were exposed online and were running vulnerable OS versions. Sygnia says they were both compromised using known remote code execution flaws to install custom malware on the networking devices.
Next, the attackers used this access to gain access to internal file servers where they deployed PlugX, a modular remote access Trojan (RAT), which various Chinese hackers have been using for data collection and exfiltration for over a decade now.
Other malware deployed on the F5 BIG-IP appliance includes:
- PMCD: Connects to the C&C server hourly, executes commands received from the server via ‘csh’, maintaining remote control.
- MCDP: Captures network packets, executed with the ‘mgmt’ NIC argument, ensuring persistent network monitoring.
- SAMRID (EarthWorm): An open-source SOCKS proxy tunneler used for creating secure tunnels, previously utilized by various Chinese state-sponsored groups.
- ESRDE: Similar to PMCD it uses ‘bash’ for command execution, allowing remote command control and persistence.
The attackers used the compromised F5 BIG-IP appliance to retain persistence on the network, allowing them to gain access to the internal network while blending attacker traffic with legitimate network traffic, making detection more difficult.
This method bypasses corporate firewalls and lifts outbound traffic restrictions, enabling attackers to steal customer and financial information without raising alarms for nearly three years.
Source: Sygnia
Sygnia reports that despite extensive eradication efforts following the breach’s discovery, the hackers re-deployed PlugX with new configurations to avoid detection, using compromised internal devices like the F5 appliances to retain access.
Defense recommendations
Counteracting sophisticated and persistent threat groups like Velvet Ant requires a multi-layered and holistic security approach.
Sygnia recommends the following measures to detect attacks like these:
- Restrict outbound connections to minimize C&C communications.
- Implement strict controls over management ports and enhance network segmentation.
- Prioritize replacing legacy systems and tightening security controls.
- Deploy robust EDR systems with anti-tampering features and enable security measures like Windows Credential Guard.
- Enhance security for edge devices through patch management, intrusion detection, and migration to cloud-based solutions.
As edge network devices do not commonly support security solutions and are meant to be exposed to the internet, they have become popular targets for threat actors to gain initial access to a network.
In 2023, China-linked hackers exploited Fortinet zero-days to install a custom implant to steal data and pivot to VMWare ESXi and vCenter servers.
Weeks later, a suspected Chinese hacking campaign targeted unpatched SonicWall Secure Mobile Access (SMA) appliances to install custom malware.
In April 2023, the US and UK warned that the Russian state-sponsored APT28 hackers were deploying a custom malware named ‘Jaguar Tooth’ on Cisco IOS routers.
In May 2023, Barracuda ESG devices were exploited for seven months to deploy custom malware and steal data. The compromise on these devices was so pervasive that Barracuda recommended that companies replace breached devices rather than try to restore them.
More recently, suspected state-sponsored threat actors exploited a Palo Alto Networks zero-day to install a custom backdoor to breach internal networks and steal data and credentials.