A newly exposed server has revealed how a threat actor used automated tools, AI assistance, and Telegram bots to silently hack into more than 900 companies around the world.
The operation, built around a tool called “Bissa scanner,” targeted internet-facing web applications at a massive scale, harvested sensitive credentials, and sent real-time exploit alerts straight to the attacker’s Telegram account.
The attack centered on a critical vulnerability in Next.js, tracked as CVE-2025-55182, which security researchers call React2Shell.
This flaw allowed attackers to target millions of web servers and pull out sensitive environment files (.env) that often contain passwords, API keys, and access tokens.
The threat actor did not just scan randomly; they built a structured workflow to find, exploit, and rank victims based on how valuable the stolen data could be. Financial firms, cryptocurrency platforms, and retail companies were among the hardest hit.
The DFIR Report analysts identified the full scope of this campaign after discovering an exposed server that held over 13,000 files spread across more than 150 directories.
Researchers noted that the contents were far from a simple data dump. Instead, the server showed a professionally organized operation with scripts for exploitation, victim-data staging, credential harvesting, and access validation all running in one place.
The exposed host also revealed that the operator used Claude Code and a tool called OpenClaw to assist with troubleshooting and workflow management, giving the attack a level of automation and efficiency rarely seen in mass exploitation campaigns.
What made this discovery especially significant was the operator’s use of Telegram as a live notification system. Runner scripts inside the Bissa scanner framework were hardcoded with a Telegram bot token linked to a bot called @bissapwned_bot.
Every time the scanner confirmed a successful React2Shell exploit, the bot sent a structured alert directly to the attacker’s private Telegram chat.
The operator, publicly identifiable by the Telegram username @BonJoviGoesHard and display name “Dr. Tube,” received one line per confirmed hit, each packed with the victim’s identity, cloud posture, privilege level, and available secrets.
This gave the attacker the ability to triage hundreds of breaches in near real time, right from a messaging app.
The credential haul was enormous. Across tens of thousands of .env files, the attacker collected keys and tokens for AI providers like Anthropic and OpenAI, cloud platforms including AWS and Azure, payment systems like Stripe and PayPal, and databases such as MongoDB and Supabase.
Between April 10 and April 21, 2026, the operator uploaded over 65,000 archived file entries to a cloud storage bucket called “bissapromax” using S3-compatible Filebase, showing just how automated and continuous the collection pipeline was.
How the Telegram Bot Notification System Worked
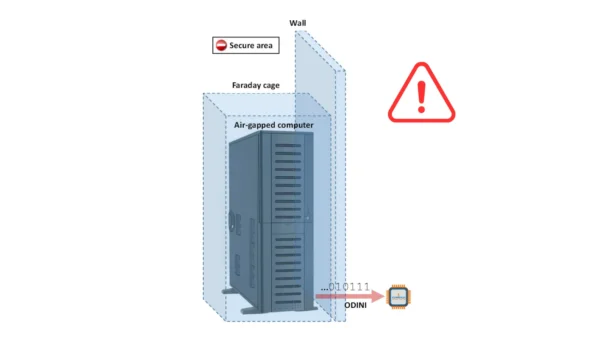
The Telegram alerting setup was one of the most technically revealing parts of this entire campaign. Each confirmation message sent by @bissapwned_bot carried a structured header with a message ID, date, sender username, and bot user ID.
The body of the message was written as a single line using emoji-delimited fields, which gave the attacker an instant summary of each victim without needing to log into the server manually.
This design choice shows a clear operational maturity: the attacker wanted speed, clarity, and minimal effort when reviewing results.
The DFIR Report analysts found that the operator ran at least two separate bots: @bissapwned_bot for scanner alerting and @bissa_scan_bot within the AI-control subsystem powered by OpenClaw.
Metadata lookups against the Telegram API confirmed both bots remained active at the time of discovery.
The destination chat resolved to a private conversation between the bot and a single human operator, confirming that this was a solo-run, centrally managed campaign.
This level of infrastructure investment points to an attacker who had been running this type of operation for a long time, with storage phase names tracing back to September 2025.
.webp)
This illustration showing how @bissapwned_bot delivered real-time exploit notifications to the operator’s Telegram chat for each confirmed CVE-2025-55182 hit.
The DFIR Report researchers noted several strong defensive measures organizations should apply right away. First, patch aggressively and stay subscribed to vendor advisories so critical CVEs do not go unnoticed until an incident occurs.
Second, move production credentials out of .env files and into a proper secret manager, injecting them at runtime with short lifetimes and narrow permissions.
Third, organizations should control outbound traffic from application tiers through a logged proxy to prevent compromised hosts from quietly reaching attacker infrastructure.
Finally, rotate credentials on a regular schedule, scan code and built artifacts for embedded secrets, and plant canary tokens that trigger an alert the moment they are accessed by an unauthorized party.
Follow us on Google News, LinkedIn, and X to Get More Instant Updates, Set CSN as a Preferred Source in Google.