
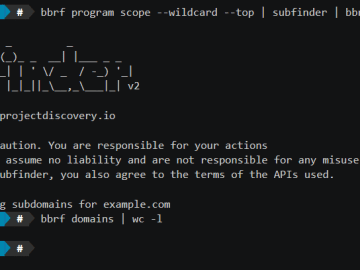
🎙️ Hacking, Open Source and Bug Bounty (Live Podcast) #2

Source link
Related Articles
All Mix →Digg and Reddit: Please Learn The Difference Between Original Content and Blogspam
Nothing is worse for systems like Digg and Reddit than repetitive, mediocre content. These networks are designed to magnify the efficiency of the Internet by…
yet another Bug Bounty Reconnaissance Framework – honoki
Table of Contents Get started What’s the problem? Architecture Document store Client Features Programs & Scopes Collaboration & Distribution Extensibility AWS Lambda (aka Cloud Magic)…
Kristian Bremberg, Detectify Crowdsource community manager: “Crowdsourced security gives researchers freedom”
The Detectify Crowdsource platform allows security researchers to submit newly discovered exploits and incorporate them into Detectify’s automated security service. At the heart of the…
XSS via reportError
Table of Contents What is reportError Analysis reportError for XSS Uncaught Message Conclusion References reportError란 함수를 아시나요? Chrome 95, Firefox 93 버전에 추가된 글로벌 메소드로…
Revisiting the AI Bubble | Daniel Miessler
I did a short post (and a video) about how AI shouldn’t be thought of as a bubble because a bubble is a false belief…
[tl;dr sec] #277 – Cybersecurity (Anti)Patterns, $64K from Deleted Files, New from Meta AI Security
Table of Contents How to avoid Busywork Generators, bug bounty story of secrets in deleted files, new AI security tools and evals from Meta Almost……




![[tl;dr sec] #277 - Cybersecurity (Anti)Patterns, $64K from Deleted Files, New from Meta AI Security](https://image.cybernoz.com/wp-content/uploads/2025/05/tldr-sec-277-Cybersecurity-AntiPatterns-64K-from-Deleted-Files.png)