🎙️ Hacking, Open Source and Bug Bounty (Live Podcast) #3

Source link
Related Articles
All Mix →HOW DID THIS HAPPEN!? (13370822 LHE VLOG)
HOW DID THIS HAPPEN!? (13370822 LHE VLOG) Source link
A GTD Approach to Organizing and Reading Your Feeds
The fundamental problem when managing feeds is input management. Most of us simply have too many feeds to read in a single sitting. How can…
Meet the Hacker: Peter Jaric, Software Developer: “I got two board games for the first bug I reported”
Table of Contents What are your experiences with bug bounty and responsible disclosure programs? In your opinion, what differs Detectify’s Crowdsource from other bug bounty…
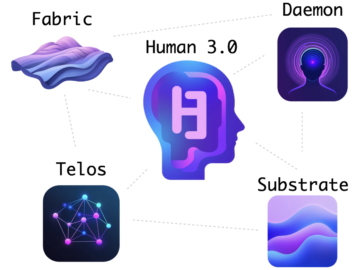
How My Projects Fit Together
Table of Contents Table of Contents The Problem(s) Security forever The Major Projects Substrate Fabric Telos Daemon Human 3.0 Component Summary Summary When people look…
Launching the Hacker Calendar, Never Miss a Challenge Again
HackerOne has a long history of running Hack Days. You might still remember our recent hack day where we launched the HackerOne Alexa Skill. Earlier…
Replacing Cursor With Neovim and Claude Code
Table of Contents Ghostty to the rescue The Ghostty Keybindings The result My three-paned Ghostty / Neovim / Claude Code Setup (click for full size)…