HackTheBox – Monstrosity Walkthrough (Live)

Source link
Related Articles
All Mix →How Hacker-Powered Security Can Help Security Teams Become More Data-Driven
Challenges for Traditional Security Teams Traditional security teams are typically reactive. They’re seen as change-resistant, out of sync with development, and unable to predict or…
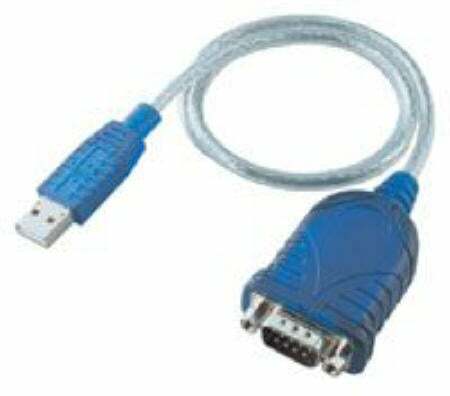
How to Manage a Cisco Device via Console Using a USB Port in OS X
Table of Contents Step 1: Procure a USB to Console Cable Step 2: Download and Install the Driver Step 3: Find the Port On Your…
Hive Five 204 – Make Change That Lasts
Table of Contents The Bee's Knees Hive Store: For Hackers By Hackers Table of Contents Updates Work Level up Explore Learned something? As 2024 comes…
Security: How To Monitor Your Network Connections
One of the most important concepts in computer security is “knowing thy system”. This essentially means that in order to be able to protect something…
US Government Mandates Vulnerability Disclosure for IoT
This year has seen a rapid acceleration in the American government’s efforts to secure federal and state cyber infrastructure. This momentum has continued with the…
Gentoo vs. Debian | Daniel Miessler
[ August 2006 ] I’ve been playing with Linux since 1999 and using it steadily in one capacity or another since 2001. I’ve tinkered with…