An Iranian threat actor known as Handala Hack has carried out a series of destructive cyberattacks against organizations in Israel, Albania, and the United States, using remote desktop access, network tunneling, and multiple simultaneous data-wiping tools.
The group operates under the broader identity of Void Manticore, also tracked as Red Sandstorm and Banished Kitten, and is directly linked to Iran’s Ministry of Intelligence and Security (MOIS).
Its attacks are not about espionage — they are specifically built to destroy data and make recovery nearly impossible.
Handala Hack draws its name from the well-known Palestinian cartoon character Handala and has been active since late 2023. The group maintains three public-facing personas: Handala Hack, Karma, and Homeland Justice.
Homeland Justice has been used since mid-2022 to target government agencies, telecom providers, and other sectors in Albania, while Karma appears to have been phased out and replaced by Handala over time.
In recent operations, the group extended its reach to the United States, striking organizations including medical technology firm Stryker.
%20-%20Homeland%20Justice,%20Handala%20and%20Karma%20(Source%20-%20Check%20Point).webp)
Check Point researchers identified the group’s evolving attack patterns across multiple intrusions and found that while its core methods have stayed consistent since 2024, several new techniques have begun appearing in recent campaigns.
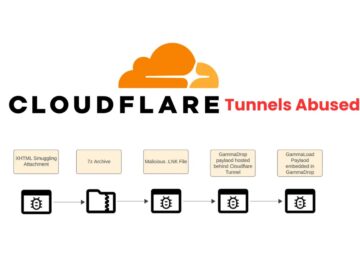
These include NetBird, a legitimate peer-to-peer networking tool used to tunnel traffic inside victim networks, and an AI-assisted PowerShell script deployed as part of its wiping toolkit.
The researchers also noted a clear drop in the group’s operational discipline, with activity traced directly to Iranian IP addresses rather than the commercial VPN services it previously relied on.
The attack chain typically begins with compromised VPN credentials, obtained through brute-force attempts or supply chain breaches against IT service providers.
Once inside, the attackers rely on Remote Desktop Protocol (RDP) to navigate between systems manually before triggering destruction.
At least five attacker-controlled machines were observed operating simultaneously within a single victim environment, reflecting the group’s intent to cause damage as fast and as broadly as possible.
.webp)
What sets Handala apart is its drive to destroy data from several angles at once, giving organizations almost no chance of meaningful recovery.
The group achieves this by deploying multiple wipers simultaneously through Group Policy, ensuring rapid spread across the network.
Parallel Wiping Operations: A Multi-Layer Approach to Destruction
The destructive phase of a Handala intrusion runs four separate wiping techniques at the same time. The first is the custom Handala Wiper, distributed via Group Policy logon scripts through a batch file named handala.bat.
This wiper overwrites file contents and applies Master Boot Record (MBR) corruption for deep, low-level damage.
Since the executable runs remotely from the Domain Controller and is never written to disk on targeted machines, it is harder for security tools to detect.
.webp)
Alongside this, the attackers use an AI-assisted PowerShell wiper that removes all files from user directories and then floods every logical drive with a propaganda image named handala.gif.
The group also downloads VeraCrypt, a legitimate encryption utility, directly through the victim’s own browser to lock drives and prevent data recovery.
As a final step, operators manually delete virtual machines and individual files over RDP, a behavior the group has documented in its own leaked videos.
Defenders should enforce multi-factor authentication on all remote access and privileged accounts without exception. Security teams should watch for logins from unfamiliar countries, unusual hours, new device registrations, and abnormal VPN data transfers.
Connections from Iranian IP addresses and known Starlink IP ranges should be blocked at the perimeter. RDP access must be disabled where not needed, especially on machines carrying default Windows naming formats such as DESKTOP-XXXXXX or WIN-XXXXXX.
Teams should also monitor closely for tools like NetBird and other tunneling utilities, as their presence may indicate unauthorized internal network activity.
Follow us on Google News, LinkedIn, and X to Get More Instant Updates, Set CSN as a Preferred Source in Google.