Handala Hack is an Iranian state-linked destructive actor that combines old-school RDP-heavy intrusions with new tools like NetBird and AI-assisted wipers to devastate victim networks rapidly.
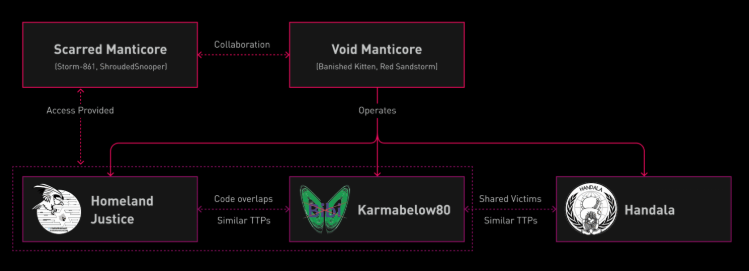
Handala Hack is an online persona operated by Void Manticore (also tracked as Red Sandstorm and Banished Kitten), a threat actor affiliated with Iran’s Ministry of Intelligence and Security (MOIS).
Additional personas linked to this cluster include Karma and Homeland Justice, which have been used in campaigns against targets in Israel and Albania.
Public reporting ties Void Manticore to MOIS’s Internal Security Deputy and its Counter-Terrorism Division, whose leadership was reportedly impacted in recent Israeli strikes on Iranian intelligence figures.
Since late 2023, Handala has emerged as the dominant public-facing persona, effectively replacing Karma in most operations while Homeland Justice remains active in Albanian-focused campaigns.
Handala Hack, also tracked by Check Point Research as Void Manticore, is an Iranian threat actor that is known for multiple destructive wiping attacks combined with “hack and leak” operations.
Intrusions attributed to all three personas show highly similar TTPs and overlapping wiper code, suggesting closely coordinated teams or a gradual consolidation under the Handala brand.
Initial Access and Pre-Impact Activity
Void Manticore continues to favor compromised VPN credentials for initial access, frequently obtained through targeting IT and service providers to harvest accounts with broad downstream reach.
Analysts have observed hundreds of logon and brute-force attempts against organizational VPN infrastructures, often originating from commercial VPN nodes and hosts using default Windows naming patterns (DESKTOP-XXXXXX or WIN-XXXXXXXX).
Following a nationwide internet shutdown in Iran, Handala activity was also seen routing through Starlink IP ranges, alongside a growing number of direct connections from Iranian IP space as operational security degraded.
In a recent intrusion, the group maintained long-term access for months before the destructive phase, using that dwell time to secure Domain Administrator credentials.
Shortly before impact, the actor disabled Windows Defender performed extensive reconnaissance and credential theft (including LSASS dumping and registry hive exports), and executed ADRecon to map Active Directory, likely finalizing its privilege escalation path for the subsequent wiper deployment.
Handala’s operations remain heavily manual, with lateral movement primarily conducted over RDP sessions between compromised systems.
To reach internal hosts that are not directly exposed, operators manually deploy NetBird, a legitimate zero-trust mesh networking platform, by logging in via RDP and downloading it from the official site using the victim’s browser.
Installing NetBird on multiple machines allows attackers to tunnel traffic within the network and coordinate activity from several footholds at once; in at least one case, five attacker-controlled systems operated in parallel inside a single environment to accelerate the destructive phase.
This blend of RDP and ad hoc mesh networking reflects the group’s preference for straightforward tools that are easy to operationalize, while still complicating defenders’ efforts to trace lateral movement paths.
Parallel Wipers and Destruction
During destructive operations, Handala employs multiple wiping methods simultaneously, distributed at scale via Group Policy to maximize impact.
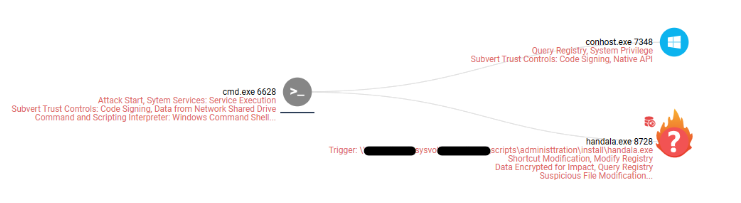
The first component is a custom executable dubbed Handala Wiper (e.g., handala.exe), executed as a scheduled task through logon scripts that trigger both the binary and an associated batch file; the malware overwrites file contents and uses MBR-level wiping techniques to corrupt system disks and cause extensive data loss.
In parallel, a custom PowerShell-based wiper enumerates files in user directories and deletes them en masse, with its structure and verbose comments suggesting AI-assisted development; it also drops a propaganda image (handala.gif) across logical drives to mark the intrusion.
Beyond bespoke wipers, the group abuses VeraCrypt, a legitimate disk encryption tool, downloaded interactively via RDP to encrypt system drives as an additional destructive layer that complicates recovery.
In some incidents, operators also manually delete virtual machines and files directly from hypervisor consoles or Windows Explorer, reflecting their hands-on approach and willingness to perform low-tech but highly impactful actions when time permits.
Defenders should prioritize strong authentication for remote access, focusing on enforcing MFA for VPN and privileged accounts and monitoring for unusual login patterns, such as access from new countries, hosting providers, or Starlink ranges.
Restricting and hardening RDP exposure, tightly controlling the use of VPN and mesh networking tools like NetBird, and watching for sudden Group Policy changes or PowerShell-based file deletion at scale are key to detecting and disrupting Handala-style operations before the wiping phase begins.
IOCs
| Type | IOC |
| Handala Wiper | 5986ab04dd6b3d259935249741d3eff2 |
| Handala Powershell Wiper | 3cb9dea916432ffb8784ac36d1f2d3cd |
| VeraCrypt Installer | 3236facc7a30df4ba4e57fddfba41ec5 |
| NetBird Installer | 3dfb151d082df7937b01e2bb6030fe4a |
| NetBird | e035c858c1969cffc1a4978b86e90a30 |
| Handala VPS | 82.25.35[.]25 |
| Handala VPS | 31.57.35[.]223 |
| Handala VPS | 107.189.19[.]52 |
| VPN exit node used by Handala | 146.185.219[.]235 |
| Starlink IP range used by Handala | 188.92.255.X |
| Starlink IP range used by Handala | 209.198.131.X |
| Commercial VPN IP range used by Handala | 149.88.26.X |
| Commercial VPN IP range used by Handala | 169.150.227.X |
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.